redsocks
This tool allows you to redirect any TCP connection to SOCKS or HTTPS proxy using your firewall, so redirection is system-wide.
Why is that useful? I can suggest following reasons:
* you use tor and don’t want any TCP connection to leak.
* you use DVB ISP and this ISP provides internet connectivity with some special daemon that may be also called “Internet accelerator” and this accelerator acts as proxy. Globax is example of such an accelerator.
Linux/iptables, OpenBSD/pf and FreeBSD/ipfw are supported.
Linux/iptables is well-tested, other implementations may have bugs,
your bugreports are welcome.
Transocks is alike project but it has noticable performance penality.
Transsocks_ev is alike project too, but it has no HTTPS-proxy support
and does not support authentication.
Several Android apps also use redsocks under-the-hood: ProxyDroid and
sshtunnel. And that’s over 100’000 downloads! Wow!
Features
========
- Redirect any TCP connection to SOCKS4, SOCKS5 or HTTPS (HTTP/CONNECT) proxy server.
- Login/password authentication is supported for SOCKS5/HTTPS connections. SOCKS4 supports only username, password is ignored. for HTTPS, currently only Basic and Digest scheme is supported.
- Redirect UDP packets via SOCKS5 proxy server. NB: UDP still goes via UDP, so you can’t relay UDP via OpenSSH.
- Sends “truncated reply” as an answer to UDP DNS queries.
- Redirect any HTTP connection to proxy that does not support transparent proxying (e.g. old SQUID had broken `acl myport’ for such connections).
Installation
git clone https://github.com/darkk/redsocks.git
cd redsocks
make
Usage
Running
=======
Program has following command-line options:
-c sets proper path to config file ("./redsocks.conf" is default one)
-t tests config file syntax
-p set a file to write the getpid() into
Following signals are understood:
SIGUSR1 dumps list of connected clients to log
SIGTERM and SIGINT terminates daemon, all active connections are closed
You can see configuration file example in redsocks.conf.example
iptables example
================
You have to build iptables with connection tracking and REDIRECT target.
# Create new chain
root# iptables -t nat -N REDSOCKS
# Ignore LANs and some other reserved addresses.
# See http://en.wikipedia.org/wiki/Reserved_IP_addresses#Reserved_IPv4_addresses
# and http://tools.ietf.org/html/rfc5735 for full list of reserved networks.
root# iptables -t nat -A REDSOCKS -d 0.0.0.0/8 -j RETURN
root# iptables -t nat -A REDSOCKS -d 10.0.0.0/8 -j RETURN
root# iptables -t nat -A REDSOCKS -d 127.0.0.0/8 -j RETURN
root# iptables -t nat -A REDSOCKS -d 169.254.0.0/16 -j RETURN
root# iptables -t nat -A REDSOCKS -d 172.16.0.0/12 -j RETURN
root# iptables -t nat -A REDSOCKS -d 192.168.0.0/16 -j RETURN
root# iptables -t nat -A REDSOCKS -d 224.0.0.0/4 -j RETURN
root# iptables -t nat -A REDSOCKS -d 240.0.0.0/4 -j RETURN
# Anything else should be redirected to port 12345
root# iptables -t nat -A REDSOCKS -p tcp -j REDIRECT --to-ports 12345
# Any tcp connection made by `luser' should be redirected.
root# iptables -t nat -A OUTPUT -p tcp -m owner --uid-owner luser -j REDSOCKS
# You can also control that in more precise way using `gid-owner` from
# iptables.
root# groupadd socksified
root# usermod --append --groups socksified luser
root# iptables -t nat -A OUTPUT -p tcp -m owner --gid-owner socksified -j REDSOCKS
# Now you can launch your specific application with GID `socksified` and it
# will be... socksified. See following commands (numbers may vary).
# Note: you may have to relogin to apply `usermod` changes.
luser$ id
uid=1000(luser) gid=1000(luser) groups=1000(luser),1001(socksified)
luser$ sg socksified -c id
uid=1000(luser) gid=1001(socksified) groups=1000(luser),1001(socksified)
luser$ sg socksified -c "firefox"
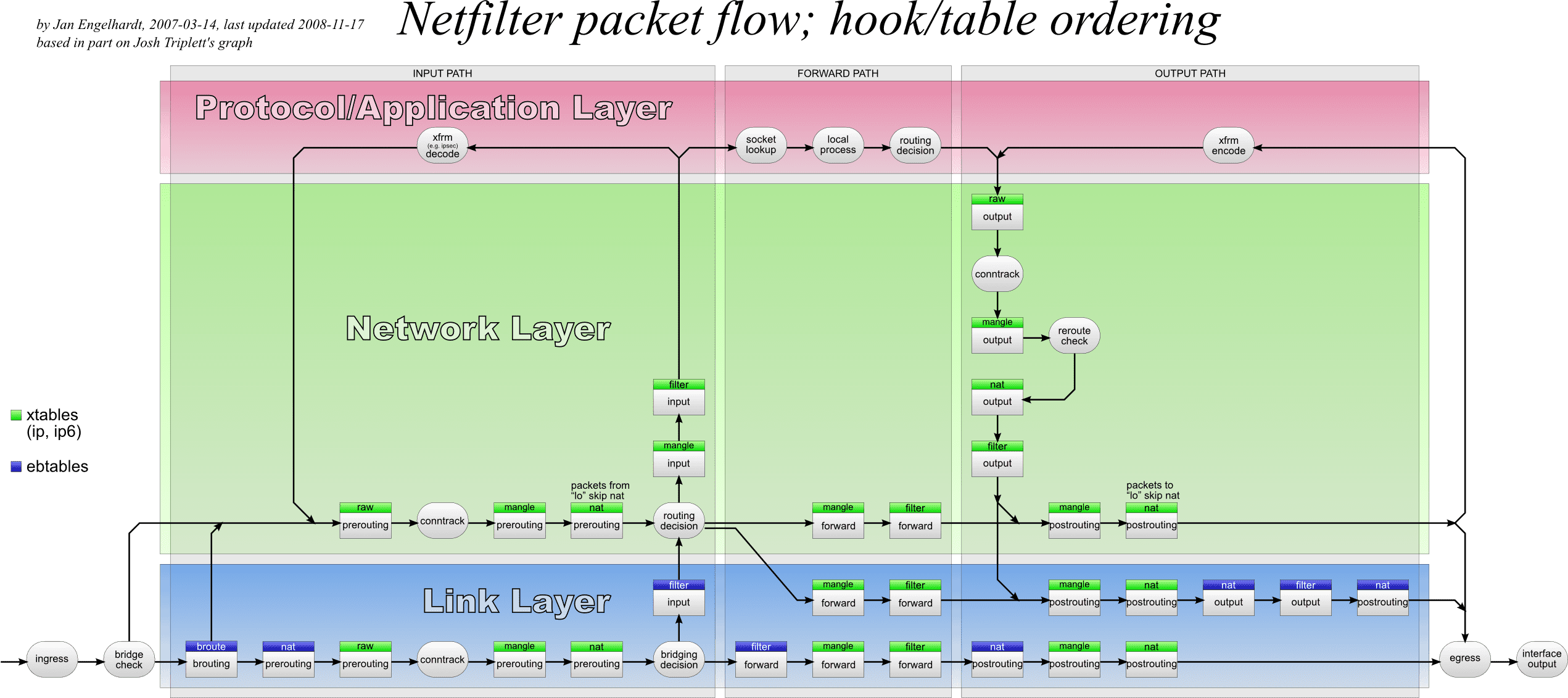
# If you want to configure socksifying router, you should look at
# doc/iptables-packet-flow.png, doc/iptables-packet-flow-ng.png and
# https://en.wikipedia.org/wiki/File:Netfilter-packet-flow.svg
# Note, you should have proper `local_ip' value to get external packets with
# redsocks, default 127.0.0.1 will not go. See iptables(8) manpage regarding
# REDIRECT target for details.
# Depending on your network configuration iptables conf. may be as easy as:
root# iptables -t nat -A PREROUTING --in-interface eth_int -p tcp -j REDSOCKS