revsh: reverse shell with terminal support, data tunneling, and advanced pivoting capabilities
revsh
revsh is a tool for establishing reverse shells with terminal support, reverse VPNs for advanced pivoting, as well as arbitrary data tunneling.
What is a “reverse shell”?
A reverse shell is a network connection that grants shell access to a remote host. As opposed to other remote login tools such as telnet and ssh, a reverse shell is initiated by the remote host. This technique of connecting outbound from the remote network allows for circumvention of firewalls that are configured to block inbound connections only.
What is a “reverse VPN”?
revsh is capable of attaching a virtual ethernet card (tun/tap) to both ends of its crypto tunnel. These cards can then be used to forward raw IP packets or Ethernet frames. When combined with an Iptables NAT rule, or bridging a real ethernet card, this allows for the operator to receive a fully routable IP address on the target machines network. This, essentially, is a full VPN that has performed a connect-back call to the operator to circumvent in-bound packet filtering and grant the operator full network access.
What is a “bind shell”?
A bind shell is a shell that is served from a normal forward network connection. revsh supports both reverse and bind shells. To invoke a bind shell you can either invoke the -b flag on both ends of the connection, or invoke the binary as ‘bindsh‘.
Can’t I just use netcat?
There are many techniques for establishing a reverse shell, but these methods don’t provide terminal support. revsh allows for a reverse shell whose connection is mediated by a pseudo-terminal, and thus allows for features such as:
- job control
- control character processing (e.g Ctrl-C)
- auto-completion
- support for programs requiring a controlling tty (e.g. vi)
- processing of window re-size events
In addition, revsh also offers the following features:
- UTF-8 support.
- Circumvents utmp / wtmp. (No login recorded.)
- Processes rc file commands upon login for easy scripting.
- OpenSSL encryption with key based authentication baked into the binary.
- Anonymous Diffie-Hellman encryption upon request.
- Ephemeral Diffie-Hellman encryption as default. (Now with more Perfect Forward Secrecy!)
- Cert pinning for protection against sinkholes and mitm counter-intrusion.
- Connection timeout for remote process self-termination.
- Randomized retry timers for non-predictable auto-reconnection.
- Netcat style non-interactive data brokering for file transfer.
- Proxy support: point-to-point, SOCKS 4, SOCKS 4a, and SOCKS 5. Proxies are available in both directions for complete flexibility.
- TUN / TAP support for forwarding raw IP packets / Ethernet frames.
- Escape sequence commands to kill non-responsive nodes or print connection statistics.
revsh is intended as a supplementary tool for a pentester’s toolkit that provides the full set of terminal features across an encrypted tunnel. All together in a small (~75k) easy to use binary.
Where can I use revsh?
revsh was developed on x86_64 Linux. Here is a brief list of Arch / OS combinations that it has been used on:
- x86_64 Linux
- i686 Linux
- amd64 FreeBSD
Installation
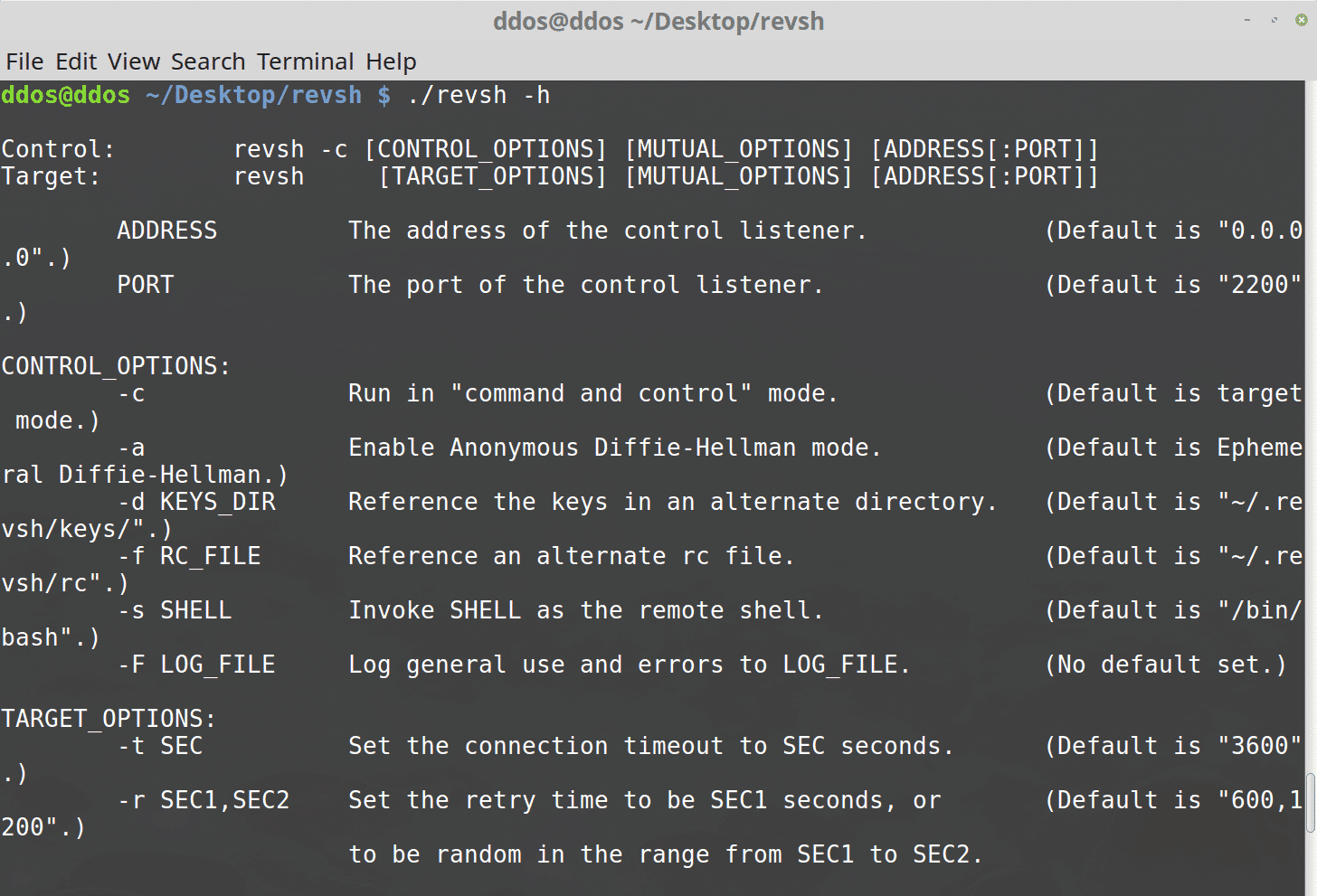
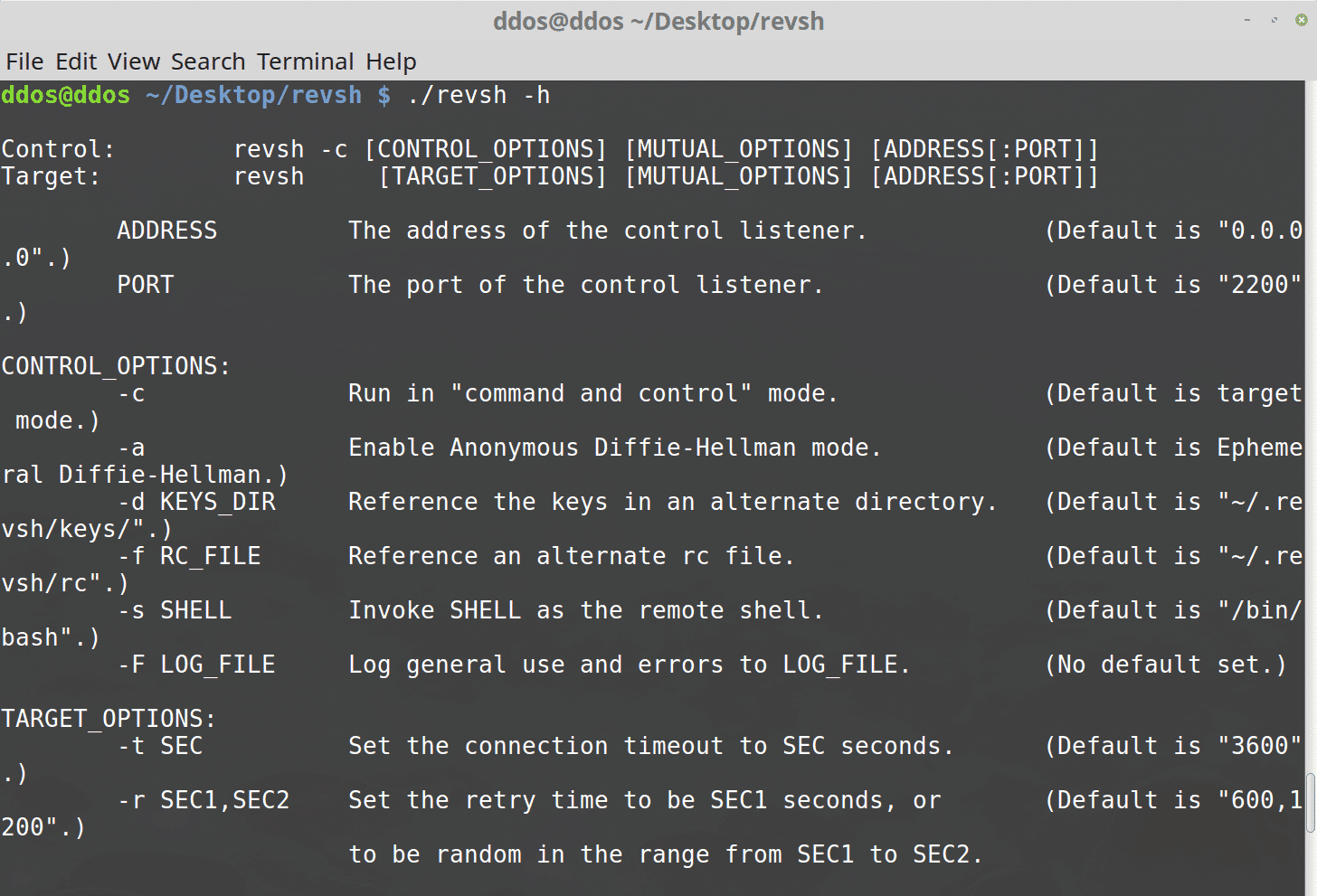
Usage
Examples
Control host example IP: 192.168.0.42
Target host example IP: 192.168.0.66
Copyright (c) 2013 @emptymonkey
Source: https://github.com/emptymonkey/





