riskscanner: Open source multi-cloud security compliance scanning platform
riskscanner
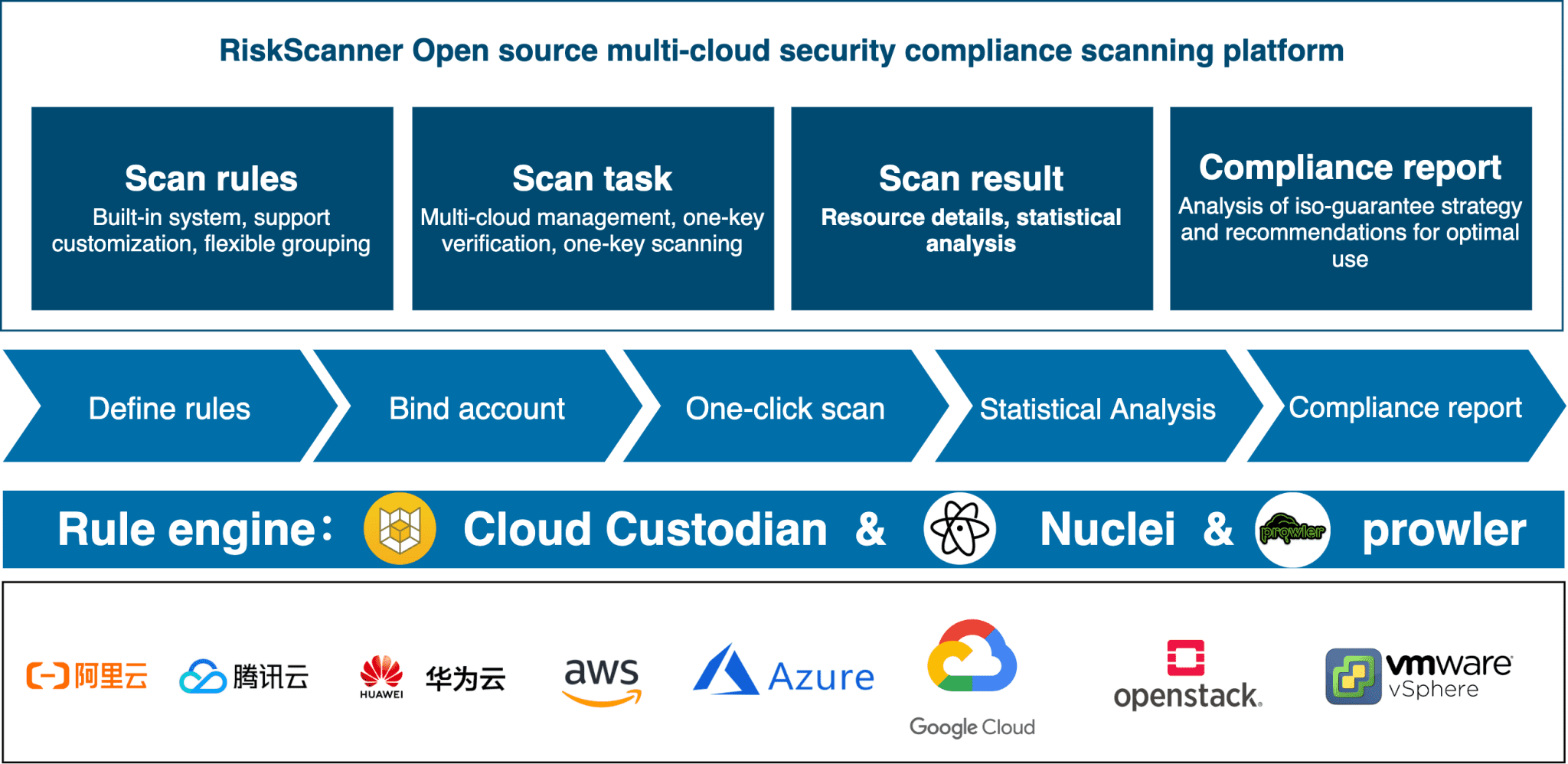
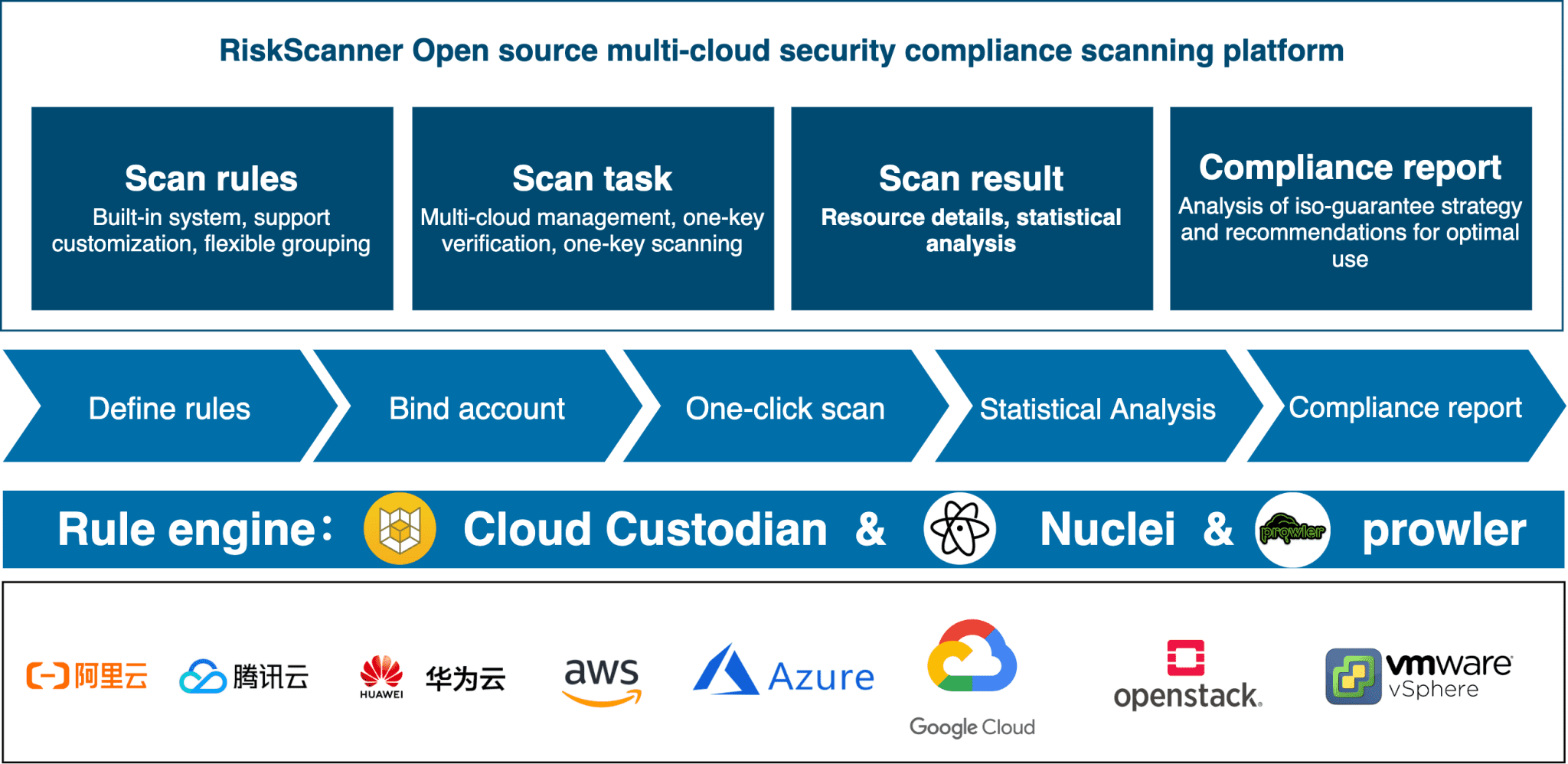
RiskScanner is an open-source multi-cloud security compliance scanning platform, Based on Cloud Custodian, Prowler, and Nuclei engines, it realizes security compliance scanning and vulnerability scanning of mainstream public (private) cloud resources.
Functional advantage
- Hierarchical protection 2.0 pre-inspection: Comply with Hierarchical Protection 2.0 specifications, covering various inspections such as security audit, access control, intrusion prevention, network architecture and management center.
- CIS compliance inspection: In compliance with CIS specifications, check and real-time monitor whether resources on the cloud meet CIS requirements.
- Vulnerability scan: Based on the vulnerability rule library, the security vulnerabilities of designated network equipment and application services are detected through scanning and other means.
- Best practice recommendations: Develop a compliance control baseline, provide best practice recommendations for enterprise-level users, and continue to improve the level of compliance.
RiskScanner follows the GPL v2 open source agreement and uses SpringBoot/Vue for development. The interface is beautiful and the user experience is good. The supported public clouds include Alibaba Cloud, Tencent Cloud, Huawei Cloud, Amazon Web Services, Microsoft Azure, and Google Cloud, and the supported private clouds include OpenStack, VMware vSphere, etc, and support vulnerability scanning.
Technical advantages
- Simple and flexible rules: scanning rules adopt simple YAML format, which is easy to understand and allows users to customize rules.
- Support multiple public (private) clouds: Supported public clouds include Alibaba Cloud, Tencent Cloud, Huawei Cloud, Amazon Web Services, Microsoft Azure, Google Cloud, and supported private clouds include OpenStack, VMware vSphere, etc.
- Support multiple resource types: Supported resource types include cloud servers, cloud disks, cloud databases, load balancing, object storage, private networks, security groups, etc.
- Rich and comprehensive vulnerability rule library: Covers OWASP TOP 10 Web vulnerabilities, such as: SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), weak passwords, etc.
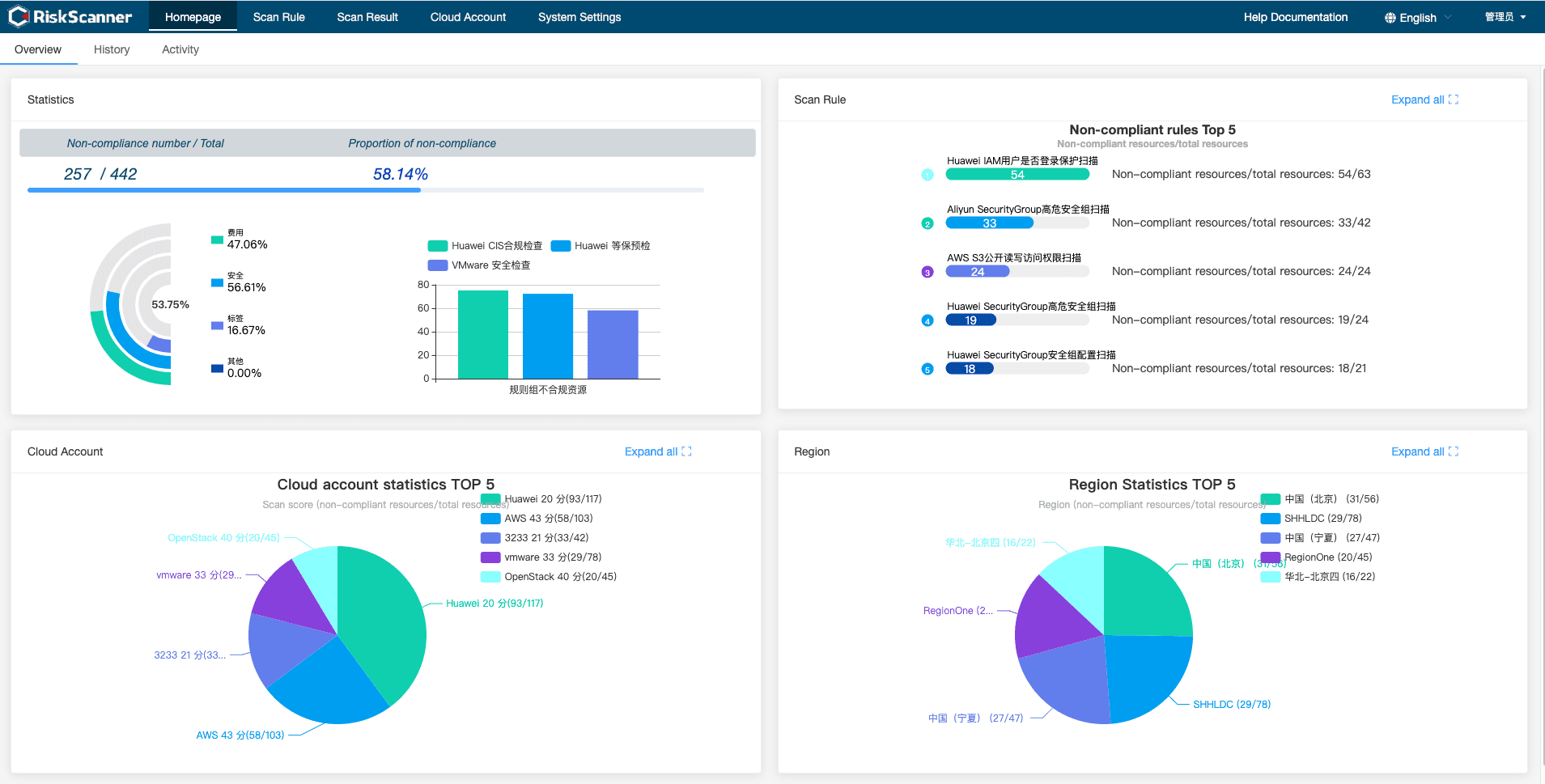
UI interface display
Install & Use
Copyright (c) 2014-2021 FIT2CLOUD, All rights reserved.





