S3cret Scanner: Hunting For Secrets Uploaded To Public S3 Buckets
S3cret Scanner: Hunting For Secrets Uploaded To Public S3 Buckets
- S3cret Scanner tool is designed to provide a complementary layer for the Amazon S3 Security Best Practices by proactively hunting secrets in public S3 buckets.
- Can be executed as a scheduled task or On-Demand
Automation workflow
The automation will perform the following actions:
- List the public buckets in the account (Set with ACL of Public or objects can be public)
- List the textual or sensitive files (i.e. .p12, .pgp and more)
- Download, scan (using truffleHog3), and delete the files from the disk, once done evaluating, one by one.
- The logs will be created in the logger.log file.
Installation
Prerequisites
- Python 3.6 or above
- TruffleHog3 installed in $PATH
- An AWS role with the following permissions:
- If you’re using a CSV file – make sure to place the file accounts.csv in the csv directory, in the following format:
Install
git clone https://github.com/Eilonh/s3crets_scanner.git
pip3 install -r requirements.txt
pip3 install trufflehog3
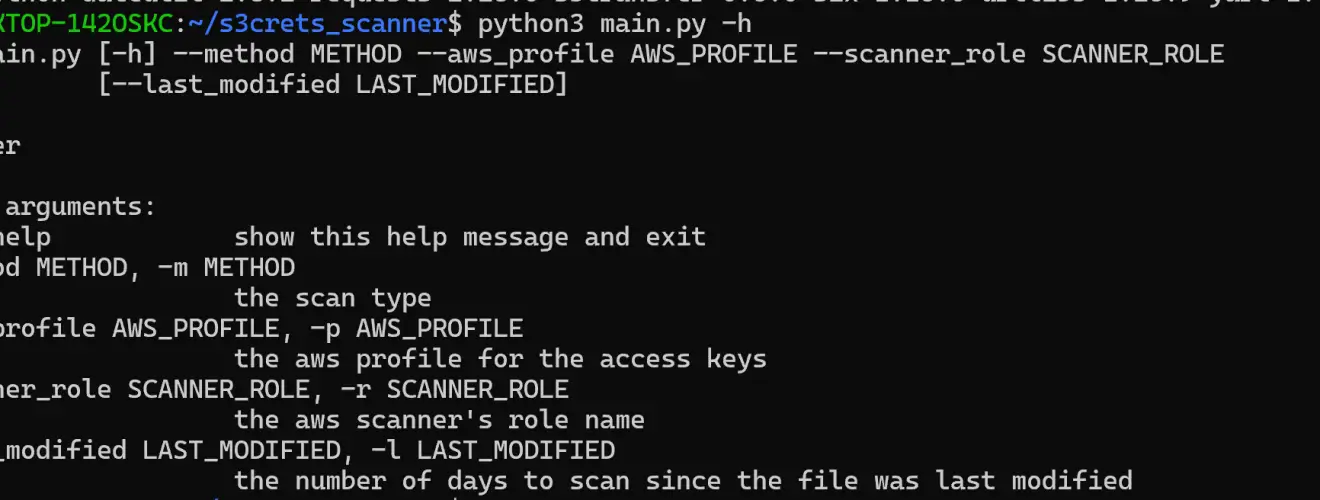
Use

Copyright (C) 2022 Eilonh
Source: https://github.com/Eilonh/






