Sniffles
Sniffles is a tool for creating packet captures that will test IDS that use fixed patterns or regular expressions for detecting suspicious behavior. Sniffles works very simply. It takes a set of regular expressions or rules and randomly chooses one regular expression or rule. It then generates content based on that rule or regular expression. For fixed strings, this means adding the string directly to the data (possibly with offsets or other options as per Snort rules). For regular expressions, the process is somewhat more complex. The regular expression is converted to an NFA and a random path is chosen through the NFA (from start to end). The resulting data will match to the regular expression. Finally, Sniffles can be set to full match or partial match. With a full match, the packet data will absolutely match to at least one rule or a regular expression (Some Snort options are not fully considered though). A partial match will erase the last character from a matching character sequence to a sequence that should not match (may match to another rule though). Matching rules should cause the most burden on an IDS. Thus, it is possible to determine how well the IDS handles worst-case traffic. Partial matching traffic will cause almost as much burden as matching traffic. Finally, Sniffles can also generate traffic that has completely random data. Such random data offers a best-case scenario as random data is very unlikely to match with any rules. Thus, it can be processed at maximum speed. Thus, Sniffles allows the creation of packet captures for best and worst case operation of IDS deep packet inspection.
In addition to the above, Sniffles also has the ability to create an evaluation packet captures. There are two types of evaluation packet captures. The first evaluation packet capture will create exactly one packet for each rule or regular expression, in sequence. Thus it is possible to test and see that each rule matches as expected. The full evaluation goes a step further and creates a packet for every possible branch in a regular expression. A single regular expression could have thousands of possible branches. This tests to ensure that all possible branches of a regular expression are handled properly. Evaluation packet captures should match all packets. Any unmatched packets most likely represent a failure of the IDS and need further investigation. Of course, there is always the possibility that Sniffles is not creating the correct packet for a given IDS, or doesn’t recognize a particular option for a rule. Check the supported rule features for more information.
Finally, Sniffles can also do a lot for generating random network traffic. By default, random traffic is TCP, UDP, or ICMP and unidirectional. However, it can also generate TCP traffic with ACKs, handshakes, and teardowns for each stream. It will generate correct sequence numbers and checksums. Further, MAC addresses can be set according to desired distributions, and IP network addresses can be defined by Home and External address spaces. In addition, it is possible to simulate scans within a traffic capture.
Supported Formats:
- Snort: Snort alert rules (rule should begin with the Alert directive). Content tags are recognized and parsed correctly. PCRE tags are likewise correctly parsed. HTTP tags are processed consecutively so they may not create the desired packet. Content (and PCRE or HTTP content) can be modified by distance, within and offset. A rule may use a flow control option, though only the direction of the data is derived from this. The nocase option is ignored and the case presented is used. All other options are ignored. The header values are parsed and a packet will be generated meeting those values. If Home and External network address spaces are used then the correct space will be used for the respective $HOME_NET and $EXTERNAL_NET variables. Example:alert tcp $EXTERNAL_NET any -> $HOME_NET 8080 (msg:”SERVER-APACHE Apache Tomcat UNIX platform directory traversal”; flow:to_server; content:”/..|5C|/”; content:”/..|5C|/”; http_raw_uri;
- Regular expressions: Raw regular expressions 1 to a line written as either abc or /abc/i. Currently supports the options i, s, and m. Other options are ignored. Example:/ab*c(d|e)f/i
- Sniffles Rule Format
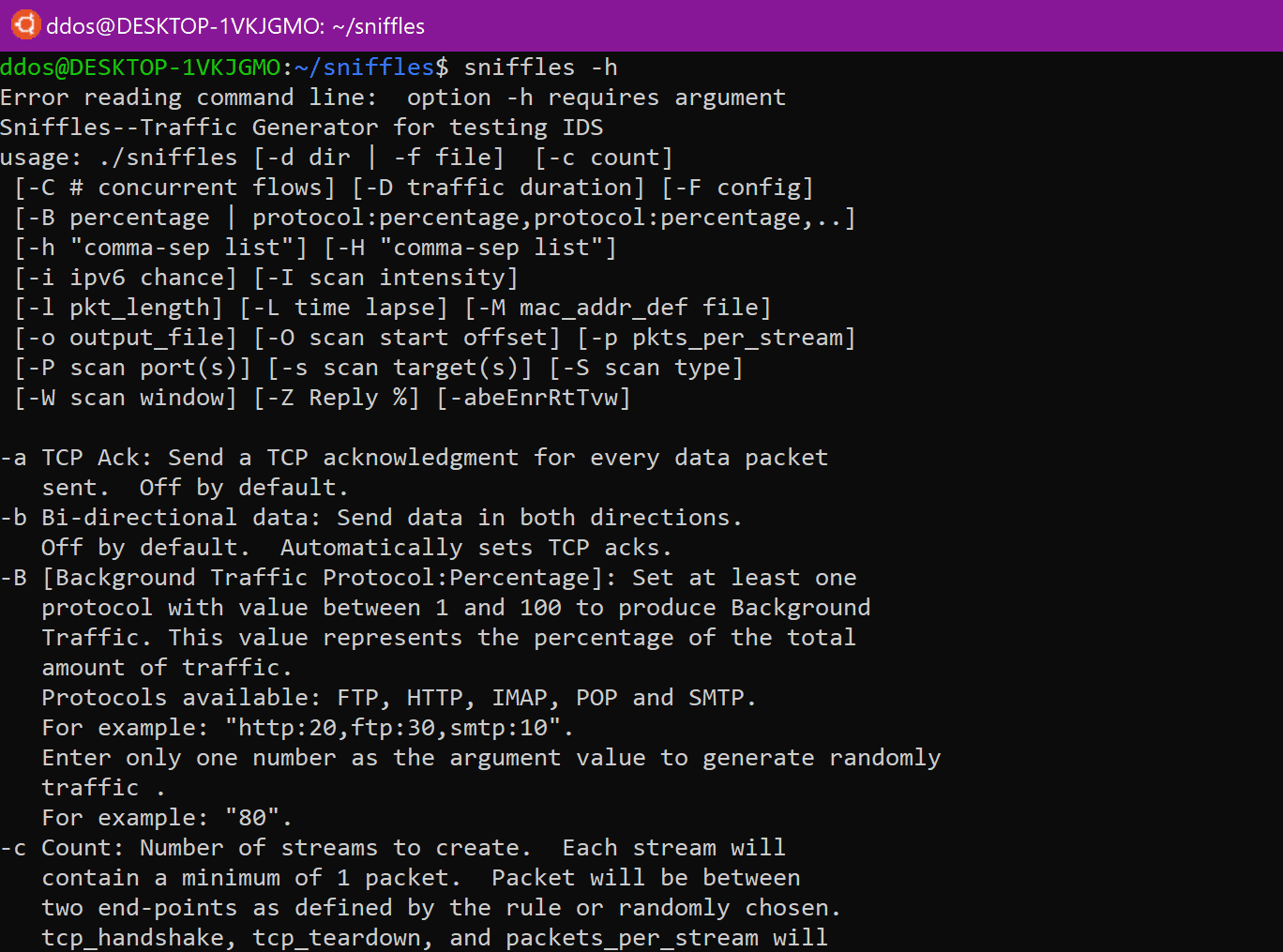
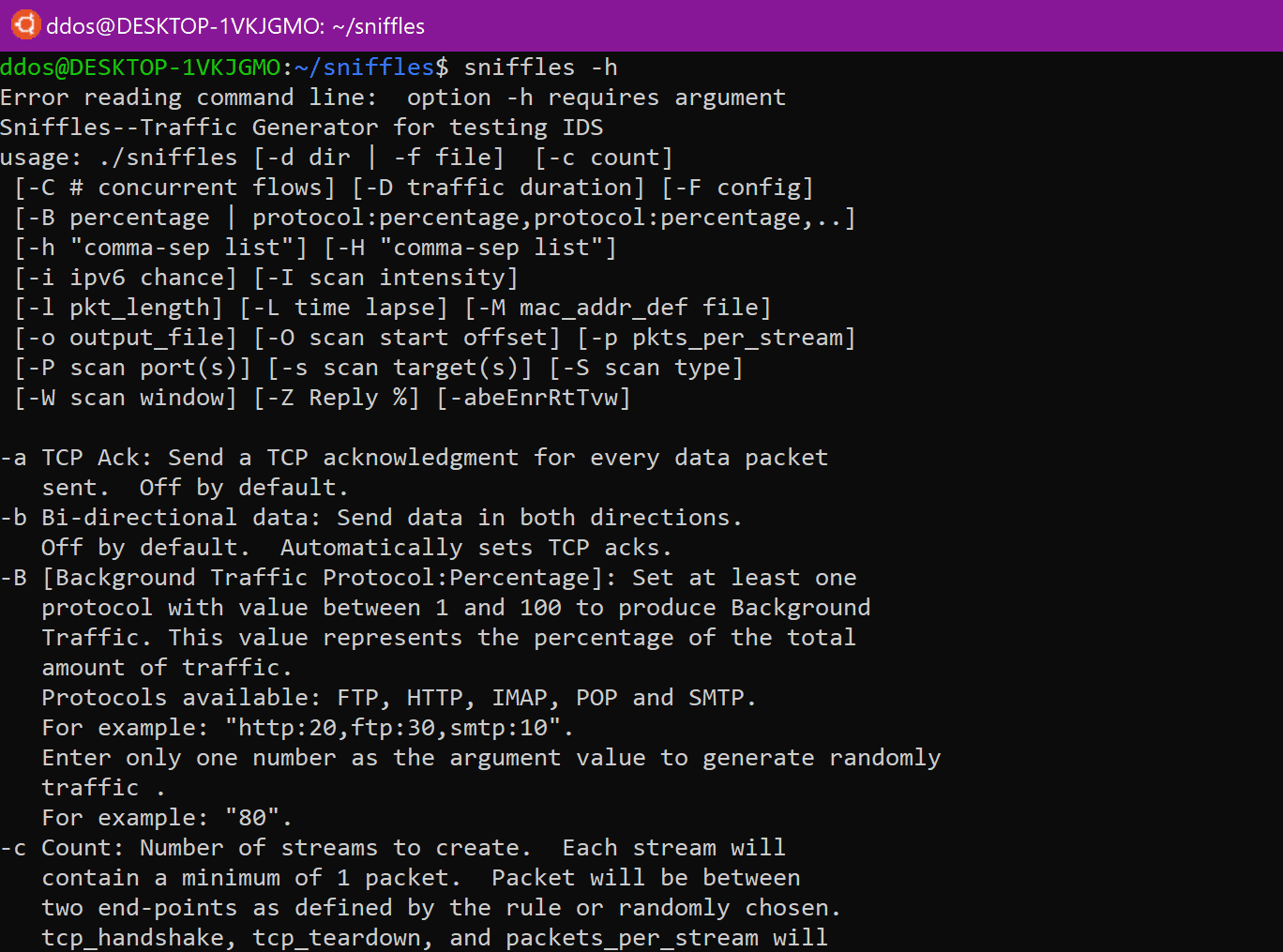
Install && Use
Copyright (C) 2017