Security researchers have uncovered a critical security flaw in the popular file archiver 7-Zip. Specifically, this 7-Zip...
Exploit
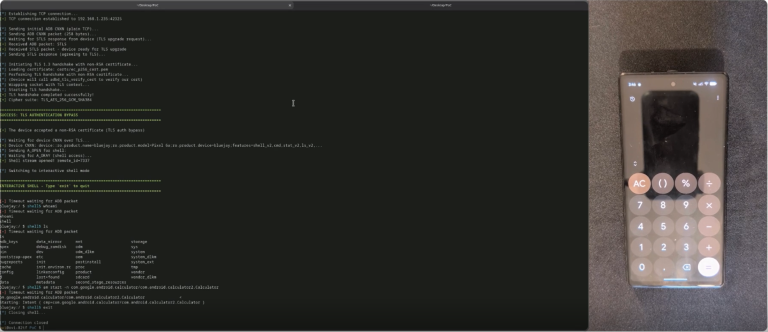
A critical vulnerability existing within the core of Android’s developer tools has been exposed, revealing a zero-click...
A critical vulnerability has been identified in the Snap One WattBox 800 and 820 series power controllers....
Security researchers have sounded the alarm on a critical vulnerability in LiteLLM, a massively popular open-source gateway...
The Quake III Arena engine, a cornerstone of FPS history open-sourced by id Software, has been hit...
Just when administrators thought NTLM relay attacks were becoming a thing of the past, a dangerous new...
In a recent deep-dive analysis, security researcher BitsByWill examined two critical Linux kernel vulnerabilities—CVE-2023-52440 and CVE-2023-4130—both impacting...
The Sangoma FreePBX Security Team has issued an urgent security advisory after discovering a potential exploit targeting...
The maintainers of ImageMagick have patched four security vulnerabilities that could impact applications using the popular image...
Fortinet has issued an urgent security advisory for a critical remote unauthenticated command injection vulnerability affecting multiple...
Security researcher Jann Horn from Google Project Zero disclosed the technical details and proof-of-concept exploit code for...
In April 2025, Microsoft issued a critical security patch addressing a serious vulnerability in the Windows Common...
A critical SQL injection vulnerability in Fortinet FortiWeb, tracked as CVE-2025-25257, has been added to the CISA...
A dangerous Linux privilege escalation vulnerability, CVE-2023-0386, has officially entered the CISA Known Exploited Vulnerabilities (KEV) Catalog...
Security researcher Jael Koh of PixiePoint Security has unveiled the technical details and working proof-of-concept exploits for...
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two new vulnerabilities to its Known Exploited...
Security researchers at ht3labs published the technical details and proof-of-concept exploit code for a trio of critical...
FortiGuard Labs has uncovered a renewed phishing campaign that leverages the eight-year-old CVE-2017-0199 vulnerability to deploy FormBook,...
Security researcher Egidio Romano (EgiX) uncovers a fascinating PHP Object Injection (POI) vulnerability in legacy versions of...
Nintendo’s recently launched Switch 2 console has already had a vulnerability discovered by enthusiasts. Security researcher David...