Forager
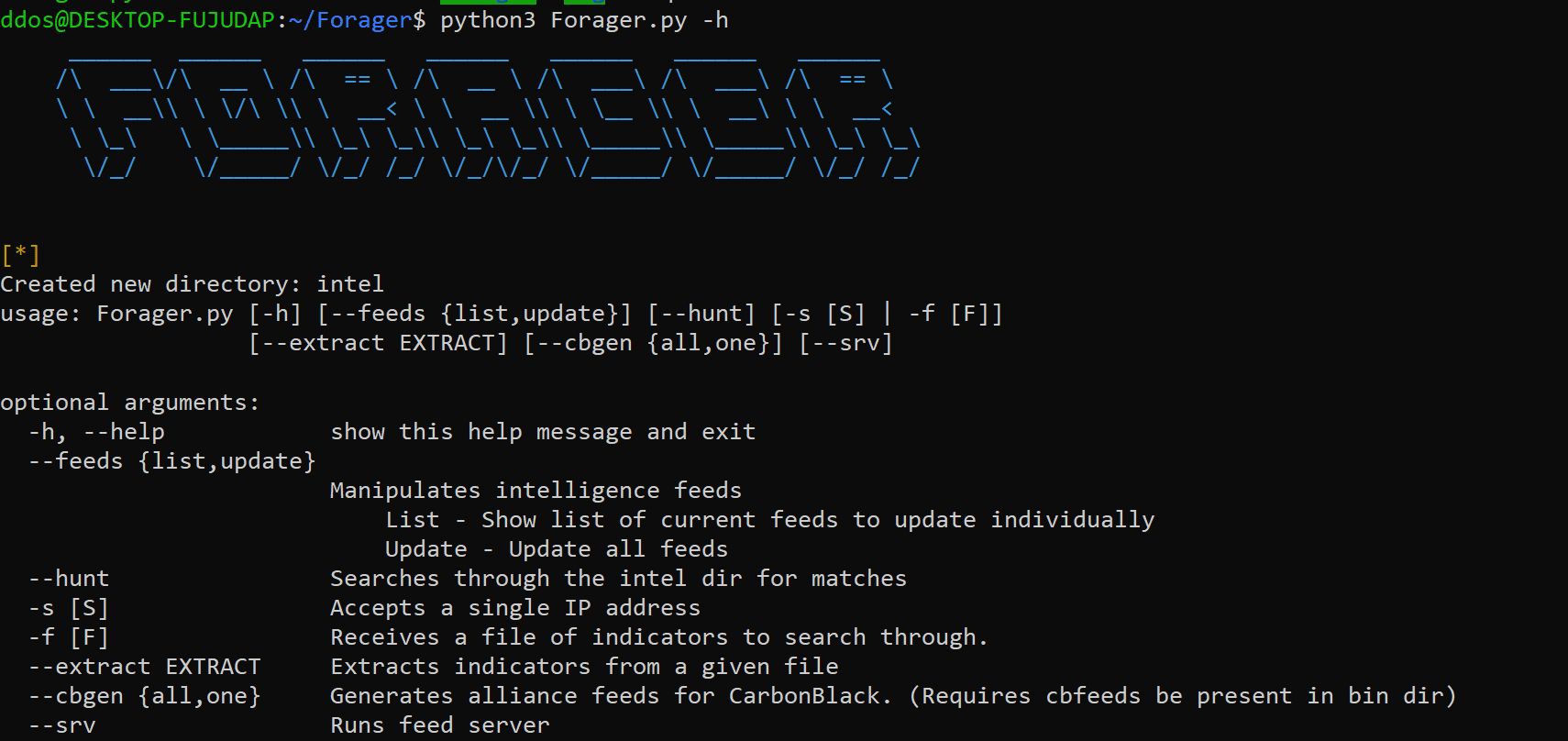
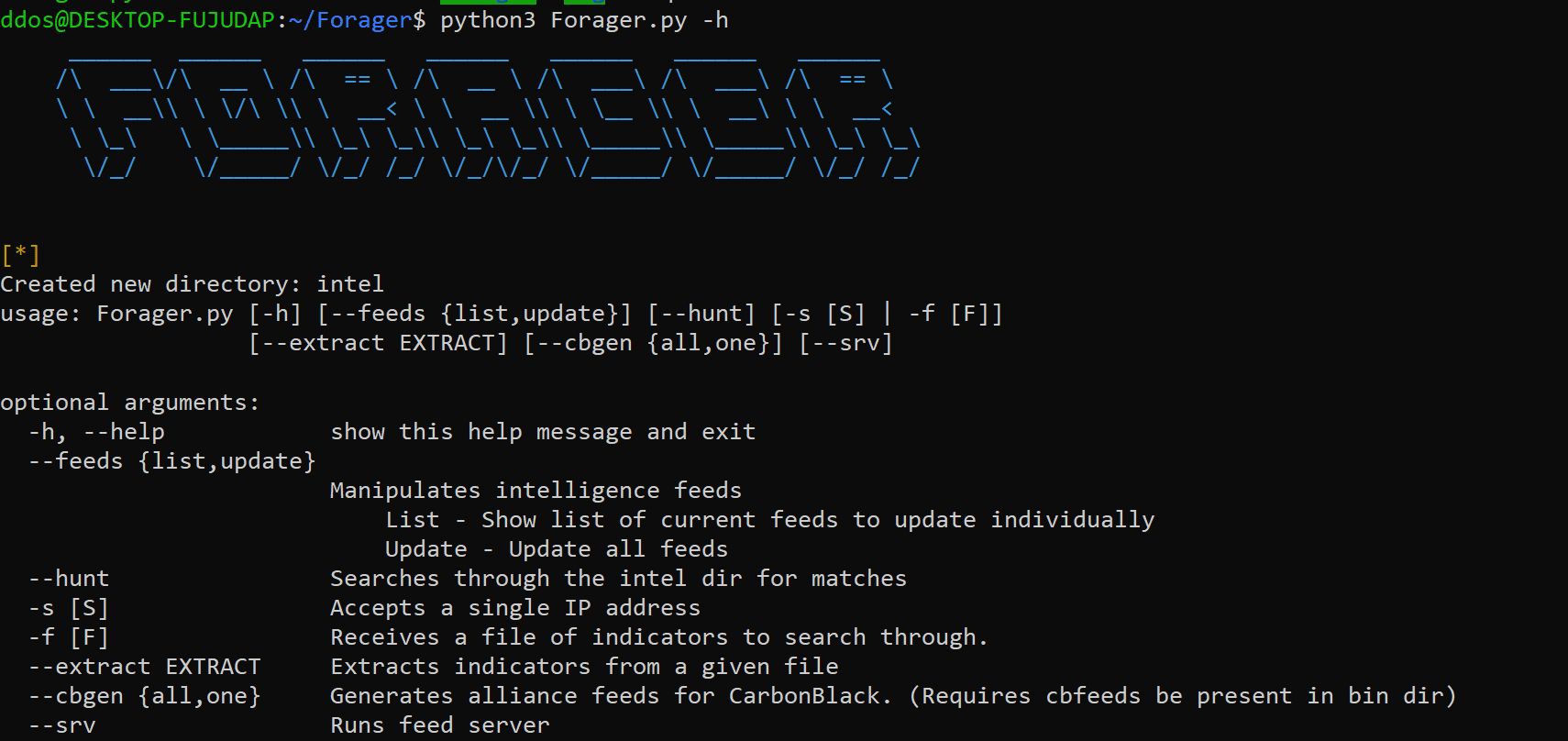
Do you ever wonder if there is an easier way to retrieve, store, and maintain all your threat intelligence data? Random user, meet Forager. Not all threat intel implementations require a database that is “correlating trillions of data points..” and instead, you just need a simple interface, with simple TXT files, that can pull threat data from other feeds, PDF threat reports, or other data sources, with minimal effort. With 15 pre-configured threat feeds, you can get started with threat intelligence feed management today. Right now. Do it!
Features At A Glance
- Fetch intel from URL’s using modular feed functions
- Extract domain, md5, sha1, sha256, IPv4, and YARA indicators
- Search through the current intel set by single IP or with an IOC file
- Generate JSON feeds for consumption by CarbonBlack
- Serves up a Simple HTTP JSON feed server for CarbonBlack
Install
git clone https://github.com/opensourcesec/Forager.git
pip3 install -r requirements.txt
Use
Copyright (c) 2014 Bobby Argenbright
Source: https://github.com/opensourcesec/