ThreatIngestor v1.4 releases: Extract and aggregate threat intelligence
ThreatIngestor
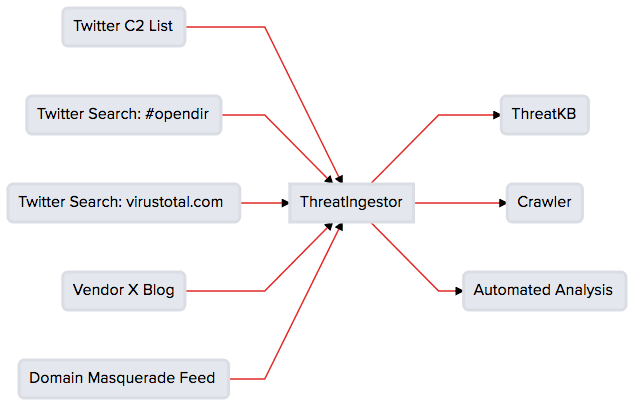
An extendable tool to extract and aggregate IOCs from threat feeds.
Integrates out-of-the-box with ThreatKB and MISP, and can fit seamlessly into any existing workflow with SQS, Beanstalk, and custom plugins.
ThreatIngestor can be configured to watch Twitter, RSS feeds, or other sources, extract meaningful information such as malicious IPs/domains and YARA signatures and send that information to another system for analysis.
There is a never-ending stream of publicly available information on malicious activities online, but compiling all that information manually can take a lot of manual effort and time. ThreatIngestor automates as much of that work as possible, so you can focus on more important things.
Changelog v1.4
Breaking Changes
- Due to the recent Twitter API changes, the Twitter operator is no longer supported (#157)
Features
- ThreatIngestor now offers the ability to include program monitoring via BugSnag. You can include your BugSnag credentials the traditional way by adding them to the
config.yml(#157) - The ability to exclude URLs from RSS and sitemap feeds is now available. This utilizes raw regular expressions (regex) and is not filtered like the
includeoption (#148)
Install && Use
Copyright (C) 2017






