tracy v0.9 releases: finding all sinks and sources of a web application
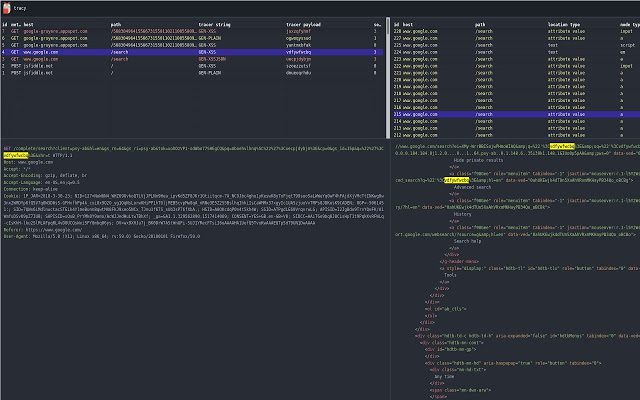
Tracy
A pentesting tool designed to assist with finding all sinks and sources of a web application and display these results in a digestible manner. tracy should be used during the mapping-the-application phase of the pentest to identify sources of input and their corresponding outputs. tracy can use this data to intelligently find vulnerable instances of XSS, especially with web applications that use lots of JavaScript.
tracy is a browser extension and light-weight HTTP proxy that records all user input to a web application and monitors any time those inputs are output, for example in a DOM write, server response, or call to eval.
tracy was written with the goal of eliminating XSS by assisting a penetration tester in identifying every source of input into an application and following that input to all of its sinks. These cases are documented and stored as references that can be used to identify the locations of potentially risky input.
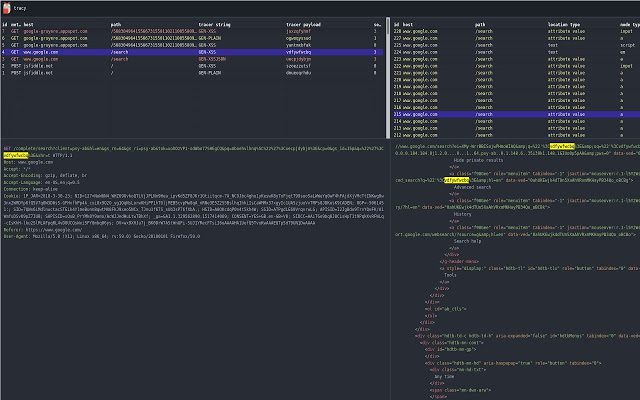
How it works
While browsing a web application, a user flags particular input they would like to be traced. The extension marks this input with a reference and documents any time this reference is seen in a server response, written to the DOM, or used in one of the other dangerous methods mentioned above.
The extension makes use of a light-weight proxy to monitor server responses and MutationObserver7 to monitor DOM writes. Additionally, the extension proxies8 a few functions that are considered dangerous and checks to see if these functions are executing arguments that contain one of the collected references.
Changelog v0.9
- Now using webpack to bundle resources
- Updates to database schema to improve performance
- Fixes to UI for better event navigation
- Performance updates to the DOM MutationObserver for sites that make large amounts of DOM requests
Get it
Copyright (c) 2018 NCC Group Plc
Source: https://github.com/nccgroup/





