UEFI Firmware Parser v1.11 releases: Parse BIOS/Intel ME/UEFI firmware related structures
UEFI Firmware Parser
The UEFI firmware parser is a simple module and set of scripts for parsing, extracting, and recreating UEFI firmware volumes. This includes parsing modules for BIOS, OptionROM, Intel ME and other formats too. Please use the example scripts for parsing tutorials.
Features
- UEFI Firmware Volumes, Capsules, FileSystems, Files, Sections parsing
- Intel PCH Flash Descriptors
- Intel ME modules parsing (ME, TXE, etc)
- Dell PFS (HDR) updates parsing
- Tiano/EFI, and native LZMA (7z) [de]compression
- Complete UEFI Firmware volume object hierarchy display
- Firmware descriptor [re]generation using the parsed input volumes
- Firmware File Section injection
Supported Vendors
This module has been tested on BIOS/UEFI/firmware updates from the following vendors. Not every update for every product will parse, some may require a-priori decompression or extraction from the distribution update mechanism (typically a PE).
- ASRock
- Dell
- Gigabyte
- Intel
- Lenovo
- HP
- MSI
- VMware
- Apple
Changelog v1.11
- Remove Python version specific classifiers
Install
sudo pip install uefi_firmware
or
git clone https://github.com/theopolis/uefi-firmware-parser.git
sudo python ./setup.py install
Use
The simplest way to use the module to detect or parse firmware is through the AutoParser class.
There are several classes within the uefi, pfs, me, and flash packages that accept file contents in their constructor. In all cases there are abstract methods implemented:
- process() performs parsing work and returns a True or False
- showinfo() print a hierarchy of information about the structure
- dump() walk the hierarchy and write each to a file
Scripts
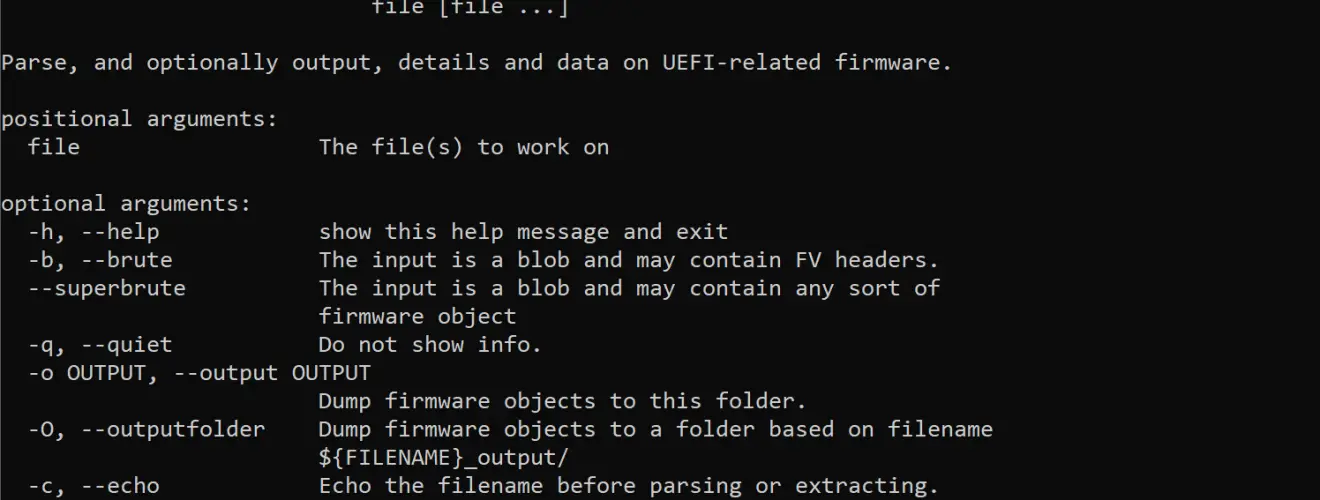
A Python script is installed uefi-firmware-parser
To test a file or directory of files:
If you need to parse and extract a large number of firmware files check out the -O option to auto-generate an output folder per file. If parsing and searching for internals in a shell the –echo option will print the input filename before parsing.
The firmware-type checker will decide how to best parse the file. If the –test option fails to identify the type, or calls is unknown, try to use the -b or –superbrute option. The latter performs a byte-by-byte type checker.
GUID Injection
Injection or GUID replacement (no addition/subtraction yet) can be performed on sections within a UEFI firmware file, or on UEFI firmware files within a firmware filesystem.
Note: when injecting into a firmware file the user will be prompted for which section to replace. At the moment this is not-yet-scriptable.
IDA Python support
There is an included script to generate additional GUID labels to import into IDA Python using Snare’s plugins. Using the -g LABEL the script will generate a Python dictionary-formatted output. This project will try to keep up-to-date with popular vendor GUIDs automatically.
Copyright (c) 2014 Teddy Reed <teddy@prosauce.org>
Copyright (c) 2013 Hector Martin <hector@marcansoft.com>
Source: https://github.com/theopolis/






