volatility 3 v2.5.2 releases: The volatile memory extraction framework
Volatility 3: The volatile memory extraction framework
Volatility is the world’s most widely used framework for extracting digital artifacts from volatile memory (RAM) samples. The extraction techniques are performed completely independent of the system being investigated but offer visibility into the runtime state of the system. The framework is intended to introduce people to the techniques and complexities associated with extracting digital artifacts from volatile memory samples and provide a platform for further work into this exciting area of research.
In 2019, the Volatility Foundation released a complete rewrite of the framework, Volatility 3. The project was intended to address many of the technical and performance challenges associated with the original code base that became apparent over the previous 10 years. Another benefit of the rewrite is that Volatility 3 could be released under a custom license that was more aligned with the goals of the Volatility community, the Volatility Software License (VSL).
Changelog v2.5.2
- New Layers:
- Amazon S3 support
- Google Cloud Storage support
- New plugins:
linux.vmayarascanwindows.mftscan.ads
- New features:
- Dumping of Elf files added to the
elfsplugin
- Dumping of Elf files added to the
- Improvements to ELF support
- Bugfixes to registry support
- Documentation improvements
- Better support for remote ISF directories
Install
git clone https://github.com/volatilityfoundation/volatility3.git
pip3 install -r requirements-minimal.txt
Use
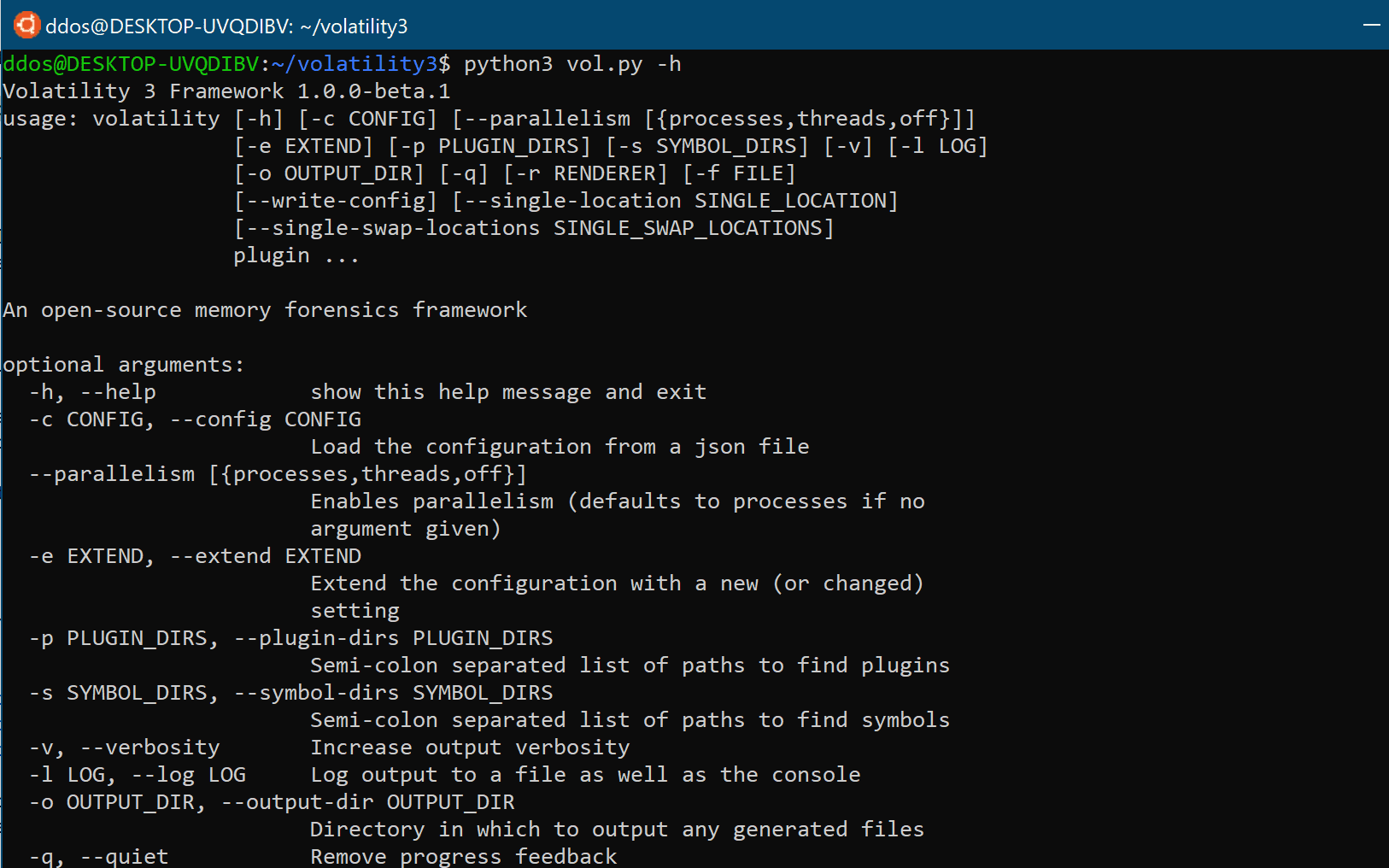
To see available options, run “python vol.py -h”
To get more information on a Windows memory sample and to make sure Volatility supports that sample type, run
‘python -f <imagepath> windows.info’
Example:
$ python vol.py —f /home/user/samples/stuxnet.vmem windows.info
Run some other plugins. The -f or —-single-location is not strictly required, but most plugins expect a single sample. Some also
require/accept other options. Run “python vol.py <plugin> -h” for more information on a particular command.
Tutorial
Copyright (C) 2007-2019 Volatility Foundation