VulnerableCode v33.6.1 releases: free and open vulnerabilities database and the packages they impact
VulnerableCode
VulnerableCode is a free and open database of FOSS software package vulnerabilities and the tools to create and keep the data current.
It is made by the FOSS community to improve and secure the open-source software ecosystem.
Why?
The existing solutions are commercial proprietary vulnerability databases, which in itself does not make sense because the data is about FOSS (Free and Open Source Software).
The National Vulnerability Database which is a primary centralized data source for known vulnerabilities is not particularly well suited to address FOSS security issues because:
- It predates the explosion of FOSS software usage
- It’s data format reflects a commercial vendor-centric point of view in part due to the usage of CPE to map vulnerabilities to existing packages.
- CPEs are just not designed to map FOSS to vulnerabilities owing to their vendor-product centric semantics. This makes it really hard to answer the fundamental questions “Is package foo vulnerable” and “Is package foo vulnerable to vulnerability bar?”
How
VulnerableCode independently aggregates many software vulnerability data sources and supports data re-creation in a decentralized fashion. These data sources (see the complete list here) include security advisories published by Linux and BSD distributions, application software package managers and package repositories, FOSS projects, GitHub, and more. Thanks to this approach, the data is focused on specific ecosystems yet aggregated in a single database that enables querying a richer graph of relations between multiple incarnations of a package. Being specific increases the accuracy and validity of the data as the same version of an upstream package across different ecosystems may or may not be vulnerable to the same vulnerability.
The packages are identified using Package URL PURL as primary identifiers rather than CPEs. This makes answers to questions such as “Is package foo vulnerable to vulnerability bar?” much more accurate and easy to interpret.
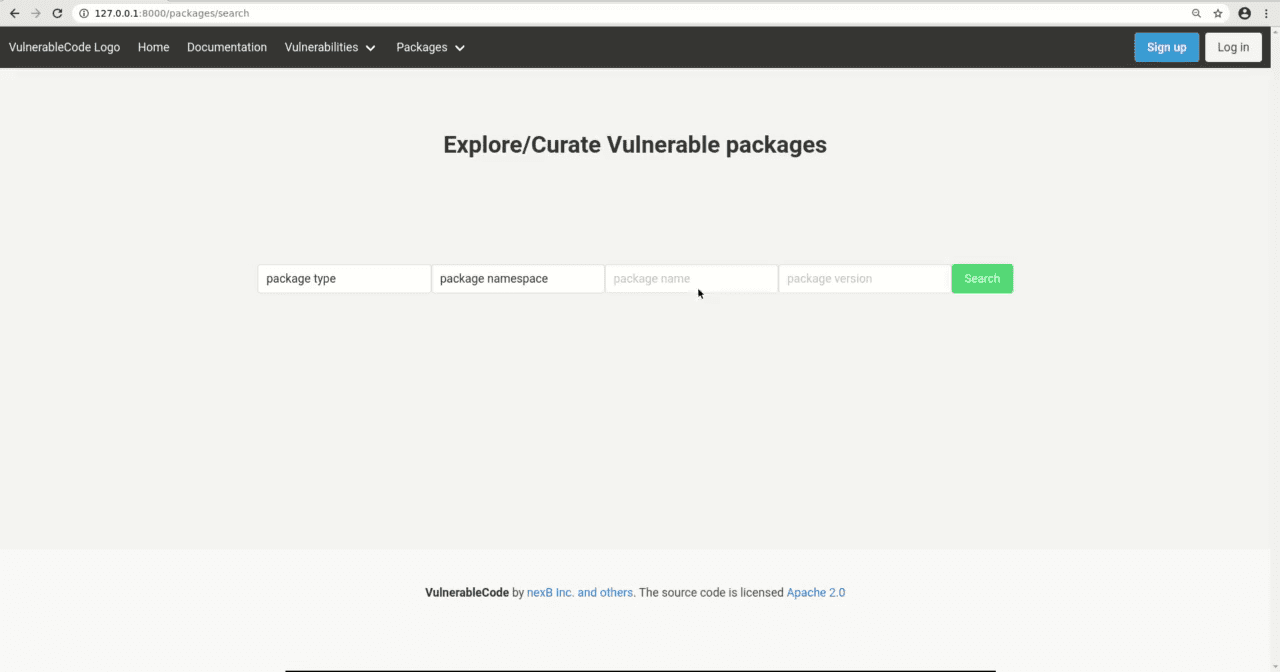
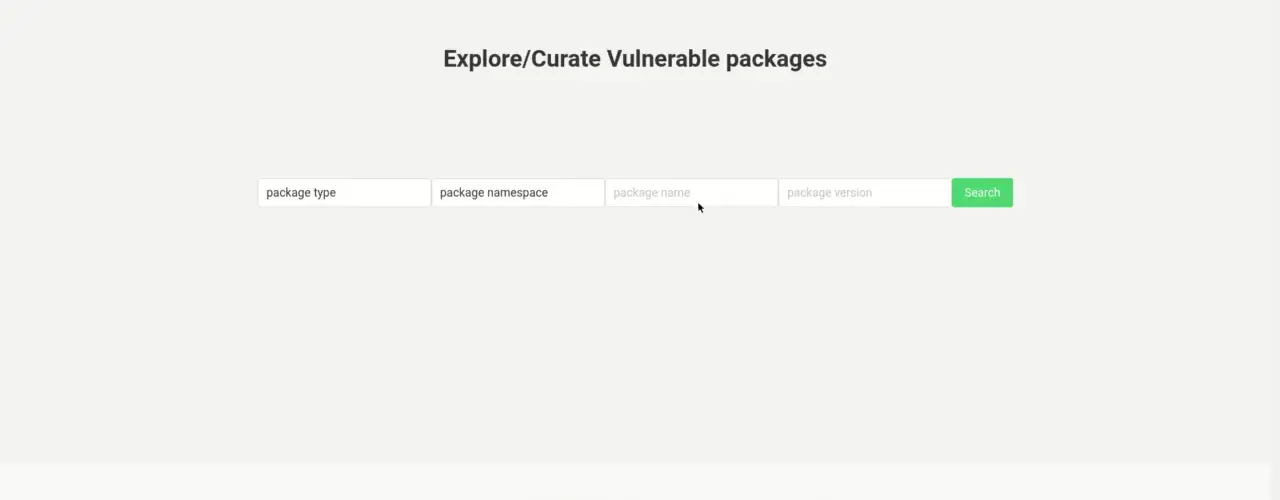
The primary access to the data is through a REST API.
In addition, an emerging web interface goal is to support vulnerabilities data browsing and search and progressively to enable community curation of the data with the addition of new packages and vulnerabilities, and reviewing and updating their relationships.
We also plan to mine for vulnerabilities which didn’t receive any exposure due to various reasons like but not limited to the complicated procedure to receive CVE ID or not able to classify a bug as a security compromise.
Recent presentations:
- Open Source Summit 2020
Install & Use
Copyright (C) 2019 nexB Inc. @nexB