xssmap: Intelligent XSS detection tool
XSS Tool Overview
This tool is an intelligent XSS detection tool that uses human techniques to look for reflected cross-site scripting (XSS) vulnerabilities.
Rather than use the same approach as virtually every other reflected cross-site scripting tool, this tool does not take a list of known XSS vectors and fuzz its way through the target site. Instead, the tool takes a surgical approach and follows the same process that a human pen tester follows when looking for reflected XSS vulnerabilities. Namely, a typical human tester:
- Looks at the parameters of a typical web application request (URL parameters, form parameters, headers, etc.);
- Observes the response to see if any of the parameters are present (a “reflection”);
- If reflected, verifies that the reflection is not a coincidence;
- Derives the context of the reflection if not a coincidence;
- Crafts an attack appropriate to that context;
- Tests to see if the attack is successful.
This XSS tool follows this same process to efficiently identify potential reflected XSS vulnerabilities. Namely, given a valid URL and/or POST body, the tool makes a request to the application. Using XPath queries, the tool determines which (if any) of the parameters are reflected in the application response. If any are reflected, the tool sends another request with a slightly varied input of the reflected parameter to confirm the detected reflection was not a coincidence. We limit the variation to a short random alphanumeric sequence—just enough to offset coincidental reflections. If this modified parameter is still detected as reflected, then the tool can determine the context of the reflection based on the XPath query used to discover it.
For example, given a URL parameter value of foo, an XPath query //*[@*[contains(.,'foo')]] identifies locations where the value foo is reflected in an HTML attribute. With the context of reflection, the tool can then use an attack based on the HTML attribute context. With this attack crafted, the tool makes a third request to the application via the PhantomJS headless rendering engine. This engine allows us to hook various events that are triggered by our crafted attack when the attack is successful. Using these hooks, the tool can then determine whether or not the crafted attack actually executed.
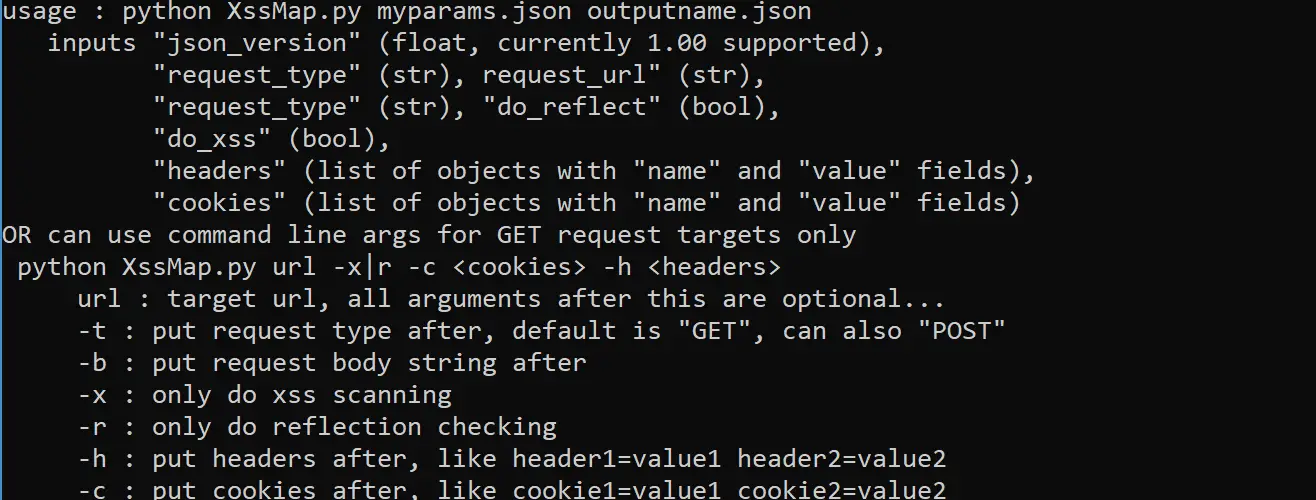
For convenience, this tool can detect reflection (run_reflect) or detect successful XSS attacks (run_xss) separately (i.e. execute steps 1-4, execute steps 5-6 above). We refer to these as “reflection detection” and “XSS scan” respectively.
By following this human technique, our tool is able to find XSS vulnerabilities in as little as 3 requests, whereas most XSS tools hammer the target site with hundreds or thousands of requests.

Installation && Tutorial
Copyright 2016-2017 Secure Decisions, a division of Applied Visions, Inc.






