ysoserial.net v1.36 releases: Deserialization payload generator for a variety of .NET formatters
ysoserial.net
A proof-of-concept tool for generating payloads that exploit unsafe .NET object deserialization.
Description
ysoserial.net is a collection of utilities and property-oriented programming “gadget chains” discovered in common .NET libraries that can, under the right conditions, exploit .NET applications performing unsafe deserialization of objects. The main driver program takes a user-specified command and wraps it in the user-specified gadget chain, then serializes these objects to stdout. When an application with the required gadgets on the classpath unsafely deserializes this data, the chain will automatically be invoked and cause the command to be executed on the application host.
It should be noted that the vulnerability lies in the application performing unsafe deserialization and NOT in having gadgets on the classpath.
This project is inspired by Chris Frohoff’s ysoserial project
Disclaimer
This software has been created purely for the purposes of academic research and for the development of effective defensive techniques and is not intended to be used to attack systems except where explicitly authorized. Project maintainers are not responsible or liable for misuse of the software. Use responsibly.
This software is a personal project and not related to any companies, including Project owner and contributors employers.
Changelog v1.36
- Update README.md by @irsdl in #126
- Fixing the Mono gadget by @irsdl in #127
- Update README.md by @irsdl in #128
- serializer helper update + testing arena by @irsdl in #129
- code clean-up by @irsdl in #130
- Hex output stdin fixes by @Bort-Millipede in #131
- project file update by @irsdl in #132
- project update by @irsdl in #133
- project update by @irsdl in #134
- Fixing the single quote escaping issue in JSON messages by @irsdl in #136
- Fixing bugs in cmd payloads’ JavaScript escaping by @irsdl in #137
- Readme update, code content update by @irsdl in #138
- Update README.md by @irsdl in #139
- adding a feature & general updates by @irsdl in #140
- Adding new gadgets & improvements by @irsdl in #141
- fixing descriptions, refactoring some names by @irsdl in #142
- stdin Encoding Fix by @Bort-Millipede in #144
- added –stdin feature to ViewStatePlugin.cs by @Ramzeth in #145
- Added ObjectDataProvider gadget generation for MessagePack (Typeless) by @NinesPsygnosis in #146
- Reduced the necessary code to achieve gadget generation for MessagePackTypeless by @NinesPsygnosis in #147
- Added link to blog article for MessagePack Typeless gadget generation by @NinesPsygnosis in #149
- Added a generator for XAML that does Assembly.Load with compression by @russtone in #151
- Correcting options for DotNetNuke plugin by @idealphase in #154
- Post hexacon by @chudyPB in #156
Download
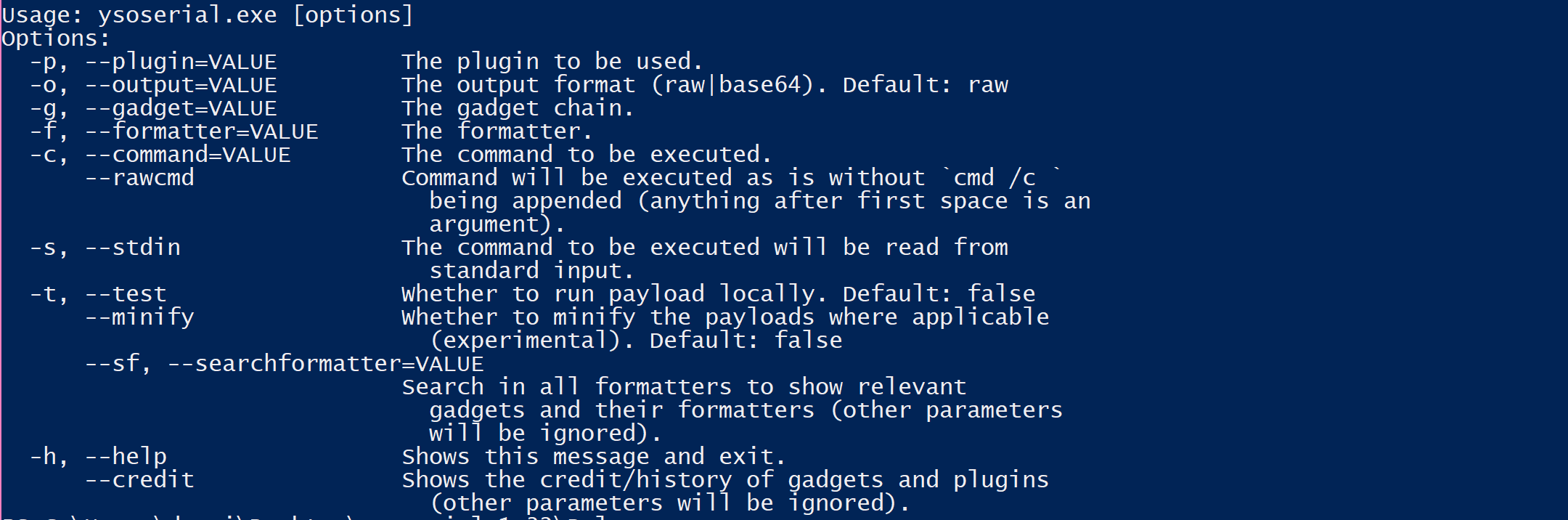
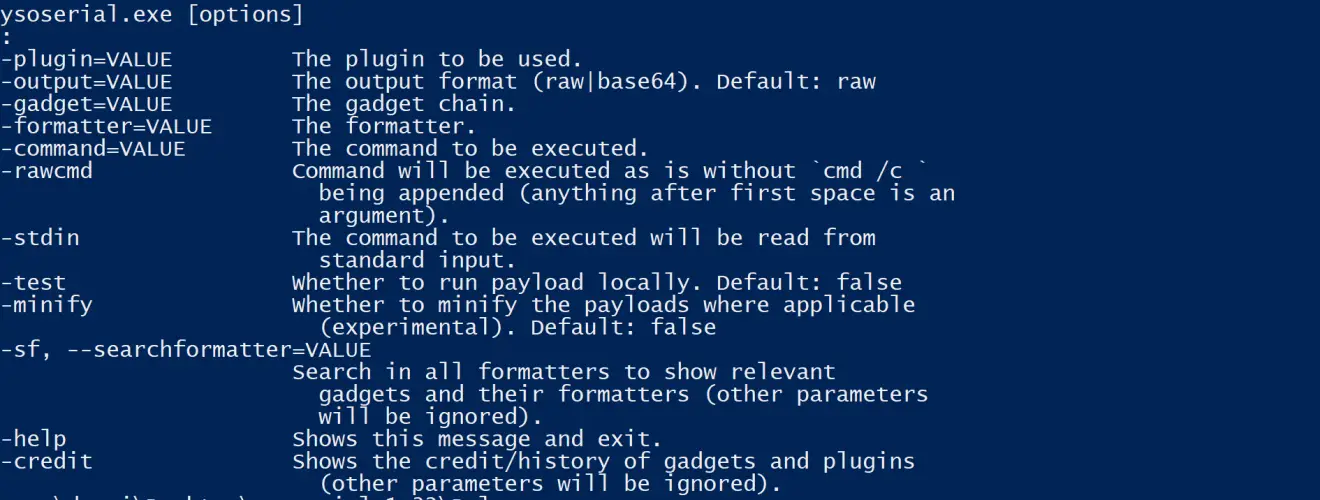
Usage
Example
Copyright (c) 2017-2019 Alvaro Muñoz
Source: https://github.com/pwntester/