badKarma – advanced network reconnaissance toolkit
badKarma is a python3 GTK+ toolkit that aims to assist penetration testers during all the network infrastructure penetration testing activity phases. It allows testers to save time by having point-and-click access to their toolkits, launch them against single or multiple targets and interact with them through simplified GUIs or Terminals.
Every task’s output is logged under a session file in order to help during a reporting phase or in a possible incident response scenario. It is also available a proxychains switch that let everything go through proxies, and last but not least, every command can be adjusted before the execution by disabling the “auto-execute” checkbox.
badKarma is licensed under GNU GPL version 3.
Session file
The Session file is just a sqlite database, it contains all the information gained during the activity, real-time updated it can be exported or/and imported from badKarma’s GUI. By default the database is located inside the “/tmp” directory, this means that you have to save it in a different location before rebooting your computer.
Inside the database, there are four tables: hosts, ports, activity_log and notes.
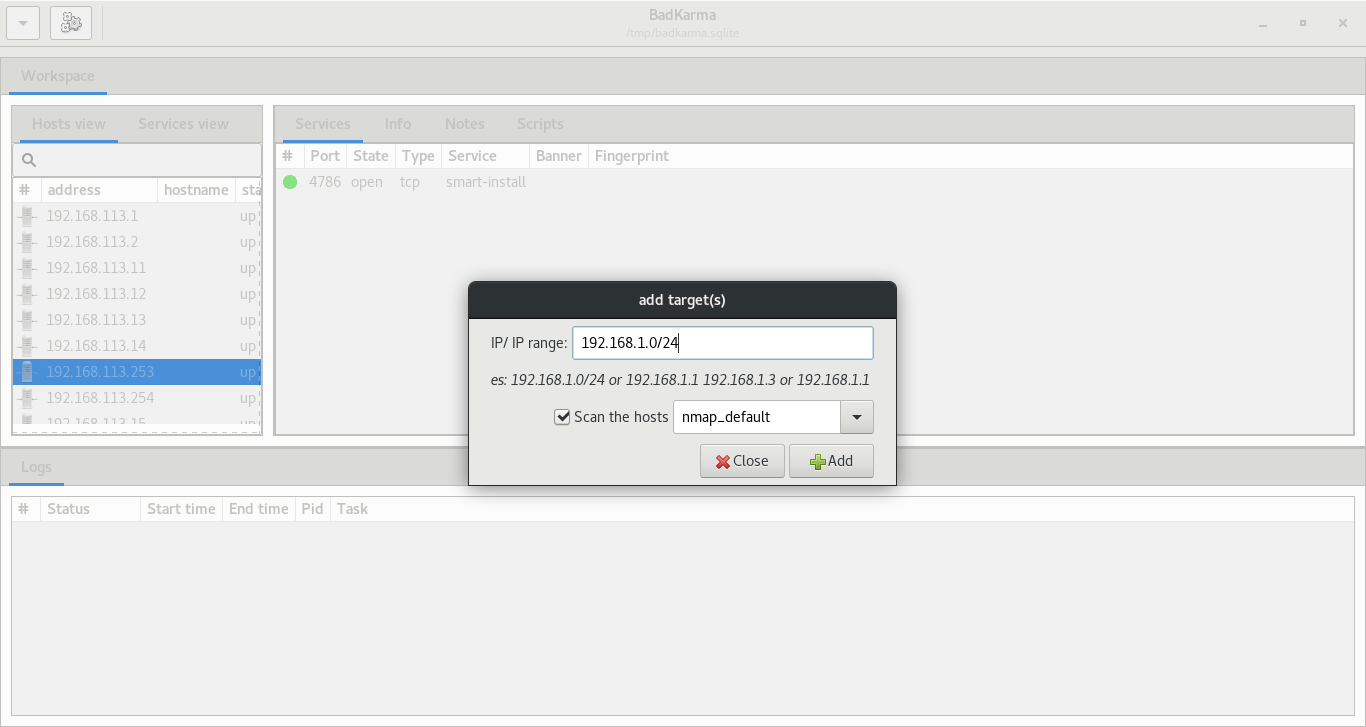
Targets
It is possible to add targets and scan them with nmap and/or masscan from the GUI, some defaults scan profiles are already available as well. It is also possible to import XML scanners result from the main menu.
By default all the scan output are stored inside the “/tmp” directory, then the output is imported into the session file and deleted.
Extensions
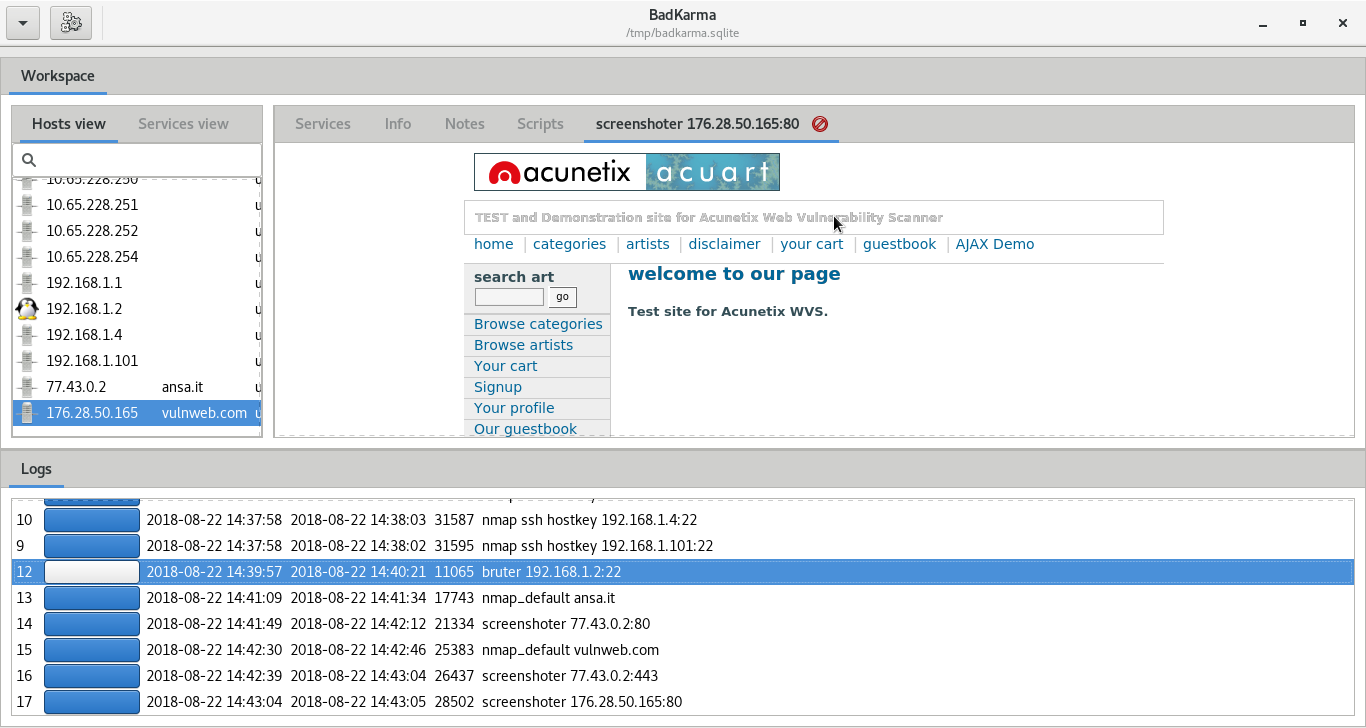
badKarma is modular, the extensions are full-interactive and they allow the penetration tester to tune tasks options since the output is logged under the session file, their output can be exported as a raw txt from the “Logs” tab.
Extensions can be found under the “extension” directory, currently available extensions are:
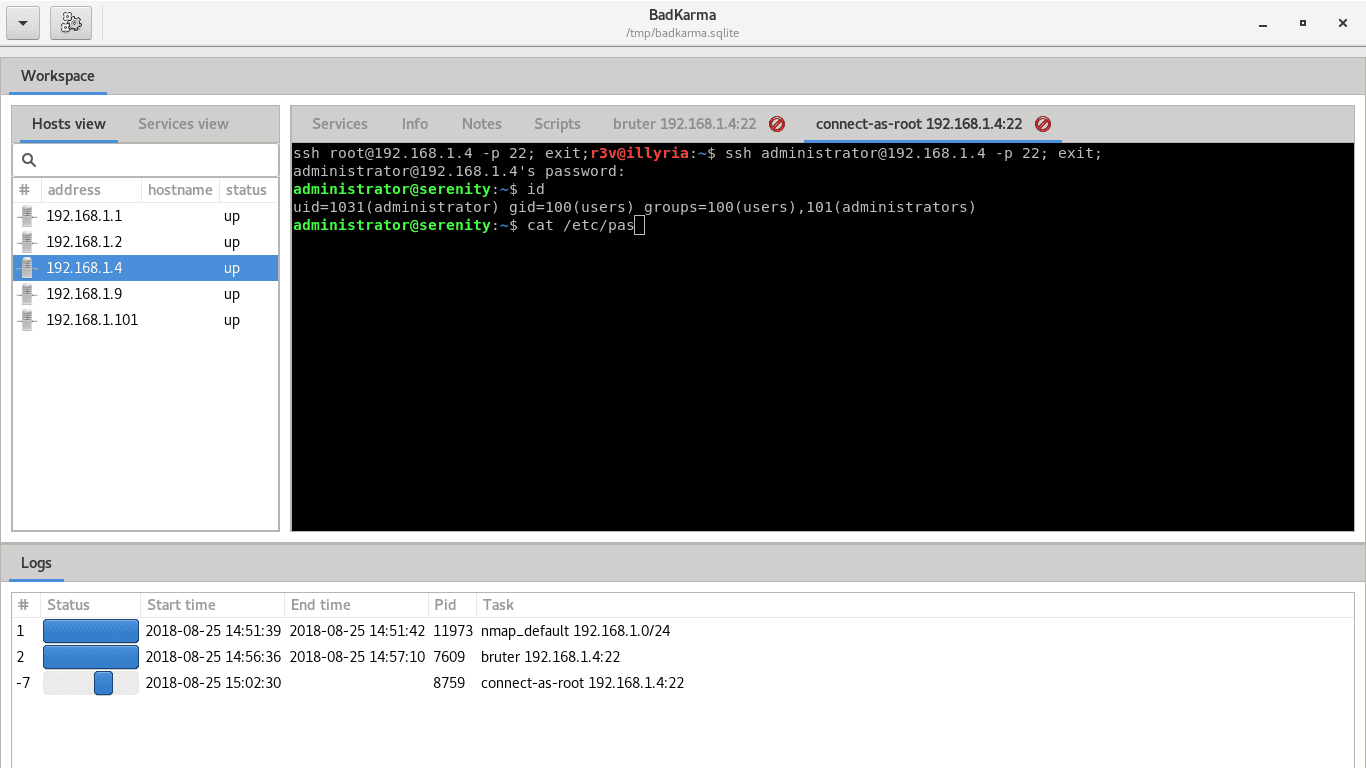
- Shell: this is the main module of the toolkit since it allows the tester to execute preconfigured shell tasks. Shell commands are located under the “conf” directory.
- Bruter: as the name says, more brute is the brute-force extension. It allows the tester to send a target directly to Hydra and configure the parameters through a GUI.
- Screenshot: this extension allows the tester to take a screenshot of possible http,rdp,rtsp,vnc and x11 servers, the screenshot will be stored in the log database as base64 and can be shown from badKarma.
- Browser: just an “open in browser” for http menu item, take it as an example to build your own extensions.
Download
apt install python3-pip python3-gi phantomjs gir1.2-gtk-vnc-2.0 ffmpeg
git clone https://github.com/r3vn/badKarma.git
cd badKarma
pip3 install -r requirements.txt
Use
$ chmod +x badkarma.py
$ ./badkarma.py
Copyright (C) 2018 r3vn
Source: https://github.com/r3vn/