CheeseTools
This repository has been made basing onto the already existing MiscTool, so big shout-out to rasta-mouse for releasing them and for giving me the right motivation to work on them.
CheeseExec
Command Exec / Lateral movement via PsExec-like functionality. Must be running in the context of a privileged user. The tool is based on rasta-mouse CsExec, but is designed to allow additional control over the service creation, specifically:
- Create (Search if the service exists, if not, tries to create it)
- Start (Search if the service exists and is stopped if that’s the case attempts to start it; if not, tries to create it and start it)
- Stop (Search if the service exists and is running if that’s the case attempts to stop it)
- Delete (Search if the service exists and is running, if that’s the case attempts to stop it then delete it, otherwise it deletes it)
CheeseExec.exe <targetMachine> <serviceName> <binPath> <action>
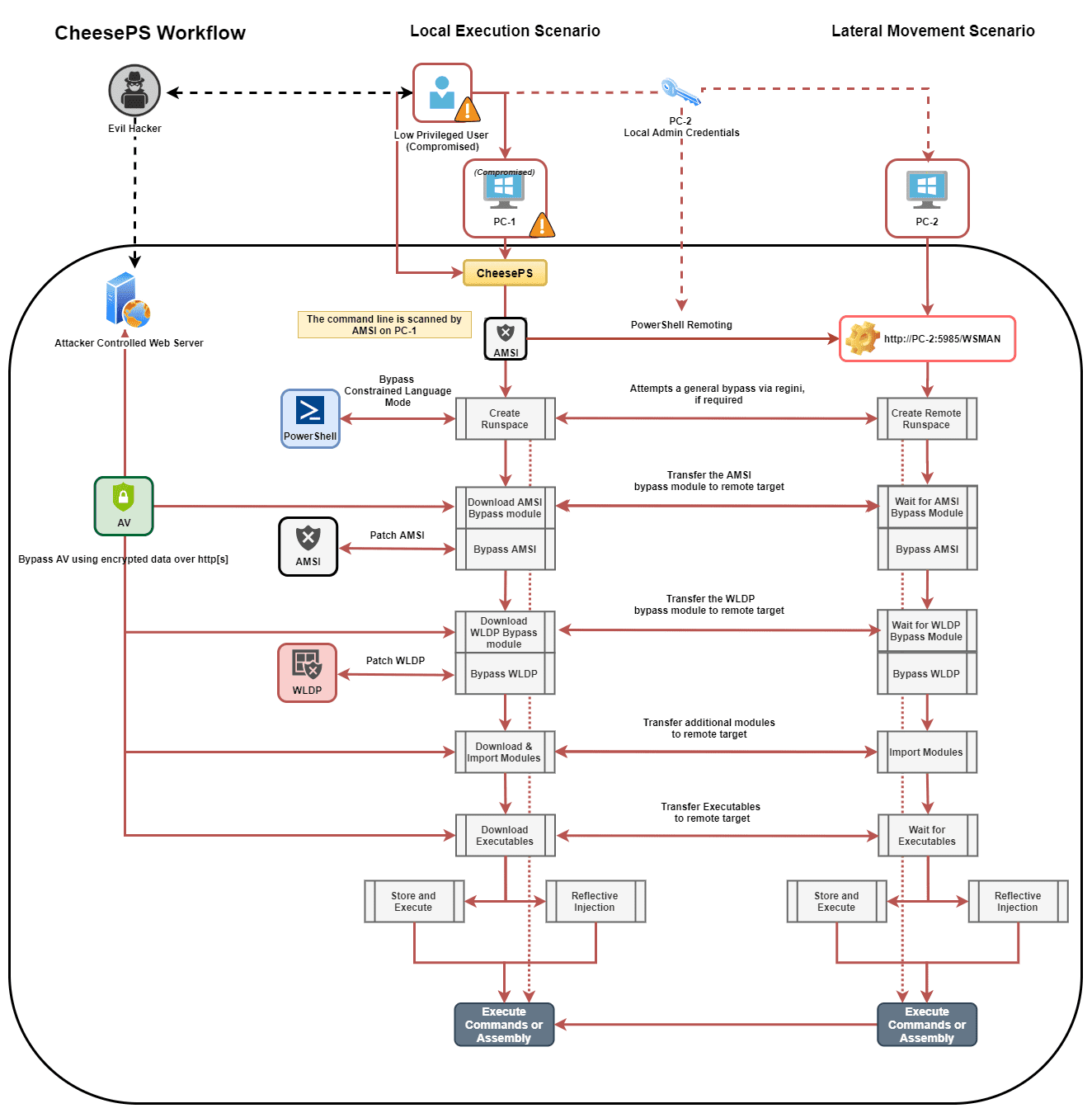
CheesePS
Cheese PS is a Command Exec / Lateral Movement framework. It relies on System.Management.Automation.PowerShell to load and run arbitrary code via PowerShell. The tool is natively capable of bypassing common restrictions creating and using PowerShell runspaces on local or remote targets. Must be running in the context of a privileged user (if using PowerShell Remoting).
The tool has been originally made as an enhancement of rasta_mouse CsPosh but grew enough to become a framework on its own, and can now be used as a general PowerShell injector.
The idea behind this tool has been summarised in the following article:
The main functionalities implemented are:
- BuiltIn CLM Bypass using REGINI
- BuiltIn AmsiBypass that patches Amsi before executing any other command
- Permits to specify an alternate PowerShell script for AMSI bypass
- BuiltIn WldpBypass that patches WLDP before executing assemblies
- Permits to specify an alternate PowerShell script for WLDP bypass
- Import modules and script before execution
- Against a local target: modules are imported via filesystem, smb, or http[s]
- Against a remote target: modules are loaded directly from the local machine using WS-Management
- Download binary and execute
- Standard: Transfer -> Write to disk -> Execute
- Reflective: Transfer -> Execute from memory
- Supports AES Encryption of PS modules, C# assemblies, and other executables to evade detection
- All imported Modules/Assemblies can be encrypted in transit or at rest, and are decrypted just before usage
The following screenshot is a decently accurate schema to describe the tool’s workflow:
Note: If executed without a target, the script will execute against the local machine
Advantages of using the tool against raw PowerShell:
- Cleaner, more intuitive command line
- Automatic bypasses (CLM, AMSI, WLDP)
- Avoids to perform outbound connections from the remote target (everything is transferred through WS-Management)
- Supports full encryption in transit
CheeseDCOM
Command Exec / Lateral Movement via DCOM. Must be running in the context of a privileged user. This tool is based on rasta-mouse CsDCOM, but it’s been improved to add additional methods, adapting to the new research made by Philip Tsukerman. There is also an experimental method to “fix” eventual attempts to disable affected DCOM objects via dcomcfg, but it requires some preconditions in order to work properly.
The idea behind this tool has been summarised in the following article:
Current Methods: MMC20.Application, ShellWindows, ShellBrowserWindow, ExcelDDE, VisioAddonEx, OutlookShellEx, ExcelXLL, VisioExecLine, OfficeMacro.
Also, see Lateral Movement Using DCOM Objects and C#
CheeseRDP
RDP credentials stealer via RDI (reflective DLL injection). Must be running in the context of a privileged user, or a user with SeImpersonatePrivilege. This tool is built on top of RdpThief by MDSec, but it’s been fully wrapped in a single C# to enable it to be run via .NET Reflection (Assembly.Load and similar). In this way, it’s possible to run it via Covenant, without the struggle of uploading a DLL on the target system.
Note: If executed without options, the program will try to inject in an active mstsc.exe process (the default wait time is 10 seconds)
Download
Copyright (C) 2020 klezVirus