OWSAP Damn Vulnerable Web Sockets: vulnerable web application
OWASP Damn Vulnerable Web Sockets (DVWS) is a vulnerable web application which works on web sockets for client-server communication. The flow of the application is similar to DVWA. You will find more vulnerabilities than the ones listed in the application.
https://www.owasp.org/index.php/OWASP_Damn_Vulnerable_Web_Sockets_(DVWS)
Changelog
| 2021-05-24 | |
| – Added heartbeat functionality in “ws-socket.php” file | |
| – Updated heartbeat command in “index.php” file | |
| – Updated formatting in “index.php” file | |
| – Removed “vendor” folder and “composer.lock” file | |
| – Updated README.md file |
Requirements
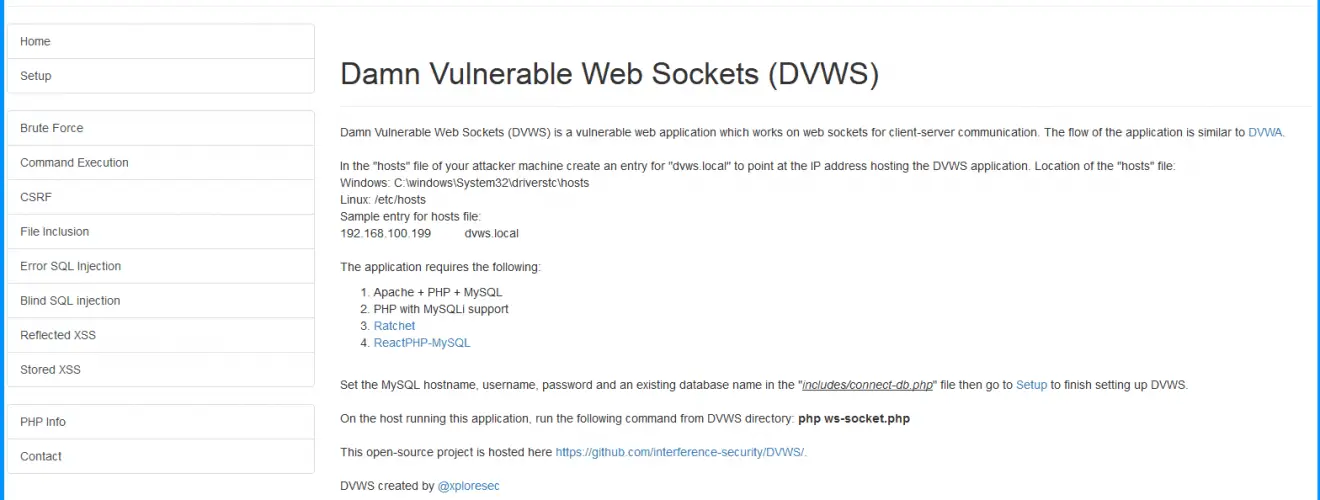
In the hosts file of your attacker machine create an entry for dvws.local to point at the IP address hosting the DVWS application.
Location of hosts file:
Windows: C:\windows\System32\drivers\etc\hosts
Linux: /etc/hosts
Sample entry for hosts file:
192.168.100.199 dvws.local
The application requires the following:
Apache + PHP + MySQL
PHP with MySQLi support
Note: Ratchet and ReactPHP-MySQL are packaged inside DVWS. Separate installation might not be required.
Setting up DVWS
git clone https://github.com/interference-security/DVWS.git
Set the MySQL hostname, username, password and an existing database name in the includes/connect-db.php file then go to Setup to finish setting up DVWS.
Running DVWS
On the host running this application, run the following command from DVWS directory: php ws-socket.php
Important Note
DVWS has been developed with limited knowledge of Web Sockets. Feel free to contribute and enhance this project.






