gimmecredz: quickly dump all credz
Objective
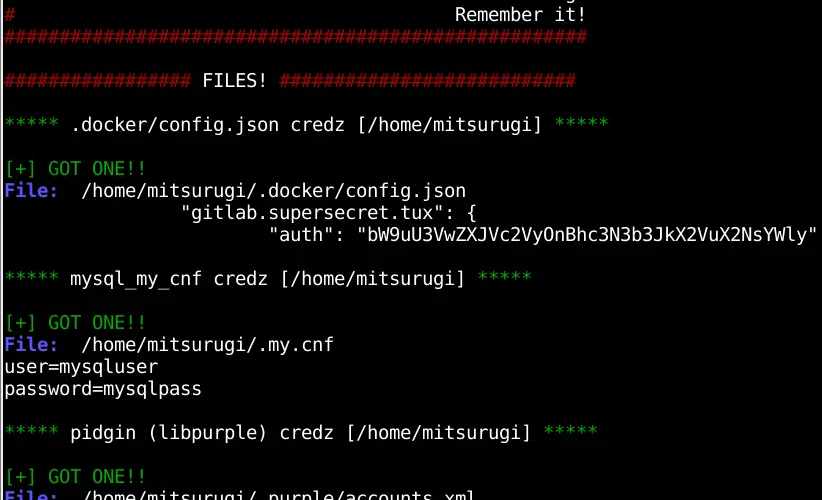
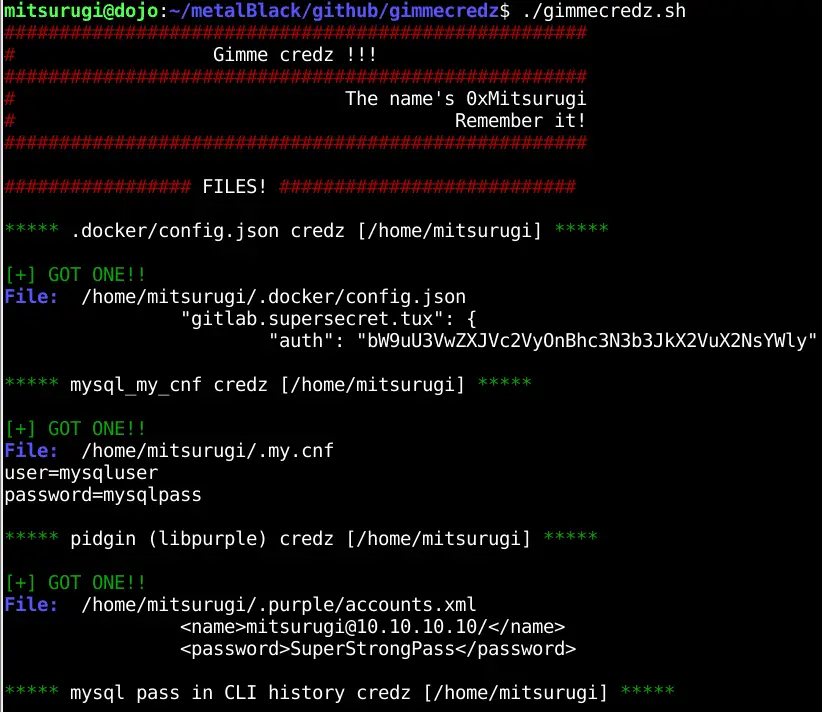
This tool can help pentesters to quickly dump all credz from known location, such as .bash_history, config files, wordpress credentials, and so on… This is not a hacking tool, just a collection of well-known files with password in them. The password can be in clear, base64 or enciphered form. It’s up to the pentester to use them, decode them or change them. This tool can be launch by root or any users, it will autodetect file access and adapt accordingly.
Goals
- this tool is in bash because bash is everywhere, and I wanted it to be the most compatible with all pwned systems without having to install any third party lib/shell/script language.
- this tool should be easy to read/tweak and easy to add new password dumps
- this tool should not be taken too seriously
- this tool uses mainly bash with a little bit of grep (egrep), find and some other usual tools.
- I don’t care if this tool fails softly on one or another files. I prefer a simple tool with little fails than an heavier tool bloated with failchecks and sanity verification.
- this tool should work quick, for this reason I don’t want some hasardous find, such as:
find / -type f -exec grep password {} \;find is limited with maxdepth 3 at most - this tool should be autodocumented. Read it.
- this tool is not sponsored by the NSA and won’t send your credz to any thirdparty.
Usage
Easy usage:
wget https://raw.githubusercontent.com/0xmitsurugi/gimmecredz/master/gimmecredz.sh
chmod +x gimmecredz.sh
./gimmecredz.sh
Or, for the l33t:
$ curl https://raw.githubusercontent.com/0xmitsurugi/gimmecredz/master/gimmecredz.sh | bash
Check the start of the script. You can set vars. Currently, you can force to check root-owned files even if you are using (in hope of misconfiguration of the targets). You can also put a script in verbose where it shows everything, even failures.
Key extraction:
Except for “root access”, all files are check. If it’s related to /home and if you’re root, it will loop for all users.
Root access
- print inf if a user has a shell in a shadow file
- WPA password store in wpa_supplicant or NetworkManager
- grub password
- ldap password
- password in fstab
- All other checks are done for root, and for
Files with credz
- .docker/config.json
- mysql mycnf
- pidgin (libpurple)
- postgresql
- mysql and rdesktop pass stored in (z|ba)sh history
- presence of a –password in (z|ba)sh history
- ssh keys (protected bypass, and unprotected)
- keepassx databases (ability to tell if it’s currently open)
Browsers
- Firefox logins.json and key3.db
- Chrome Login data
Webapps
- wordpress credz
- drupal credz
Source: https://github.com/0xmitsurugi/






