HWSyscalls
HWSyscalls is a new method to execute indirect syscalls using 3 main components:
-
Hardware breakpoints and Vectored Exception Handler to control the flow of execution.
-
HalosGate is used to find syscall numbers and addresses.
-
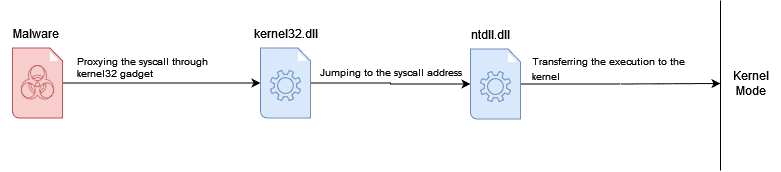
Creating a synthetic trampoline on kernel32 with hardware breakpoints.
HWSyscalls is provided as an easy-to-include library that can be added to any project that wants to use indirect syscalls without triggering EDRs or AVs detections based on the current indirect syscalls detection.
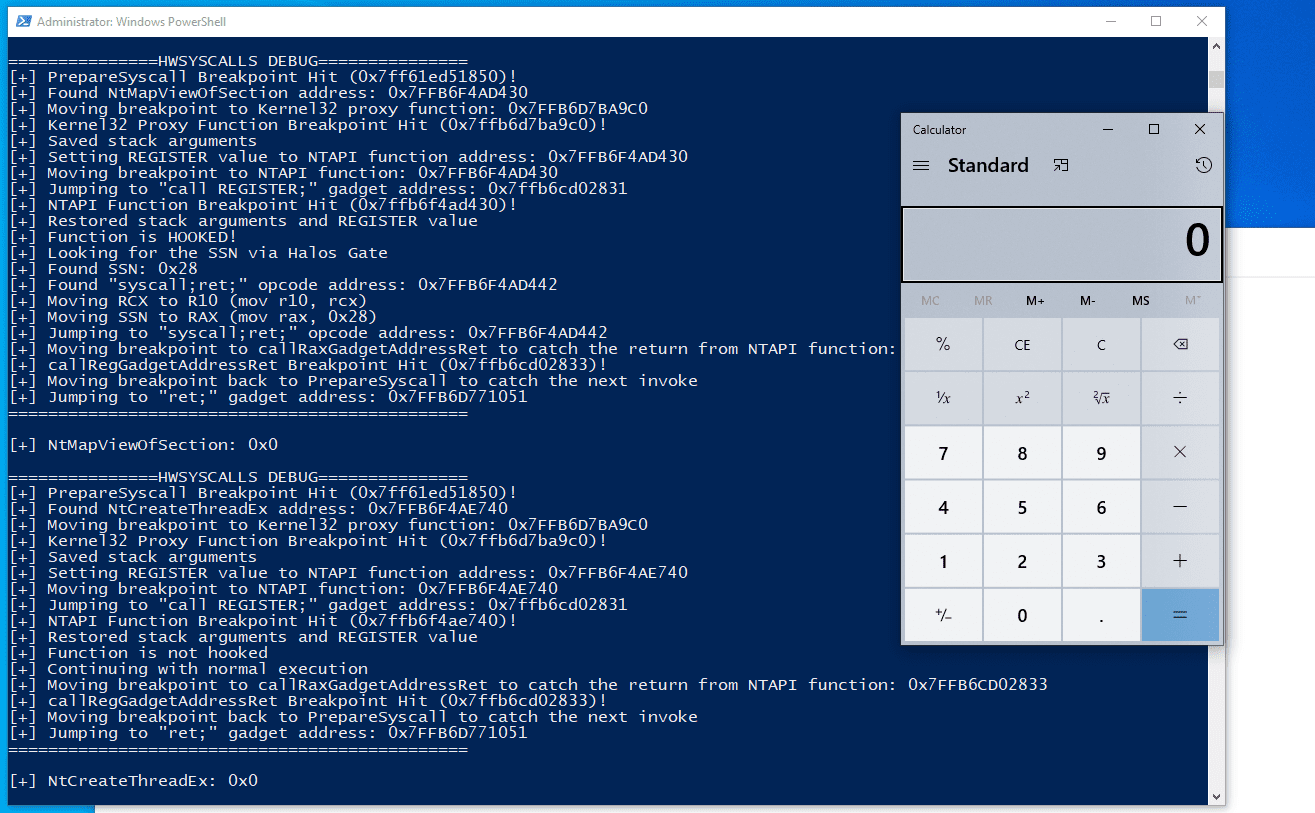
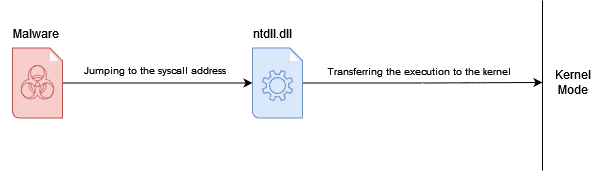
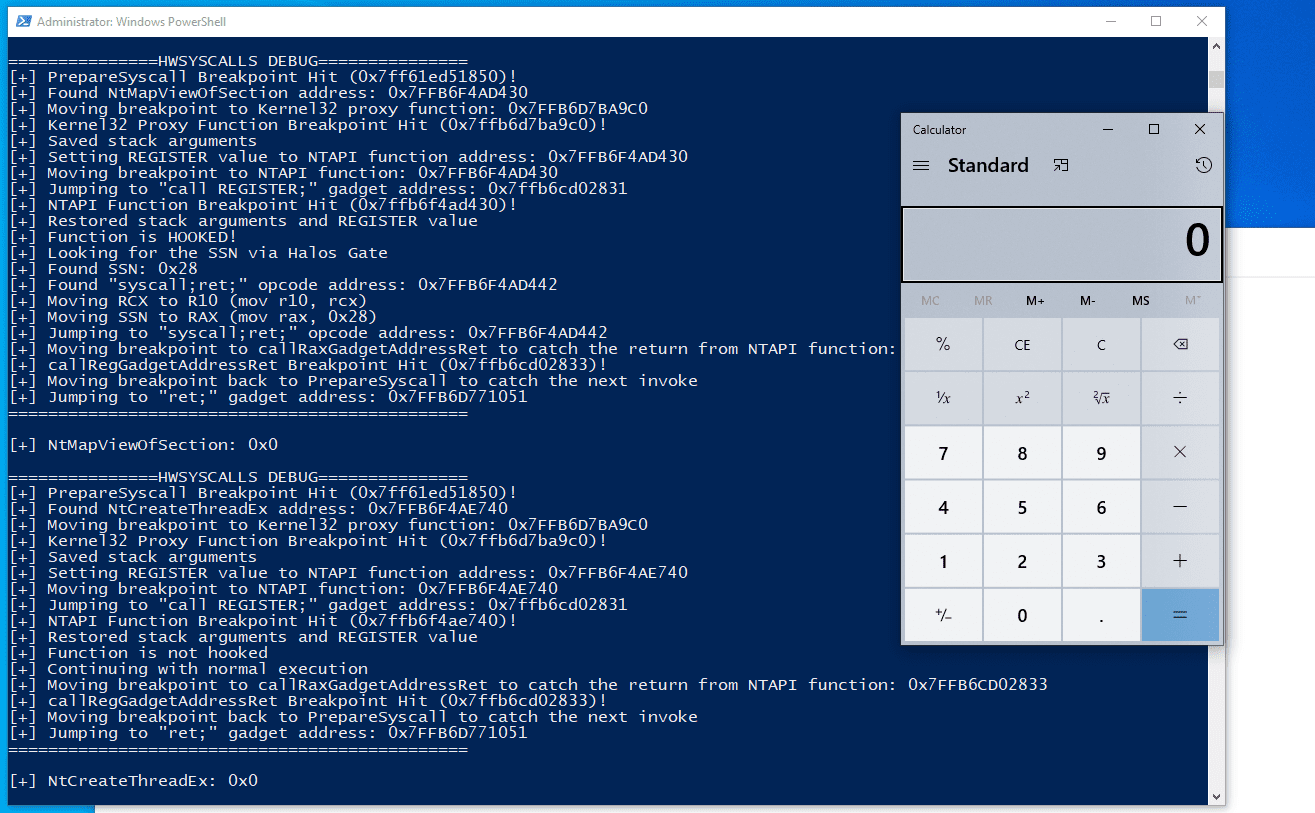
Indirect syscalls is a popular method that is used in different variations to call system calls from ntdll, however, the main issue with calling syscalls from ntdll is in its core: A weird access from a program directly to ntdll, without going through any previous dll. HWSyscalls is built upon the core idea of indirect syscalls but with a solution to this problem by combining hardware breakpoints functionality to create the synthetic trampoline in kernel32 and HalosGate to get the SSNs.
To make it easy, a normal indirect syscalls flow looks like this:
While ours looks like this:
Usage
To use the project, you will need to include the HWSyscalls.h and call InitHWSyscalls to find the required gadgets and initialize the exception handler. At the end of your program’s execution, call DeinitHWSyscalls to remove the exception handler.
The debug verbosity can be turned on or off by changing the HWSYSCALLS_DEBUG definition in HWSyscalls.h