iMonitor v2.5 releases: Endpoint Behavior Analysis System

iMonitor
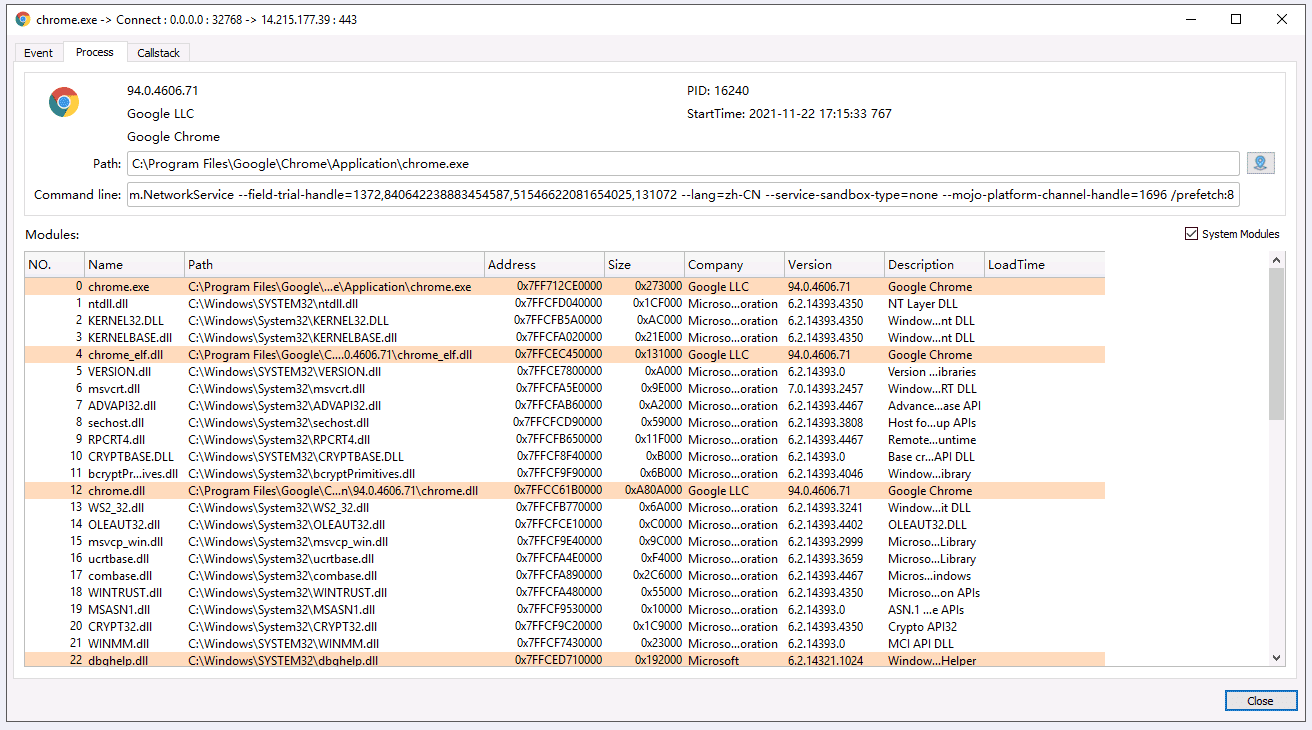
iMonitor (Endpoint Behavior Analysis System – Then Open Source Procmon) is an endpoint behavior monitoring and analysis software based on iMonitorSDK.
Provides monitoring of system behaviors such as processes, files, registry, and networks. Support extensions and scripts, you can easily customize and add more functions. It can be used for virus analysis, software reverse engineering, intrusion detection, EDR, etc.
Some features
- Open-source
- Support 32-bit and 64-bit systems from Win7 to Win11 (Because Qt uses a newer version and does not support XP, you can replace it with a Qt version that supports XP if you need to support it)
- Support rich behavior monitoring, process open events, and various operation events of sockets
- Support filter conditions for each event field and filter conditions for stack modules
- All behaviors monitored by iMonitor can be blocked by iMonitorSDK, iDefender
- Support scripting and application market, unlimited expansion and customization functions (to be supported)
Plan
-
Complete basic functions
- Support data saving and loading
- Support rule saving, the rule list
- Support process, file, registry, network information summary
- Support search, quick filter, label
- Column supports customization, editing, display, and hide
- Improve QSS and internationalization
-
Plugin extension
- Support plugin extension
- Support script extension
- Key plugin
- Filter plugin: support more complex condition filtering
- Display plugin: add more information display
- Behavior plugin: you can analyze the meaning of each path
- Security plugin: According to the weight of the behavior, intelligently analyze the virus behavior
- Reverse plugin: automatically filter out the system path, quickly analyze which data is stored and modified by a software
- Development platform-Application market support
-
Detection analysis and response
- Combined with the iDefender active defense system, quickly disable the detected behavior
- Data support report integration into EDR, SOC, SIEM, and other platforms






