Jomungand
Shellcode Loader with memory evasion by @DallasFR
How does it work?
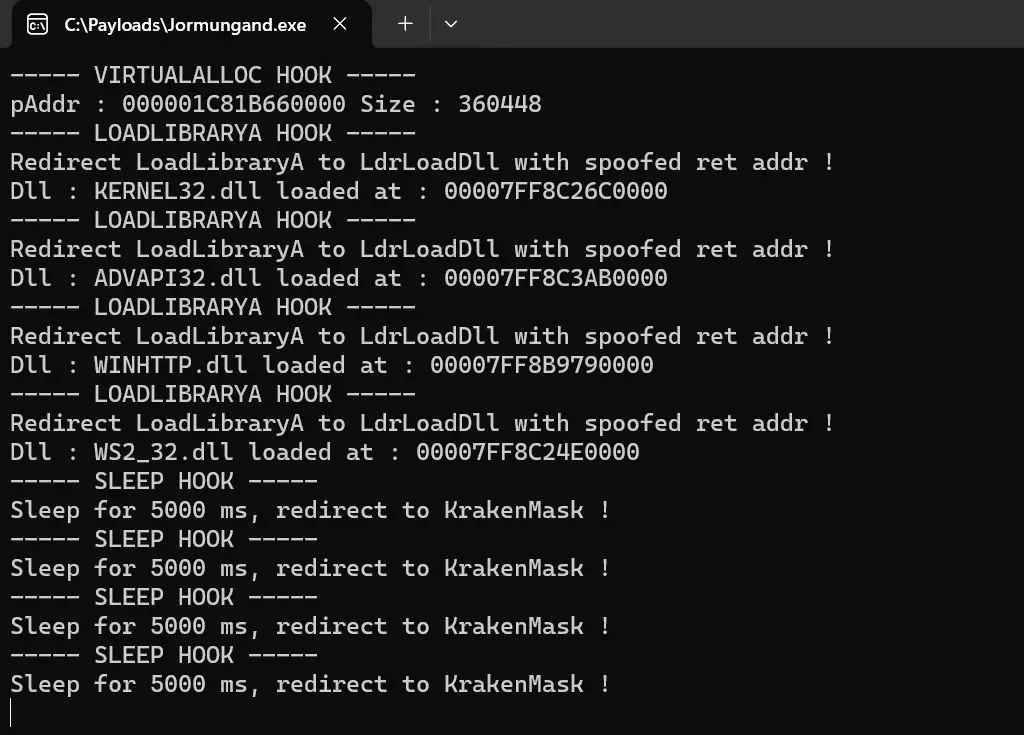
I use HWBP to hook VirtualAlloc, Sleep, and LoadLibraryA. Why do I hook this function?
-
VirtualAlloc: CobaltStrike & Meterprter is reflective dll as shellcode, with the VirtualAlloc hook we can obtain the real address of shellcode in memory
-
Sleep: I hook sleep to use KrakenMask and encrypt all the content of shellcode in memory during sleep
-
LoadLibraryA: I redirect to LdrLoadDll with ret addr spoofing. Some edr can detect malicious LoadLibraryA if the origin of the call is not backed on RX present on the disk
All NT API call was made with an indirect syscall and I spoofed the ret addr.
When the first sleep was called, I freed the virtual memory allocated to read the shellcode from a file.
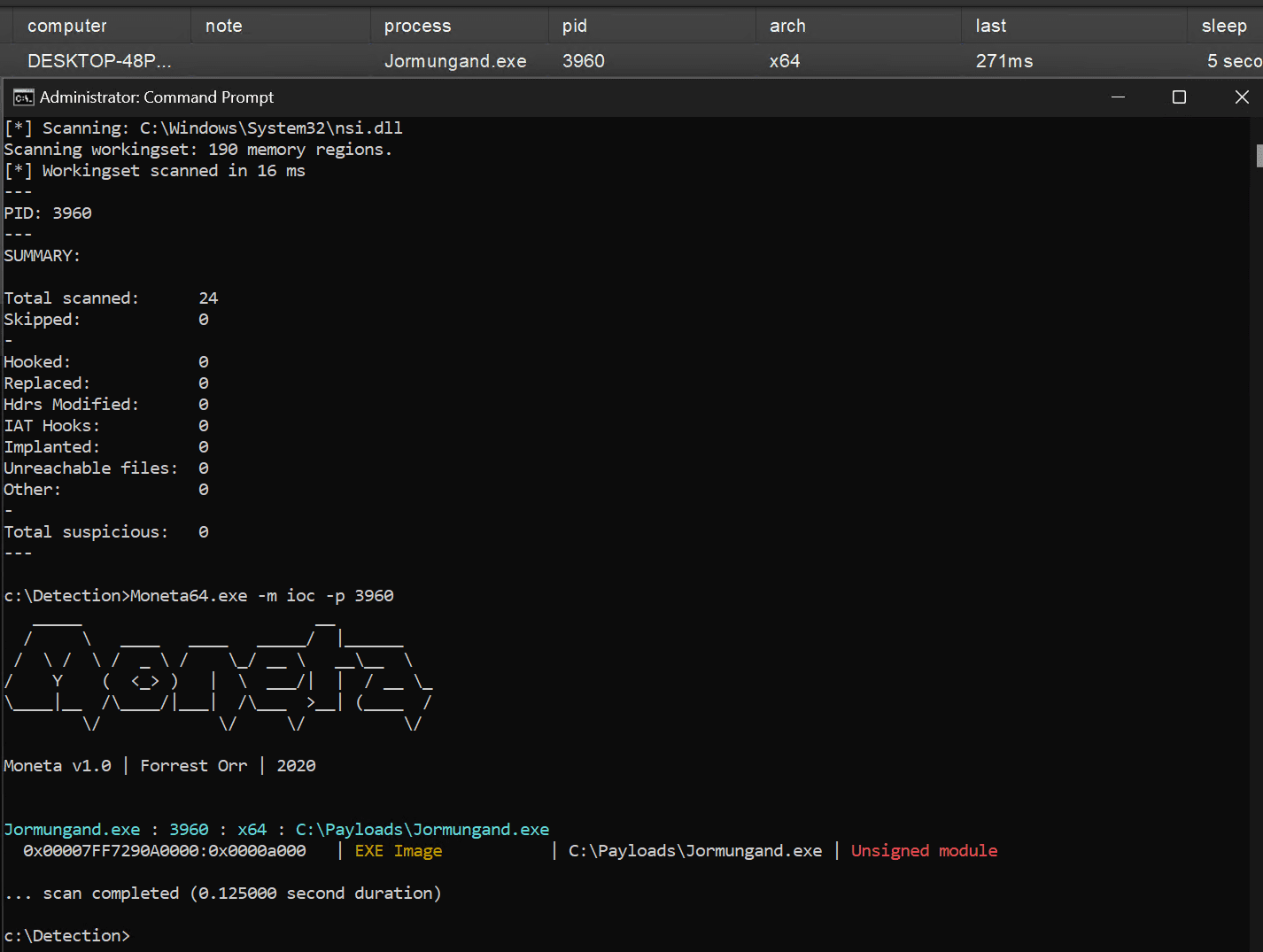
Memory scanner
- PE-Sieve: Detect nothing
- Moneta: 1 Detection, the exe image is an unsigned module
- Hunt sleeping beacons: Detect nothing
- Patriot: Detect nothing