jsprime: a javascript static security analysis tool for finding DOM-XSS

Both in the traditional PC Web platform or mobile terminal platform, client-side or server-side, the JavaScript fairly good performance and reflect the rich framework to support, so it as a mainstream development language has gradually been accepted widely recognized. At the same time, JavaScript also because of its interpreter performance advantages, for enterprises to solve scalability and throughput bottlenecks. Therefore, JavaScript is currently an important, powerful development language, its users are also increasing.
But the problem is that with the emergence of a growing number of JS libraries and many developers in function-oriented, sometimes there will be unsafe coding, which also led to a number of client-side attack events, Among them, DOM XSS is the most popular. Before the development of this tool, we try to analyze the code caused DOM XSS attack trigger points, but unfortunately, there were no sufficiently effective tools to analyze and solve problems. So we started trying to develop tools to analyze the code level to solve the problem, we will be here on this code audit tools DOM XSS attacks JSPrime defined as a JavaScript static analysis tool, code audit, and it is a Lightweight and easy-to-use point-and-click tool! Among them, the static analysis function module is based on the current very popular Esprima ECMAScript syntax parsing.
Download
git clone https://github.com/dpnishant/jsprime.git
JSPrime main function points
1, support positioning analysis JS framework or library Source and Sinks;
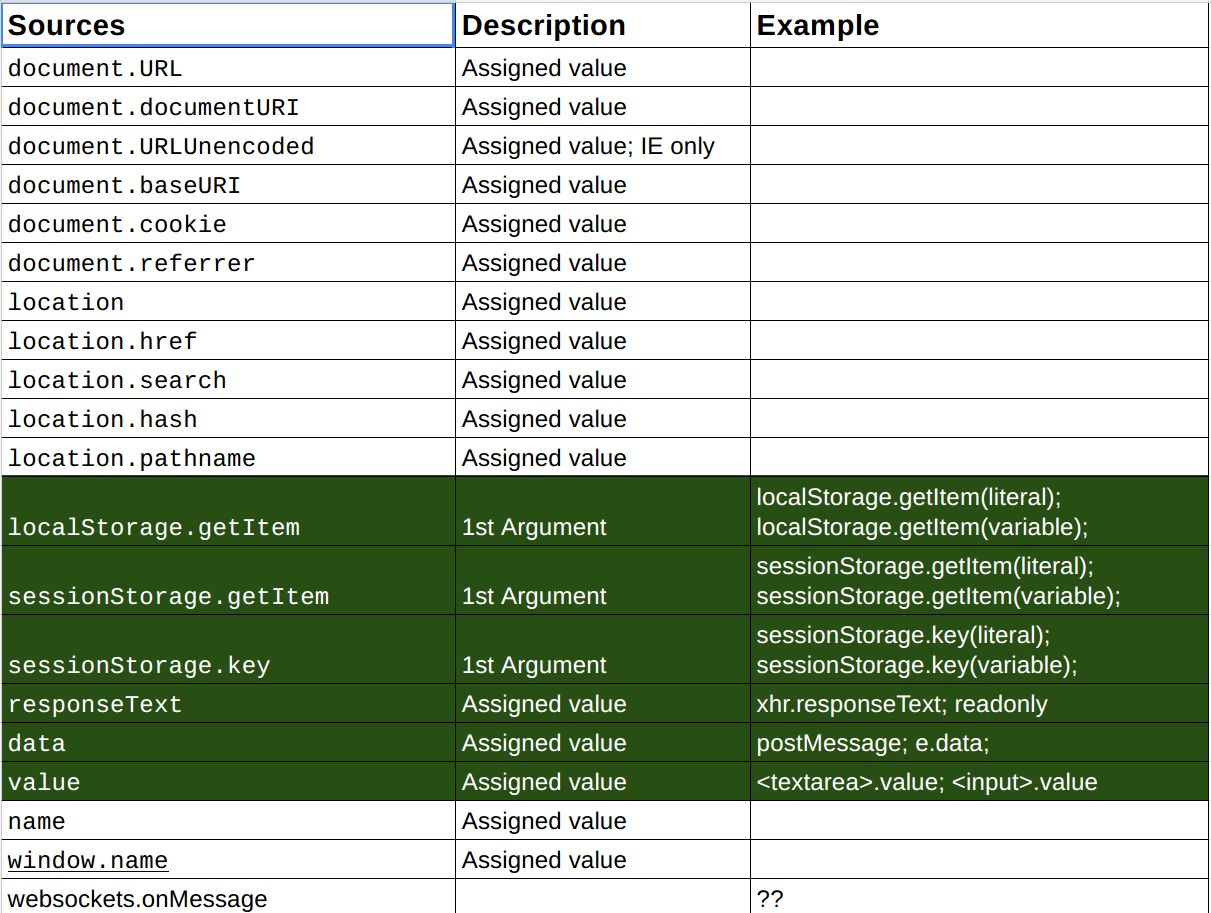
2, many dynamic or static analysis tool development often only supports pure JavaScript syntax and functionality, but for most developers, this is a problem, because the development process, usually uses some JavaScript framework or library, such as jQuery, YUI and many more. Because these scanners are designed to support pure JavaScript syntax checking, they are less mature in understanding the content of code development and are prone to false positives. So to solve this problem, JSPrime is based on jQuery and YUI frameworks such as the user’s input dangerous nature of the source and the source code is executed sink input function were detected and analyzed. The following is part of Source and Sinks of specific information, detailed view: Source & Sinks
3, variable and function tracking and positioning;
4, variable and function range limit analysis;
5, identify the known filter function;
6, object-oriented (OOP) analysis and prototype code design compliance;
7, the minimum false alarm rate;
8, support Minified.js library (the library features include DOM operations, events, animation, cookies and HTTP requests);
9, rapid analysis of retrieval capabilities;
10, click-type operation (tools without a variety of complex operations, easy to use).
Installation steps
1, Web-side operation
Open “in the browser index.html .”
2, the server-side operation
(1) If there are no installation Node.js, please visit: Node.js official website to download;
(2) to complete the first step, in the terminal to open the file from GitHub previously downloaded server.js, the specific command is as follows,
node server.js(3) After the server is turned on, enter in your browser: 127.0.0.1:8888.
DOM XSS analysis
Server-Side (Node.JS)
- Paste javascript inbox, and click Analyze button
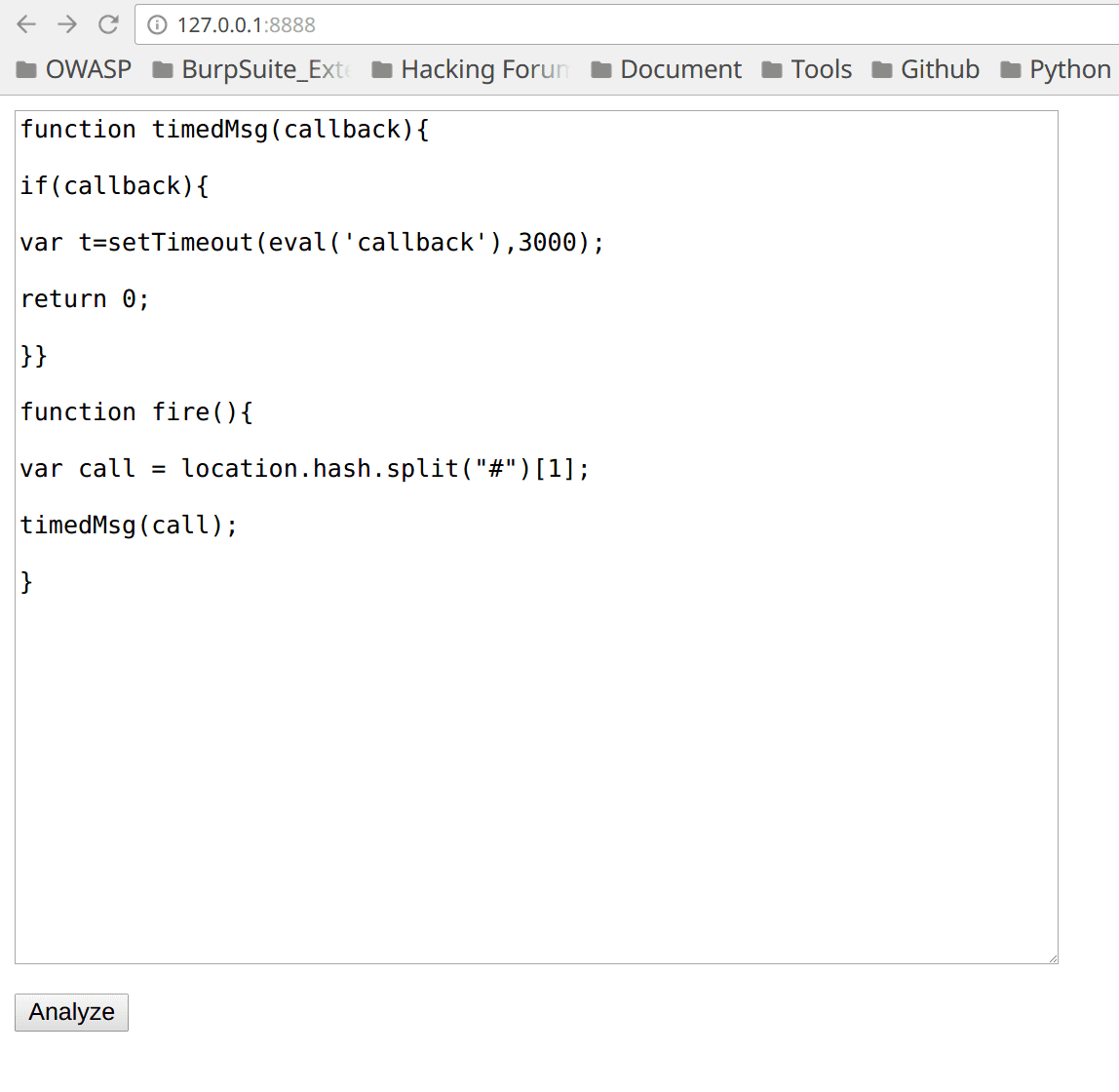
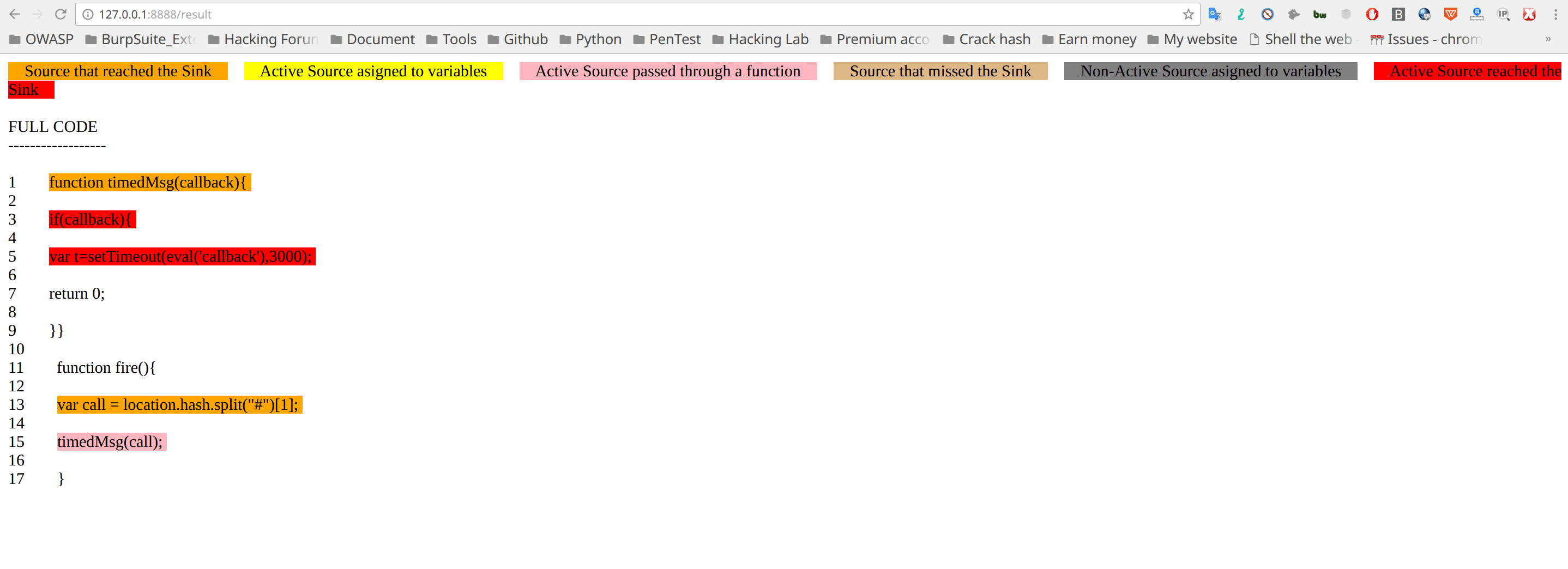
- View result
Web Client
Open “index.html” in your browser.
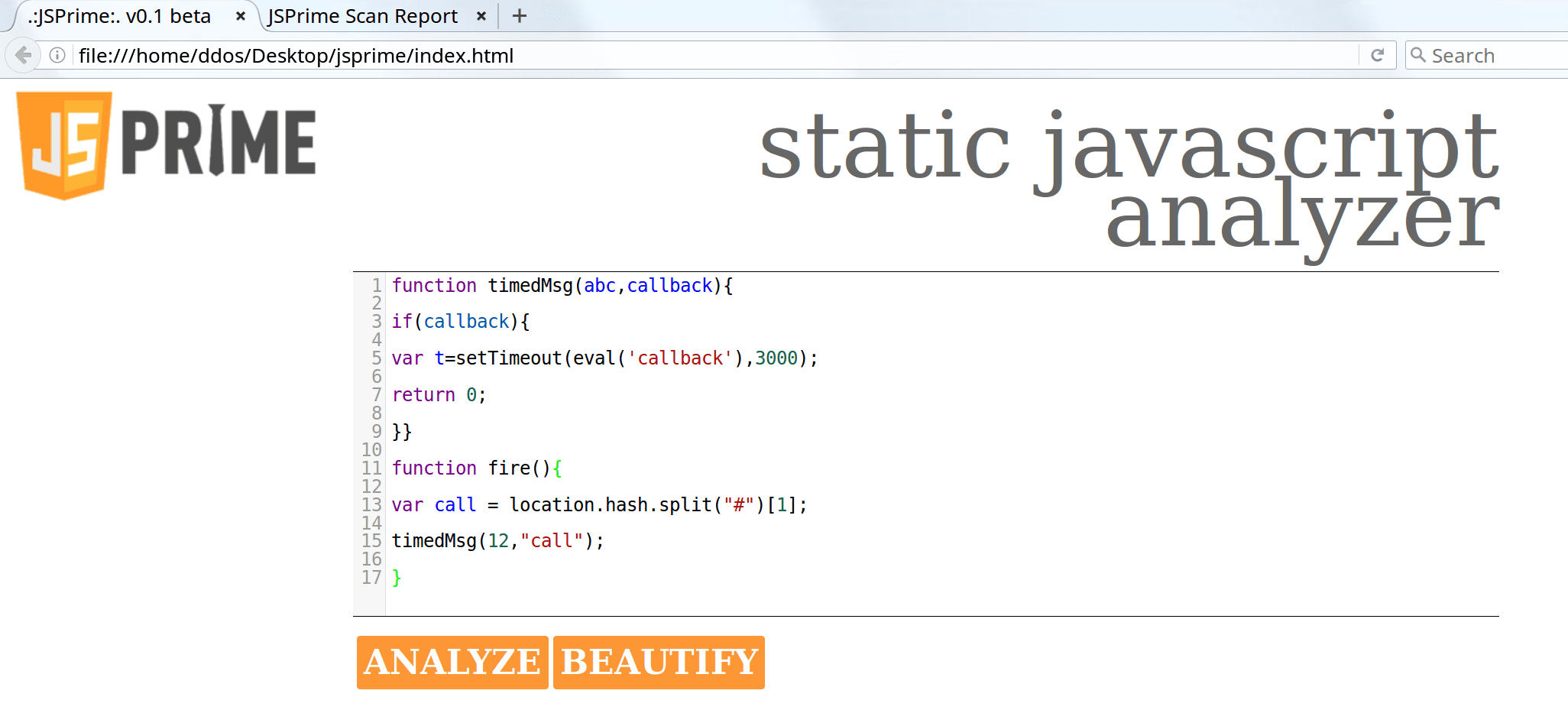
Click ANALYZE
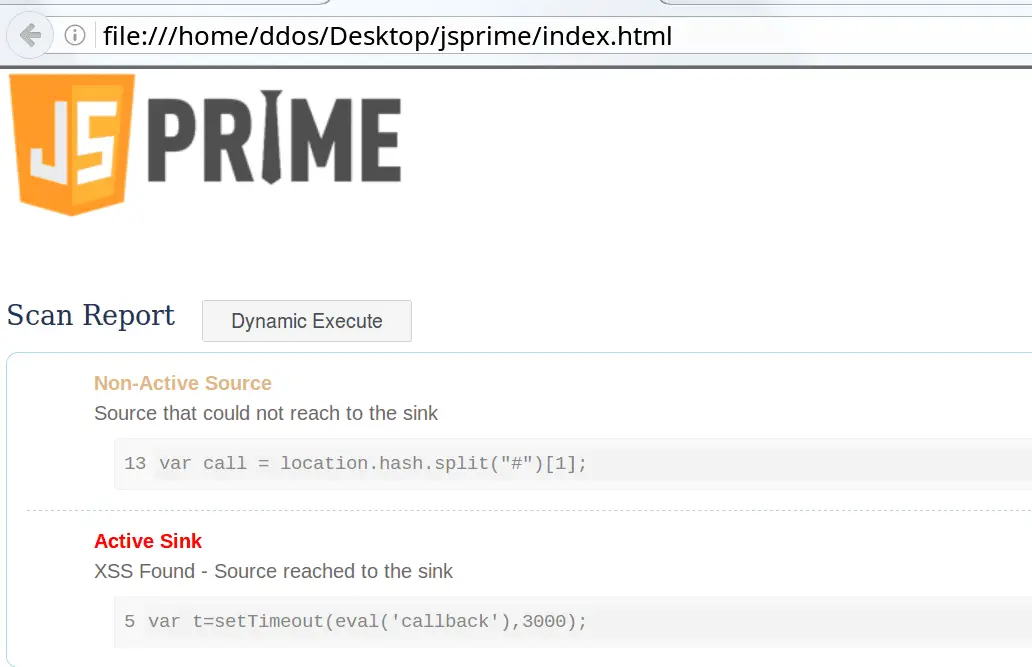
Click Dynamic Execute
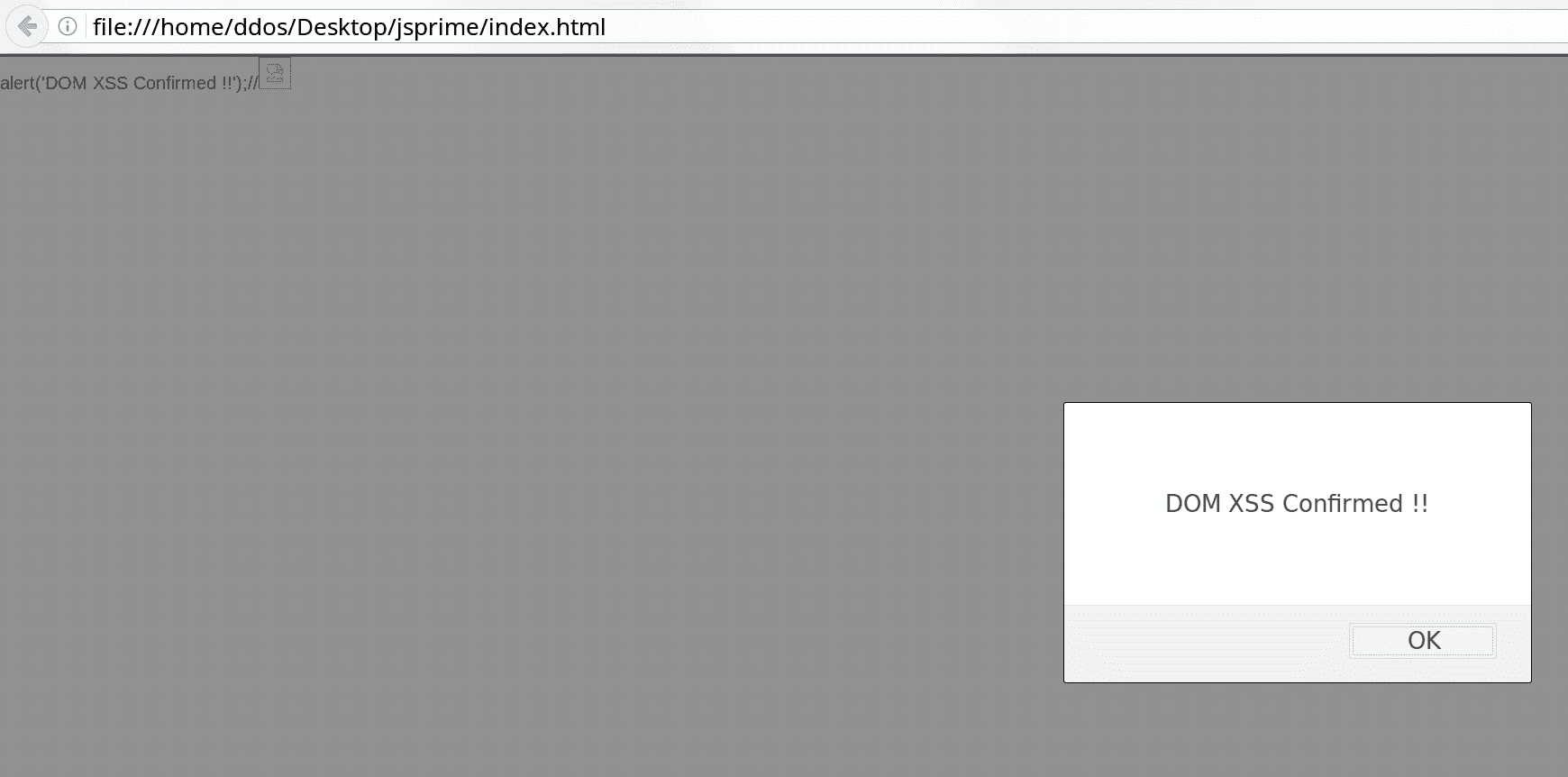
DEMO
Copyright (c) 2013 Nishant Das Patnaik (nishant.dp@gmail.com)
Copyright (c) 2013 Sarathi Sabyasachi Sahoo (sarathisahoo@gmail.com)






