kubeshark v52 releases: API traffic analyzer for Kubernetes
kubeshark
Kubeshark is an API Traffic Analyzer for Kubernetes providing real-time, protocol-level visibility into Kubernetes’ internal network, capturing and monitoring all traffic and payloads going in, out, and across containers, pods, nodes, and clusters.
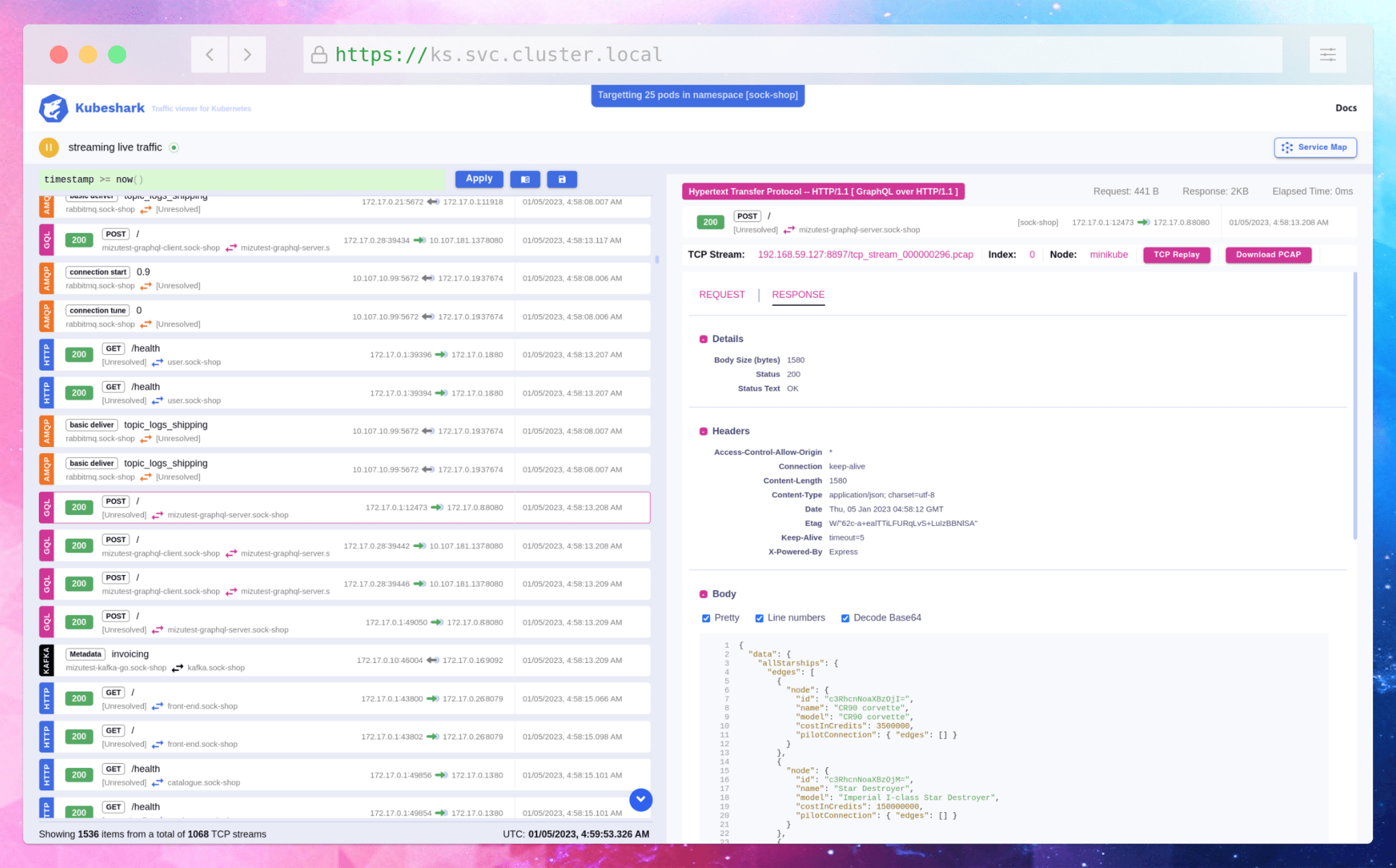
Think TCPDump and Wireshark re-invented for Kubernetes
Network Analysis
Kubeshark can sniff parts or all OSI L4 (TCP and UDP) traffic in your cluster, record it into PCAP files and dissect the following application layer protocols:
Kubeshark recognizes gRPC over HTTP/2, GraphQL over HTTP/1.1, and GraphQL over HTTP/2.
Kubeshark uses extended BPF (eBPF) to trace function calls in both the kernel space and the user space.
Kubeshark can sniff the encrypted traffic (TLS) in your cluster using eBPF without actually doing decryption. In fact, it hooks into entry and exit points in certain functions inside the OpenSSL library and Go’s crypto/tls package.
Kubeshark can recognize service mesh solutions like Istio, Linkerd, and other service mesh solutions that use Envoy Proxy under the hood.
Actionable Automation, Scripts & L4/L7 Hooks
With a combination of a scripting language, hooks, helpers, and jobs, Kubeshark can detect suspicious network behaviors and trigger actions supported by the available integrations (e.g. Slack, AWS S3, InfluxDB, Elasticsearch, and more).
Changelog v52
This release introduces a new traffic recorder feature, enhanced analysis of half-connections, and more.
Additional Enhancements and Changes
- Traffic Recorder: A powerful tool for capturing and analyzing network traffic.
- Half-Connection Viewing: Enhanced ability to view half-connections in supported protocols.
- New API Endpoints: Addition of Hub and Worker API endpoints, enabling data consumption via a WebSocket without the need for scripts or dashboard access.
- EFS Persistent Volume Support: Improved storage options with EFS persistent volume support. See Pull Request #1455 for details.
- Security Context Capabilities: Assign security context capabilities based on the features in use, reducing the need for elevated capabilities when they are not necessary.
Install & Use
Copyright 2022 Kubeshark






