Linuxprivchecker.py
linuxprivchecker script is intended to be executed locally on a Linux box to enumerate basic system info and search for common privilege escalation vectors such as world-writable files, misconfigurations, clear-text passwords, and applicable exploits.
Linuxprivchecker is designed to identify potential areas to investigate further, not provide direct action or exploitation. This is to help users further learn how these privilege escalations work and keep it in line with the rules, for self-directed exploitation, laid out for the OSCP, HTB, and other CTFs/exams.
We will try our best to add information and reference where possible. As the current Maintainer, I also plan to accompany new feature adds, with a post on my blog (hackersvanguard.com) to further explain each potential area for privilege escalation and what criteria may be required.
Download
git clone https://github.com/sleventyeleven/linuxprivchecker.git
Use
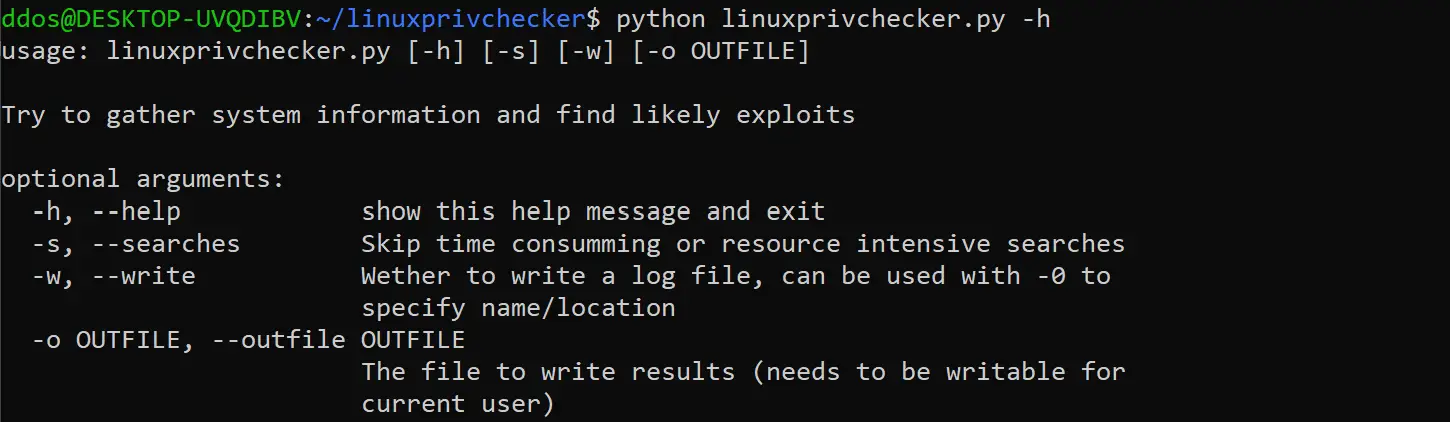
If the system your testing has Python 2.6 or high and/or argparser installed, you can utilize the following options. If importing argparser does not work, all checks will be run and no log file will be written. However, you can still use terminal redirection to create a log, such as ‘python linuxprivchecker.py > linuxprivchecker.log.’
Warning
This script comes as-is with no promise of functionality or accuracy. I have no plans to maintain updates, I did not write it to be efficient and in some cases, you may find the functions may not produce the desired results. For example, the function that links packages to running processes is based on keywords and will not always be accurate. Also, the exploit list included in this function will need to be updated over time. Feel free to change or improve it any way you see fit.
Orginal Author: Mike Czumak (T_v3rn1x) — @SecuritySift
Current Maintainer: Michael Contino (@Sleventyeleven)
Source: https://github.com/sleventyeleven/