MISP v2.4.177 released – Malware Information Sharing Platform & Threat Sharing
MISP – Malware Information Sharing Platform and Threat Sharing
MISP, Malware Information Sharing Platform, and Threat Sharing is an open-source software solution for collecting, storing, distributing, and sharing cybersecurity indicators and threats about cybersecurity incidents analysis and malware analysis. MISP is designed by and for incident analysts, security and ICT professionals or malware reverser to support their day-to-day operations to share structured information efficiently.
The objective of MISP is to foster the sharing of structured information within the security community and abroad. MISP provides functionalities to support the exchange of information but also the consumption of the information by Network Intrusion Detection System (NIDS), LIDS but also log analysis tools, SIEMs.
MISP, Malware Information Sharing Platform, and Threat Sharing, core functionalities are:
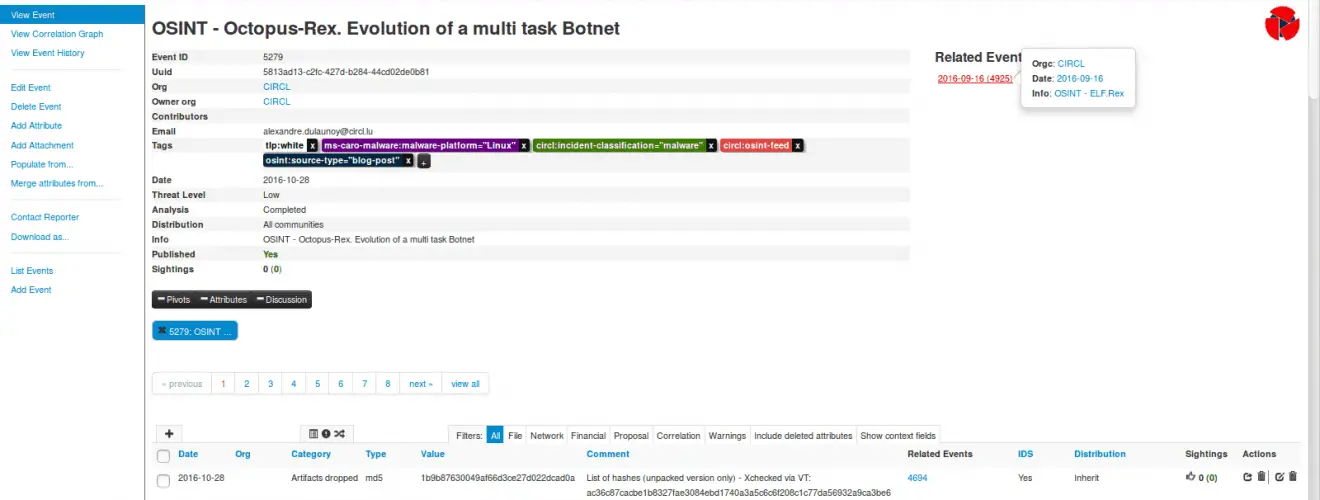
- An efficient IOC and indicators database allowing to store technical and non-technical information about malware samples, incidents, attackers and intelligence.
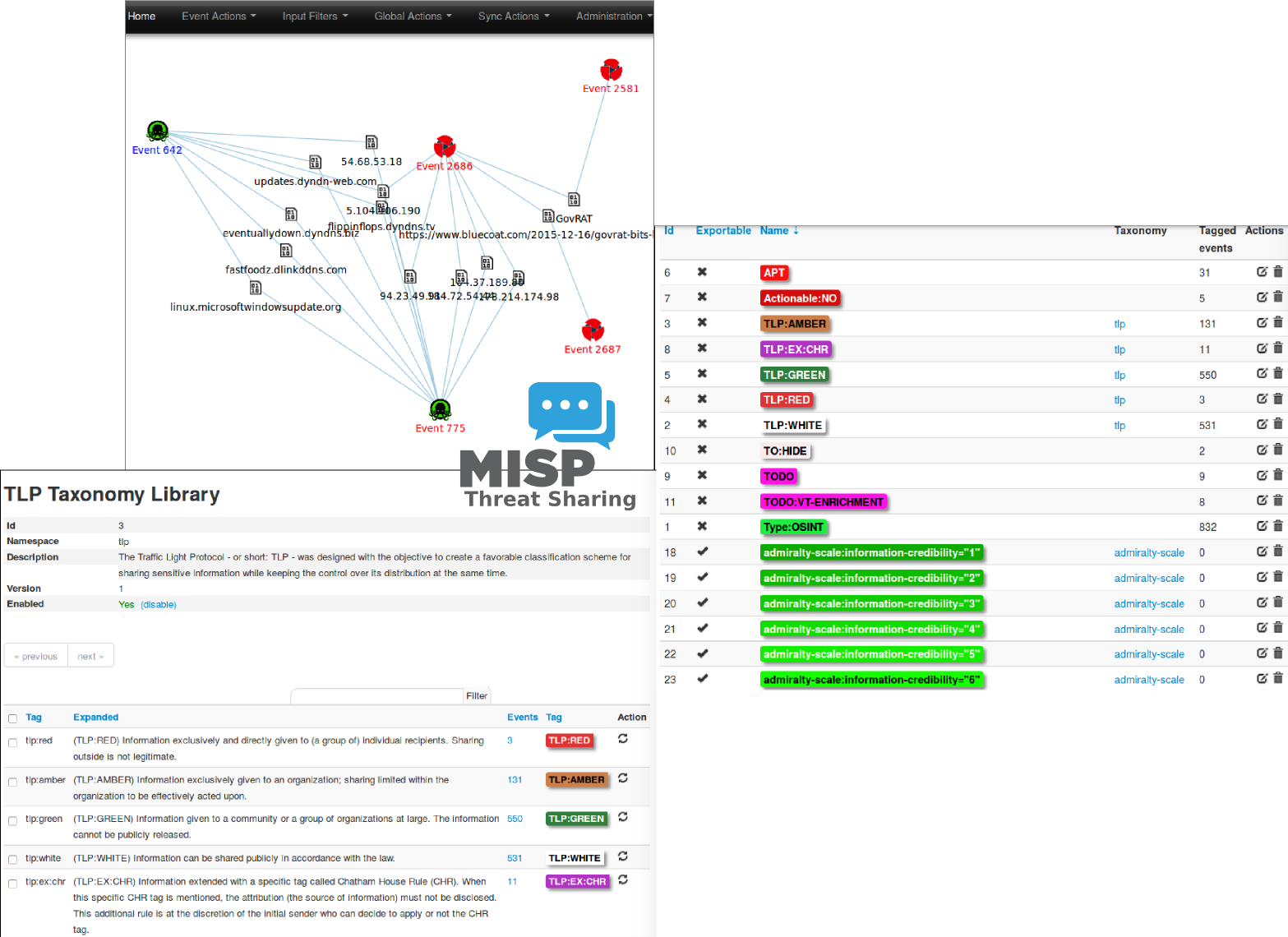
- Automatic correlation finding relationships between attributes and indicators from malware attacks campaigns or analysis.
- A flexible data model where complex objects can be expressed and linked together to express threat intelligence, incidents or connected elements.
- Built-in sharing functionality to ease data sharing using a different model of distributions. MISP can synchronize automatically events and attributes among different MISP. Advanced filtering functionalities can be used to meet each organization sharing policy including a flexible sharing group capacity and an attribute level distribution mechanisms.
- An intuitive user-interface for end-users to create, update and collaborate on events and attributes/indicators. A graphical interface to navigate seamlessly between events and their correlations. Advanced filtering functionalities and warning list to help the analysts to contribute events and attributes.
- storing data in a structured format (allowing the automated use of the database for various purposes) with the extensive support of cybersecurity indicators along fraud indicators as in the financial sector.
- export: generating IDS, OpenIOC, plain text, CSV, MISP XML or JSON output to integrate with other systems (network IDS, host IDS, custom tools), STIX (XML and JSON), NIDS export (Suricata, Snort, and Bro) or RPZ zone. Many other formats easily added via the misp-modules.
- import: bulk-import, batch-import, import from OpenIOC, GFI sandbox, ThreatConnect CSV. Many other formats easily added via the misp-modules.
- Flexible free text import tool to ease the integration of unstructured reports into MISP.
- A gentle system to collaborate on events and attributes allowing MISP users to propose changes or updates to attributes/indicators.
- data-sharing: automatically exchange and synchronization with other parties and trust-groups using MISP.
- delegating of sharing: allows a simple pseudo-anonymous mechanism to delegate publication of event/indicators to another organization.
- Flexible API to integrate MISP with your own solutions. MISP is bundled with PyMISP which is a flexible Python Library to fetch, add or update events attributes, handle malware samples or search for attributes.
- Adjustable taxonomy to classify and tag events following your own classification schemes or existing classification. The taxonomy can be local to your MISP but also shareable among MISP instances.
- Intelligence vocabularies called MISP galaxy and bundled with existing threat actors, malware, RAT, ransomware or MITRE ATT&CK which can be easily linked with events in MISP.
- Expansion modules in Python to expand MISP with your own services or activate already available misp-modules.
- Sighting support to get observations from organizations concerning shared indicators and attributes. Sighting can be contributed via MISP user-interface, API as MISP document or STIX sighting documents.
- STIX support: export data in the STIX format (XML and JSON). Additional STIX import and export is supported by MISP-STIX-Converter or MISP-Taxii-Server.
- Integrated encryption and signing of the notifications via PGP and/or S/MIME depending on the user preferences.
Exchanging info results in faster detection of targeted attacks and improves the detection ratio while reducing the false positives. We also avoid reversing similar malware as we know very fast that other teams or organizations who already analyzed a specific malware.
A sample event encoded in MISP:
Install & Tutorial
- Copyright (C) 2012 Christophe Vandeplas
- Copyright (C) 2012 Belgian Defence
- Copyright (C) 2012 NATO / NCIRC
- Copyright (C) 2013-2018 Andras Iklody
- Copyright (C) 2015-2018 CIRCL – Computer Incident Response Center Luxembourg
- Copyright (C) 2016 Andreas Ziegler