osweep v1.6.3 releases: Don’t Just Search OSINT. Sweep It
OSweep
Description
If you work in IT security, then you most likely use OSINT to help you understand what it is that your SIEM alerted you on and what everyone else in the world understands about it. More than likely you are using more than one OSINT service because most of the time OSINT will only provide you with reports based on the last analysis of the IOC. For some, that’s good enough. They create network and email blocks, create new rules for their IDS/IPS, update the content in the SIEM, create new alerts for monitors in Google Alerts and DomainTools, etc etc. For others, they deploy these same countermeasures based on provided reports from their third-party tools that the company is paying THOUSANDS of dollars for.
The problem with both of these is that the analyst needs to dig a little deeper (ex. FULLY deobfuscate a PowerShell command found in a malicious macro) to gather all of the IOCs. And what if the additional IOC(s) you are basing your analysis on has nothing to do with what is true about that site today? And then you get pwned? And then other questions from management arise…
See where this is headed? You’re about to get a pink slip and walked out of the building so you can start looking for another job in a different line of work.
So why did you get pwned? You know that if you wasted time gathering all the IOCs for that one alert manually, it would have taken you half of your shift to complete and you would’ve got pwned regardless.
The fix? OSweep™.
Changelog v1.6.3
- Remove everything Cymon.io.
- Temporarily pull raw data from Pastebin as psbdmp archive alternative.
- Return ‘no data’ for failed scans in urlscan.io.
- Fix URLhaus hash search functionality.
- Remove phishing_catcher_external.yaml.
- Add time constraint to Phishing Kit Tracker dashboard.
- Add ‘phishingkittracker git’ to pull down all the lookup tables.
Usage
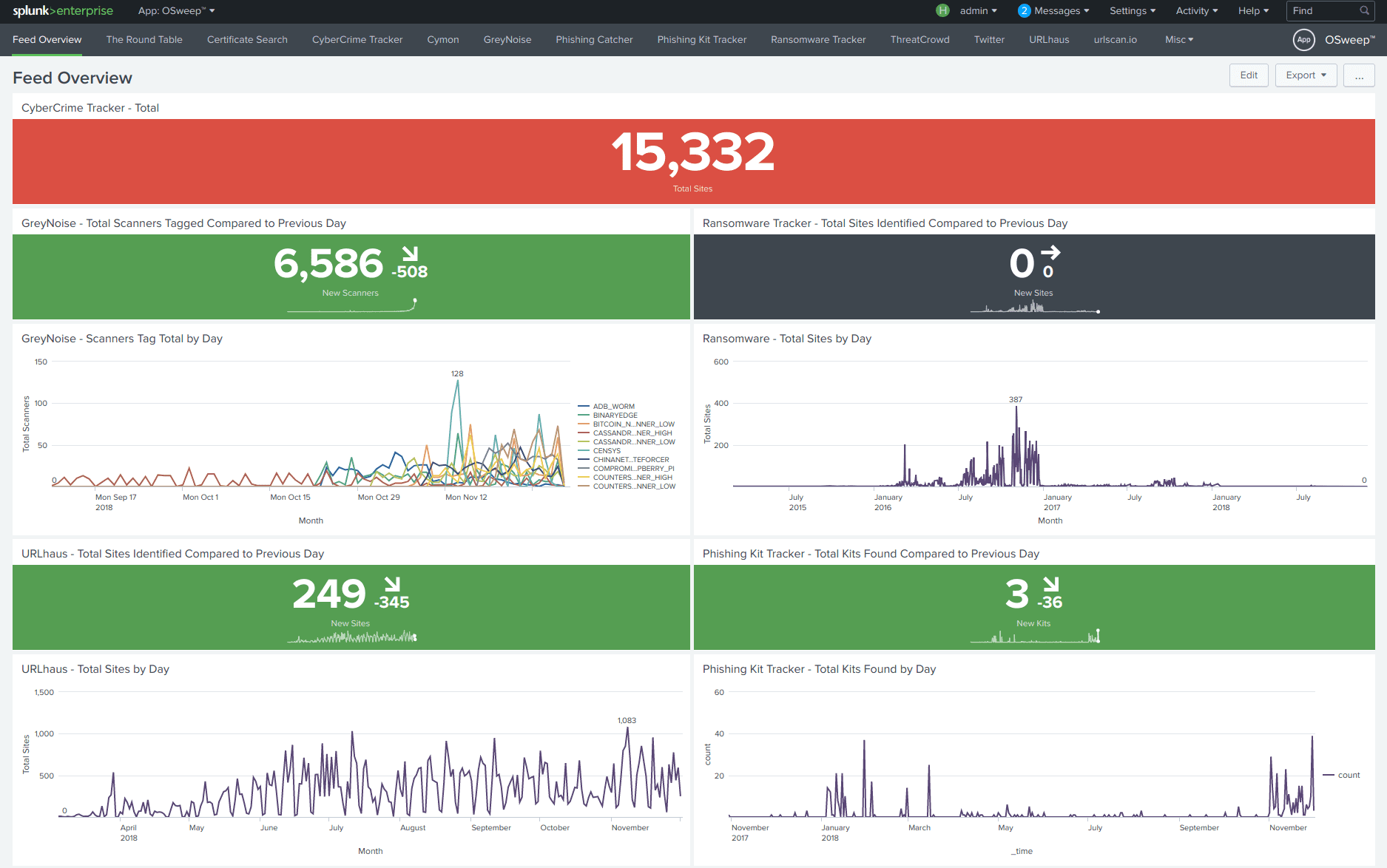
Feed Overview – Dashboard
Three of the dashboards below use lookup tables to store the data feed from the sources. This dashboard shows the current stats compared to the previous day.
Certificate Search – Dashboard
- Switch to the Certificate Search dashboard in the OSweep™ app.
- Add the list of IOCs to the “Domain, IP (+)” textbox.
- Select “Yes” or “No” from the “Wildcard” dropdown to search for subdomains.
- Click “Submit”.
CyberCrime Tracker – Dashboard
- Switch to the CyberCrime Tracker dashboard in the OSweep™ app.
- Add the list of IOCs to the ‘Domain, IP (+)’ textbox.
- Select whether the results will be grouped and how from the dropdowns.
- Click ‘Submit’.
CyberCrime Tracker – Dashboard
- Switch to the CyberCrime Tracker dashboard in the OSweep™ app.
- Add the list of IOCs to the ‘Domain, IP (+)’ textbox.
- Select whether the results will be grouped and how from the dropdowns.
- Click ‘Submit’.
Install && Tutorial
Copyright (c) 2018 leunammejii






