Phantom Evasion v3.0 releases: Python AV evasion tool capable to generate FUD executable

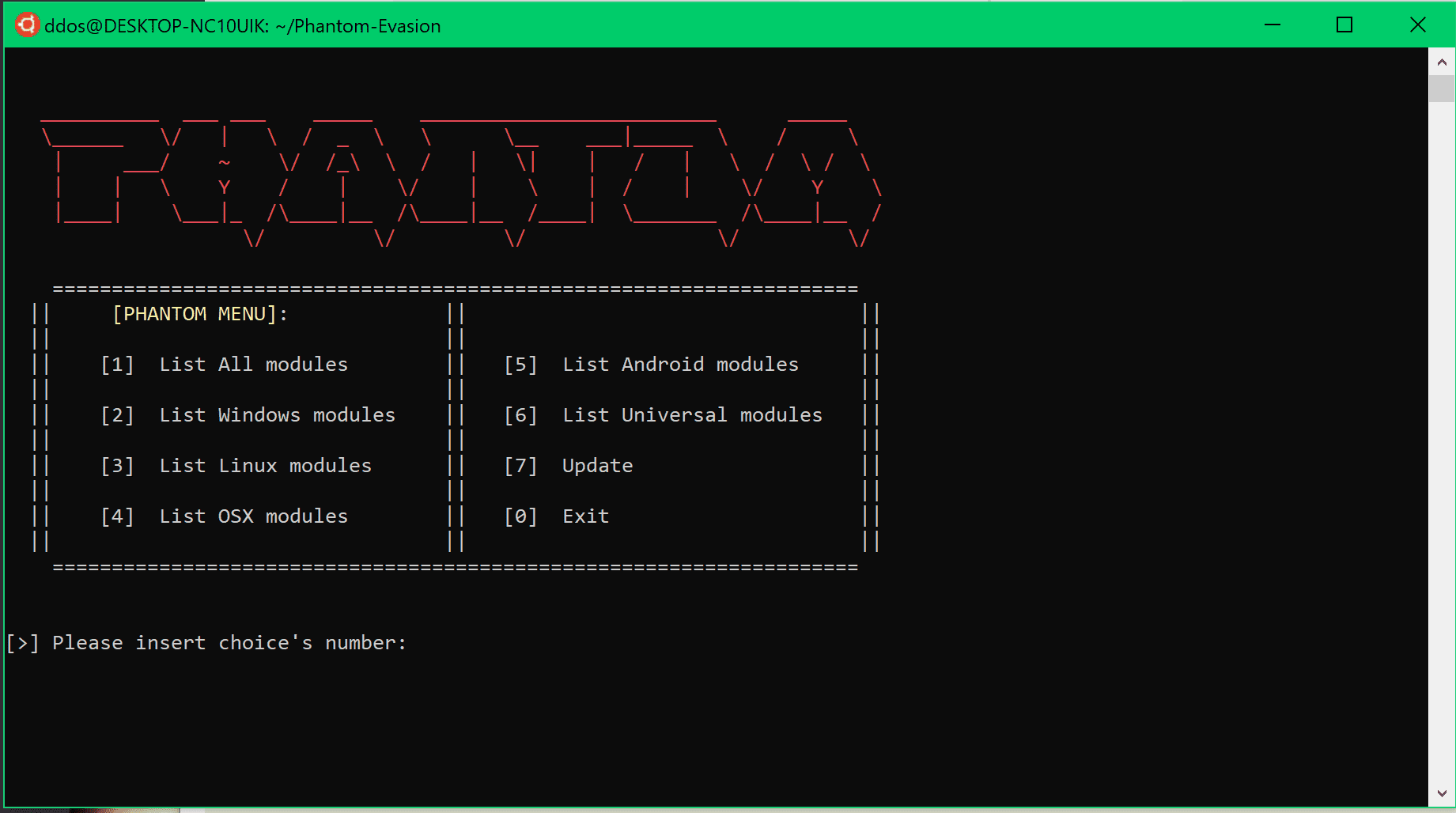
Phantom-Evasion is an interactive antivirus evasion tool written in python capable to generate (almost) FUD executable even with the most common 32-bit msfvenom payload (best performances are obtained with 64-bit payload). The aim of this tool is to make antivirus evasion an easy task for pentesters through the use of prewritten modules focused on polymorphic code and antivirus sandbox detection techniques. Since version 1.0 Phantom-Evasion also include a post-exploitation section dedicated to persistence and auxiliary modules.
Install
git clone https://github.com/oddcod3/Phantom-Evasion.git
Windows Shellcode Injection Modules (C)
Msfvenom windows payloads and custom shellcodes supported
(>) Randomized junkcode and windows antivirus evasion techniques (>) Multibyte Xor encoders availables (see Multibyte Xor encoders readme section) (>) Decoy Processes Spawner available (see Decoy Process Spawner section) (>) Strip executable available (https://en.wikipedia.org/wiki/Strip_(Unix)) (>) Execution time range:35-60 second
- Windows Shellcode Injection VirtualAlloc: Inject and Execute shellcode in memory using VirtualAlloc,CreateThread,WaitForSingleObject API.
- Windows Shellcode Injection VirtualAlloc NoDirectCall LL/GPA: Inject and Execute shellcode in memory using VirtualAlloc,CreateThread,WaitForSingleObject API. VirtualAlloc is dinamically loaded (No Direct Call) using LoadLibrary and GetProcAddress API.
- Windows Shellcode Injection VirtualAlloc NoDirectCall GPA/GMH: Inject and Execute shellcode in memory using VirtualAlloc,CreateThread,WaitForSingleObject API. VirtualAlloc is dinamically loaded (No Direct Call) using GetModuleHandle and GetProcAddress API.
- Windows Shellcode Injection HeapAlloc: Inject and Execute shellcode in memory using VirtualAlloc,CreateThread,WaitForSingleObject API.
- Windows Shellcode Injection HeapAlloc NoDirectCall LL/GPA: Inject and Execute shellcode in memory using HeapCreate,HeapAlloc,CreateThread,WaitForSingleObject API. HeapCreate and HeapAlloc are dinamically loaded (No Direct Call) using LoadLibrary and GetProcAddress API.
- Windows Shellcode Injection HeapAlloc NoDirectCall GPA/GMH: Inject and Execute shellcode in memory using HeapCreate,HeapAlloc,CreateThread,WaitForSingleObject API. HeapCreate and HeapAlloc are dinamically loaded (No Direct Call) using GetModuleHandle and GetProcAddress API.
Windows Pure C meterpreter stager
Pure C polymorphic meterpreter stagers compatible with msfconsole and cobalt strike beacon.(reverse_tcp/reverse_http)
(>) Randomized junkcode and windows antivirus evasion techniques (>) Phantom evasion decoy process spawner available (see phantom evasion decoy process spawner section) (>) Strip executable available (https://en.wikipedia.org/wiki/Strip_(Unix)) (>) Execution time range:35-60 second
- Windows Pure C meterpreter/reverse_tcp Stager: 32 bit windows/meterpreter/reverse_tcp polymorphic stager (require multi/handler listener with payload set to windows/meterpreter/reverse_tcp) First established meterpreter sessions will be invalid wait till a second sessions will be created (with stdapi loaded),
- Windows Pure C meterpreter/reverse_http Stager: 32 bit windows/meterpreter/reverse_http polymorphic stager (require multi/handler listener with payload set to windows/meterpreter/reverse_http)
- Windows Pure C meterpreter/reverse_tcp Stager: 64 bit windows/meterpreter/reverse_tcp polymorphic stager (require multi/handler listener with payload set to windows/x64/meterpreter/reverse_tcp) First established meterpreter sessions will be invalid wait till a second sessions will be created (with stdapi loaded),
- Windows Pure C meterpreter/reverse_http Stager: 64 bit windows/meterpreter/reverse_http polymorphic stager (require multi/handler listener with payload set to windows/x64/meterpreter/reverse_http)
Windows Powershell modules
(>) Randomized junkcode and windows antivirus evasion techniques (>) Decoy Process Spawner available (see phantom evasion decoy process spawner section) (>) Strip executable available (https://en.wikipedia.org/wiki/Strip_(Unix)) (>) Execution time range:35-60 second
- Windows Powershell/Cmd Oneliner Dropper: Require user-supplied Powershell/Cmd oneliner payload (example Empire oneliner payload). Generate Windows powershell/Cmd oneliner dropper written in c. Powershell/Cmd oneliner payload is executed using system() function.
- Windows Powershell Script Dropper: Both msfvenom and custom powershell payloads supported. (32 bit powershell payloads are not compatible with 64 bit powershell target and vice versa.) Generate Windows powershell script (.ps1) dropper written in c. Powershell script payload is executed using system() function (powershell -executionpolicy bypass -WindowStyle Hidden -Noexit -File “PathTops1script”).
Windows Wine-Pyinstaller modules
(>) Randomized junkcode and windows antivirus evasion techniques (>) Execution time range:5-25 second (>) Require python and pyinstaller installed in wine.
- Windows WinePyinstaller Python Meterpreter
Pure python meterpreter payload.
- WinePyinstaller Oneline payload dropper
Pure python powershell/cmd oneliner dropper.
Powershell/cmd payload executed using os.system().
More…
Copyright (C) 2017 oddcod3
Source: https://github.com/oddcod3/