php malware finder: Detect potentially malicious PHP files
PHP malware finder does it is very best to detect obfuscated/dodgy code as well as files using PHP functions often used in malware/webshells.
The following list of encoders/obfuscators/webshells are also detected:
- Best PHP Obfuscator
- Carbylamine
- Cipher Design
- Cyklodev
- Joes Web Tools Obfuscator
- P.A.S
- PHP Jiami
- Php Obfuscator Encode
- SpinObf
- Weevely3
- atomiku
- cobra obfuscator
- phpencode
- tennc
- web-malware-collection
- webtoolsvn
- novahot
Of course, it’s trivial to bypass PMF, but its goal is to catch kiddies and idiots, not people with a working brain. If you report a stupid tailored bypass for PMF, you likely belong to one (or both) category and should re-read the previous statement.
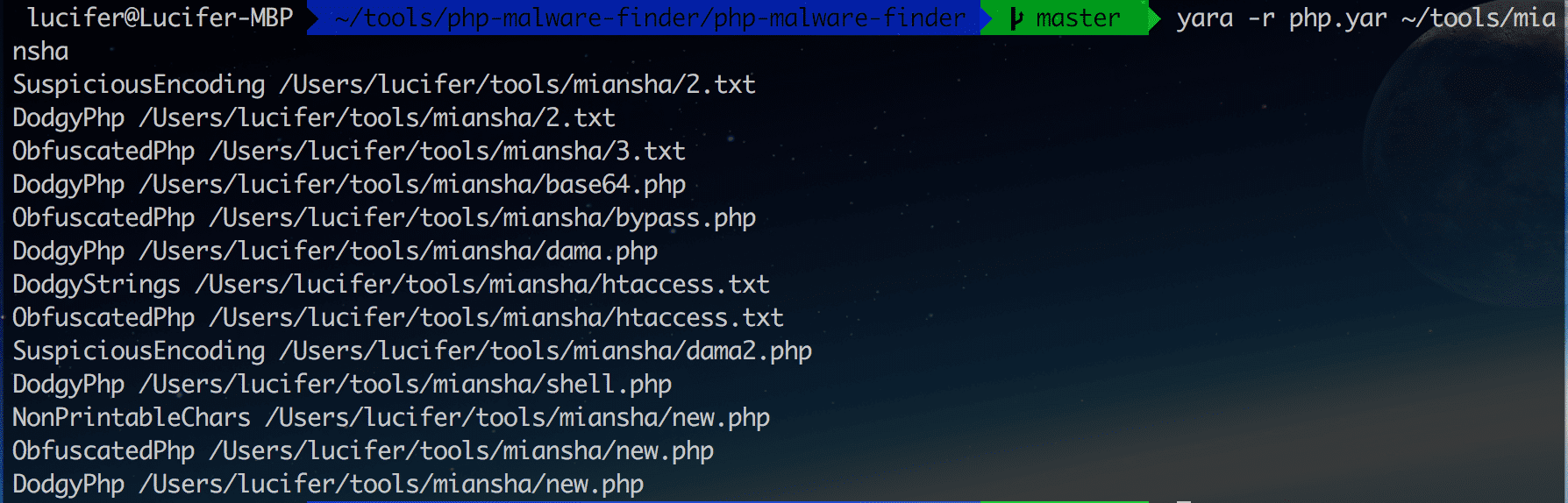
Detection is performed by crawling the filesystem and testing files against a set of YARA rules. Yes, it’s that simple!
Instead of using an hash-based approach, PMF tries as much as possible to use semantic patterns, to detect things like “a $_GET variable is decoded two times, unziped, and then passed to some dangerous function like system“.
Installation
- Install Yara.
This is also possible via some Linux package managers:
Debian: sudo apt-get install yara
Red Hat: yum install yara (requires the EPEL repository) - Download php-malware-finder
git clone https://github.com/nbs-system/php-malware-finder.git
Usage
Or if you prefer to use yara:
Please keep in mind that you should use at least YARA 3.4 because we’re using hashes for the whitelist system, and greedy regexps. Please note that if you plan to build yara from sources, libssl-dev must be installed on your system in order to have support for hashes.
Ho, and by the way, you can run the comprehensive testsuite with make tests.
Whitelisting
Check the whitelist.yar file. If you’re lazy, you can generate whitelists for entire folders with the generate_whitelist.py script.
Why should I use it instead of something else?
Because:
- It doesn’t use a single rule per sample since it only cares about finding malicious patterns, not specific webshells
- It has a complete testsuite, to avoid regressions
- Its whitelist system doesn’t rely on filenames
- It doesn’t rely on (slow) entropy computation
- It uses a ghetto-style static analysis, instead of relying on file hashes
- Thanks to the aforementioned pseudo-static analysis, it works (especially) well on obfuscated files
Source: https://github.com/nbs-system/






