SMB Session Spoofing
This is a utility that can be compiled with Visual Studio 2019 (or newer). The goal of this program is to create a fake SMB Session. The primary purpose of this is to serve as a method to lure attackers into accessing a honey-device. This program comes with no warranty or guarantees.
What an Attacker Sees
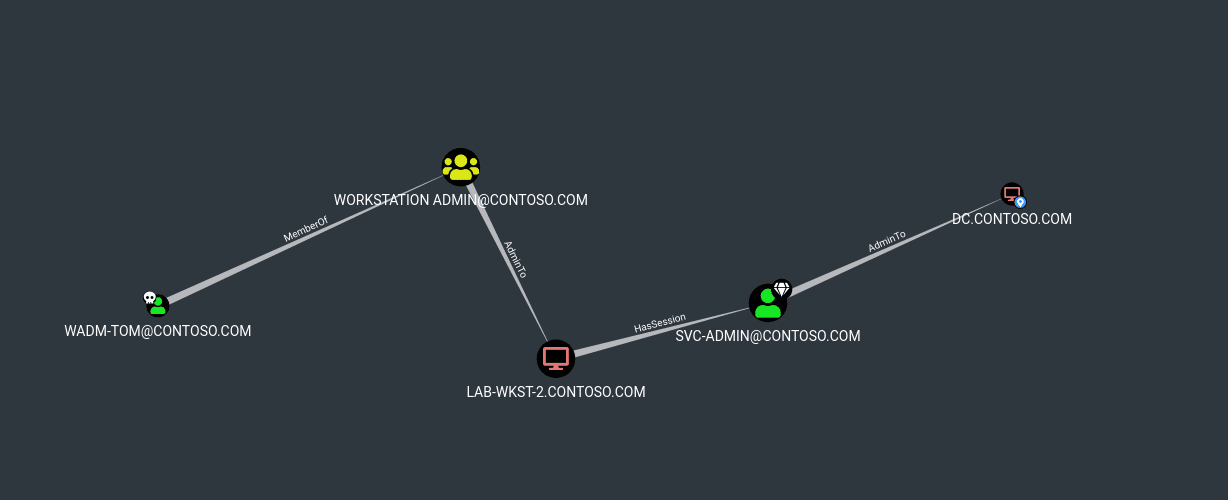
The theory behind this is when an adversary runs SharpHound and collects sessions and analyzes attack paths from owned principals, they can identify that a high privileged user is signed in on Tier-2 infrastructure (Workstations), which (it appears) they can then access and dump credentials on to gain Domain Admin access.
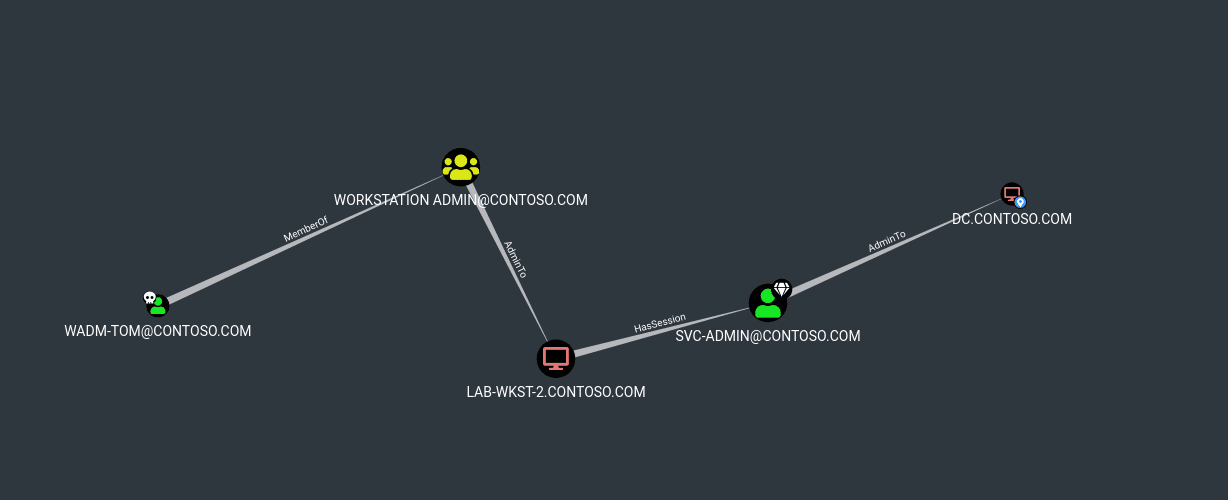
In the scenario above, an attacker has compromised the user “wadm-tom@contoso.com” who is a Local Administrator on lab-wkst-2.contoso.com. The user svc-admin is logged in on lab-wkst-2.contoso.com, meaning that all the attacker has to do is sign into the Workstation, run Mimikatz, and dump credentials. So, how do you monitor for this?
How you Should Configure Monitoring
Implementation of this tool is important, and so is monitoring. If you implement the tool with no monitoring, it is effectively useless; therefore monitoring is a must. The most effective way to monitor this host is to alert on any logon. This program is best utilized on a host with no user activity that is joined to the domain with standard corporate monitoring tools (EDR, AV, Windows Event Log Forwarding, etc). It is highly recommended that you have an email alert, SMS alert, and many others if possible to ensure that incidents involving this machine are triaged as quickly as possible since this has the highest probability for a real adversary to engage with the workstation in question.