The most popular Penetration Testing Tools

Like anything has two sides, hackers can both malicious attacks damage, the same can also use their own technology to find the system vulnerabilities, defects, etc., and then notify the relevant enterprises to repair has been better protection. But for whatever purpose, for hackers, the use of tools and scripts is essential. The so-called good work, we must first of its profits, this article will be introduced for everyone to introduce very popular hacking tools for everyone to choose to use.
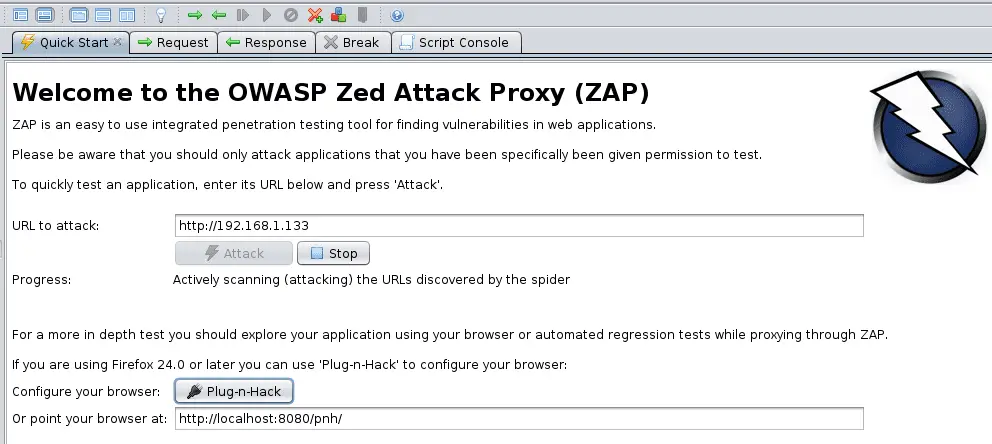
ANGRY IP SCANNER
Hackers can use the user’s IP address to track and spy on their data. It is also called “IPScan “, that is, through the IP address and port scan to find the user system into the method. It is open-source cross-platform software, is currently one of the most effective hacking tools, network management, system engineers favorite.
KALI LINUX
“latest-kali-linux-ethical-hacking-os-release-adds-spectre-meltdown-mitigations”by laboratoriolinux is licensed under CC BY-NC-SA 2.0
Its pre-installed a lot of penetration testing software, and in terms of hardware has also been greatly improved to support a large number of the desktop environment. Kali Linux is a security-oriented concept of the operating system, you can run CD and USB drivers anywhere. By using its pre-installed security tools, you can crack Wi-Fi, fake networks, and test vulnerabilities.
CAIN & ABEL
Cain & Abel is a free password recovery and network sniffing test tool developed by Oxid.it for the Microsoft operating system. It is very powerful, you can sniff the network, network cheating, crack encryption password, decode the password to be disrupted, display the password box, display the cache password and analysis of routing protocols, and even listen to the network of others use VOIP to make calls.
Burp Suite
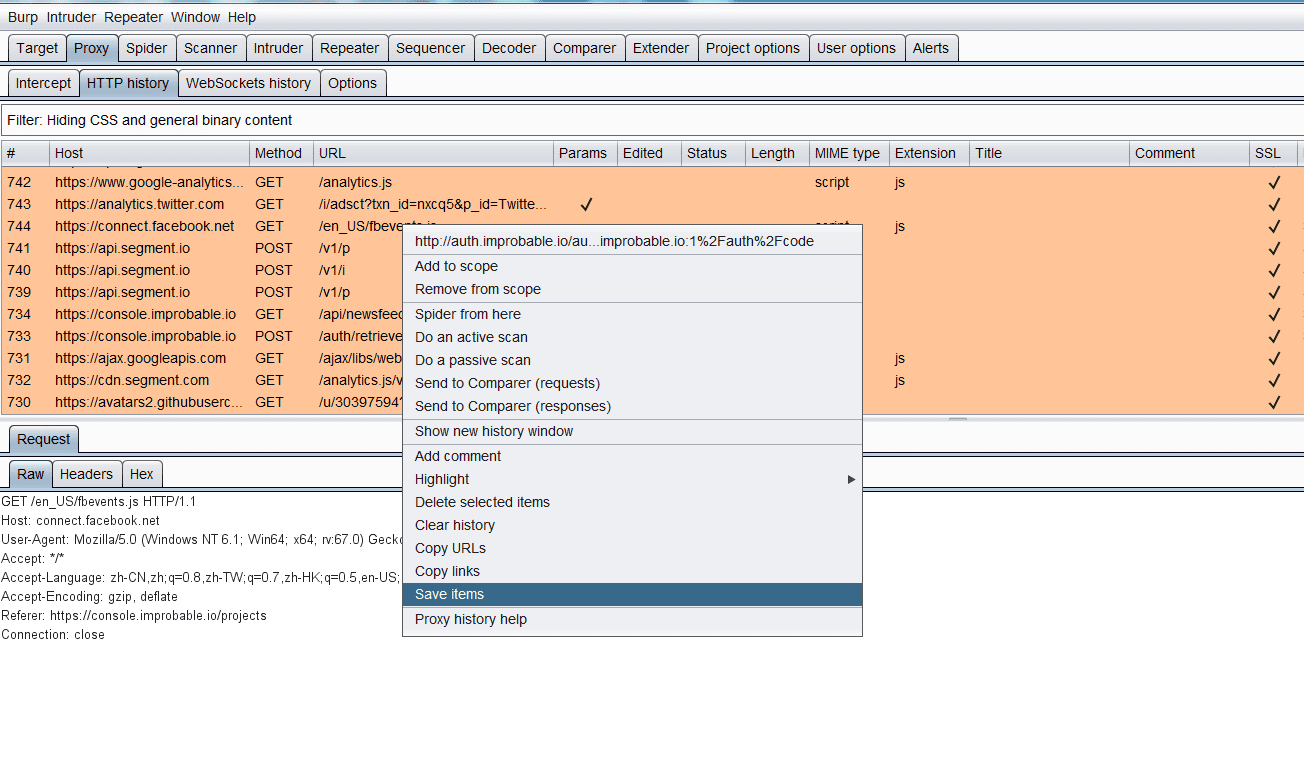
Burp Suite is an integrated platform for attacking web applications. It contains a number of tools and designs a number of interfaces for these tools to facilitate the process of accelerating attacking applications. All the tools share a powerful, extensible framework that can handle and display HTTP messages, persistence, authentication, proxy, log, and alerts. Spider is one of the most important components, able to perceive the application of the web crawler, you can completely enumerate the contents and functions of the application.
ETTERCAP
Ettercap is a powerful trickery tool for Linux, and of course, Windows can be used. Through which you can create and send fake packages at fly speed and send packets from the network adapter to the application software at all levels. Bind the listening data to a local port: connect to a port from a client and be able to decode the data for unknowns or insert the data (only in arp-based mode). This is a very popular tool, as long as its a successful operation, hackers can target the use of a variety of different attacks.

JOHN THE RIPPER
John the Ripper is a free open source and can quickly pass the password crack tool for the case of known ciphertext in the case of trying to crack the clear crack password software to support most of the current encryption algorithms such as DES, MD4, MD5, etc. It supports a variety of different types of system architecture, including Unix, Linux, Windows, DOS mode, BeOS, and OpenVMS, the main purpose is to crack the strong Unix / Linux system password. This tool is like its name, more direct and advocating brute force, the crack process depends entirely on the user, that is, just give it time, he always gives you a good result.
METASPLOIT
Metasploit is an open-source security vulnerability detection tool that helps hackers identify security issues, validate vulnerabilities, and evaluate management-driven security to provide true security risk information. These features include intelligent development, password auditing, Web application scanning, and social engineering. Teamwork, in Metasploit and the synthesis report, presented their findings.

Nmap
nmap is certainly THE scanner to know. Thanks to its numerous parameters, it is a swiss army knife to all situations where network identification is needed. It enables among other things to list network hosts and scan their ports.
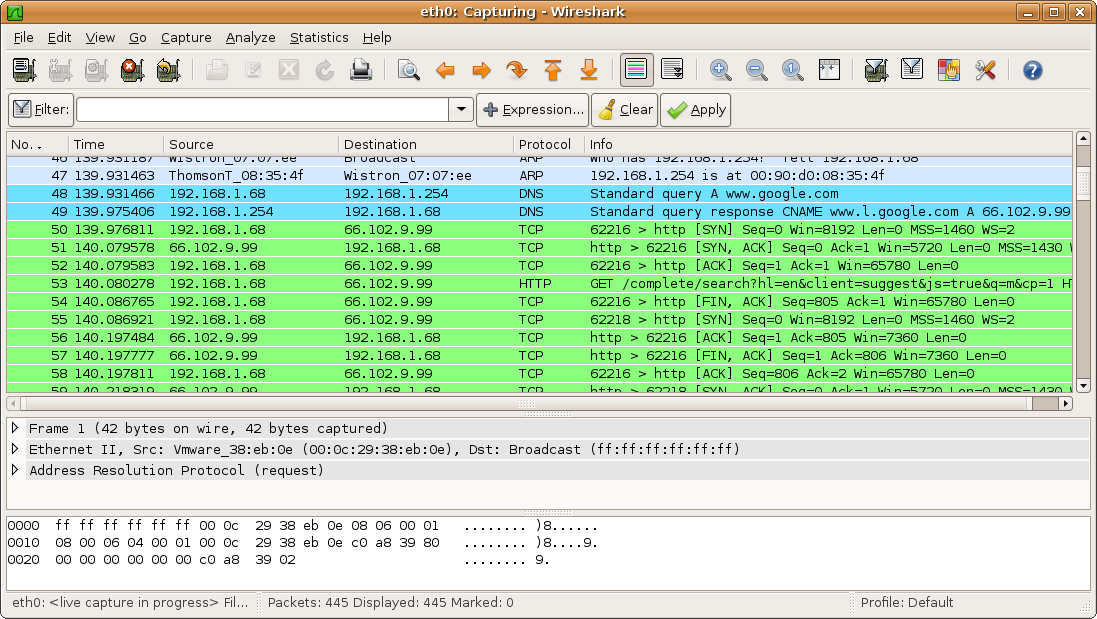
Wireshark
Interactively dump and analyze network traffic. Wireshark is a GUI network protocol analyzer. It lets you interactively browse packet data from a live network or from a previously saved capture file. Wireshark’s native capture file format is libpcap format, which is also the format used by tcpdump and various other tools.
Aircrack-ng
Aircrack-ng is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. aircrack-ng is an 802.11 WEP and WPA/WPA2-PSK key cracking program. It can recover the WEP key once enough encrypted packets have been captured with airodump-ng. This part of the aircrack-ng suite determines the WEP key using two fundamental methods. The first method is via the PTW approach (Pyshkin, Tews, Weinmann). The main advantage of the PTW approach is that very few data packets are required to crack the WEP key. The second method is the FMS/KoreK method. The FMS/KoreK method incorporates various statistical attacks to discover the WEP key and uses these in combination with brute-forcing. Additionally, the program offers a dictionary method for determining the WEP key. For cracking WPA/WPA2 pre-shared keys, a wordlist (file or stdin) or an airolib-ng has to be used.

Nessus
Nessus is the most trusted vulnerability scanning platform for auditors and security analysts. Users can schedule scans across multiple scanners, use wizards to easily and quickly create policies, schedule scans and send results via email. Nessus supports more technologies than any other vendor, including operating systems, network devices, hypervisors, databases, tablets/phones, web servers and critical infrastructure.
THC-Hydra
THC-Hydra is a very fast (multi-threaded) network logon cracker that supports many different services: afp, cisco, cisco-enable, cvs, firebird, ftp, http-get, http-head, http-proxy, https-get, https-head, httpsform-get, https-form-post, icq, imap, imap-ntlm, ldap2, ldap3, mssql, mysql, ncp, nntp, oracle-listener, pcanywhere, pcnfs, pop3, pop3-ntlm, postgres, rexec, rlogin, rsh, sapr3, sip, smb, smbnt, smtp-auth, smtp-authntlm, snmp, socks5, ssh2, svn, teamspeak, telnet, vmauthd, vnc.

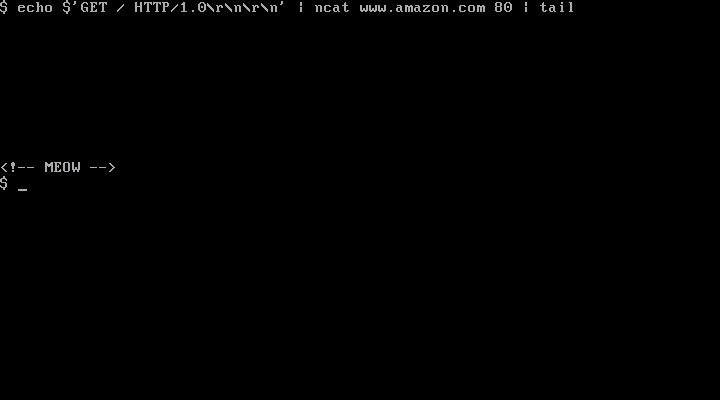
Netcat
Ncat is a feature-packed networking utility that reads and writes data across networks from the command line. Ncat was written for the Nmap Project as a much-improved reimplementation of the venerable Netcat. It uses both TCP and UDP for communication and is designed to be a reliable back-end tool to instantly provide network connectivity to other applications and users. Ncat will not only work with IPv4 and IPv6 but provides the user with a virtually limitless number of potential uses.
sqlmap
sqlmap is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester, and a broad range of switches lasting from database fingerprinting, over data fetching from the database to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
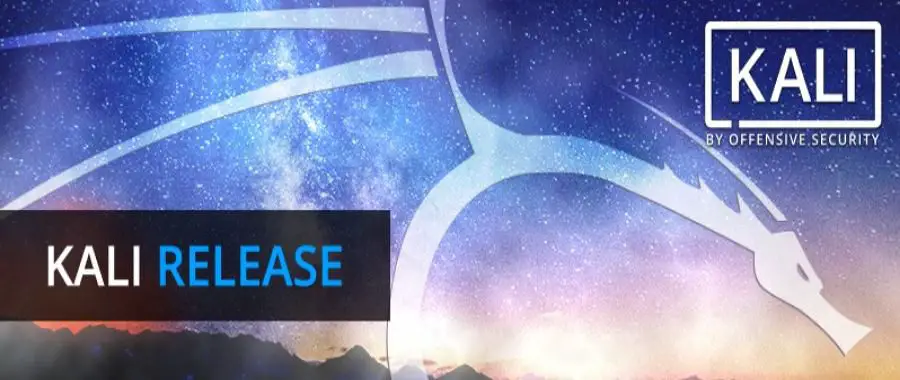
owasp-zap
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds of international volunteers*. It can help you automatically find security vulnerabilities in your web applications while you are developing and testing your applications. It is also a great tool for experienced pentesters to use for manual security testing.