MalSCCM
This tool allows you to abuse local or remote SCCM servers to deploy malicious applications to hosts they manage. To use this tool your current process must have admin rights over the SCCM server.
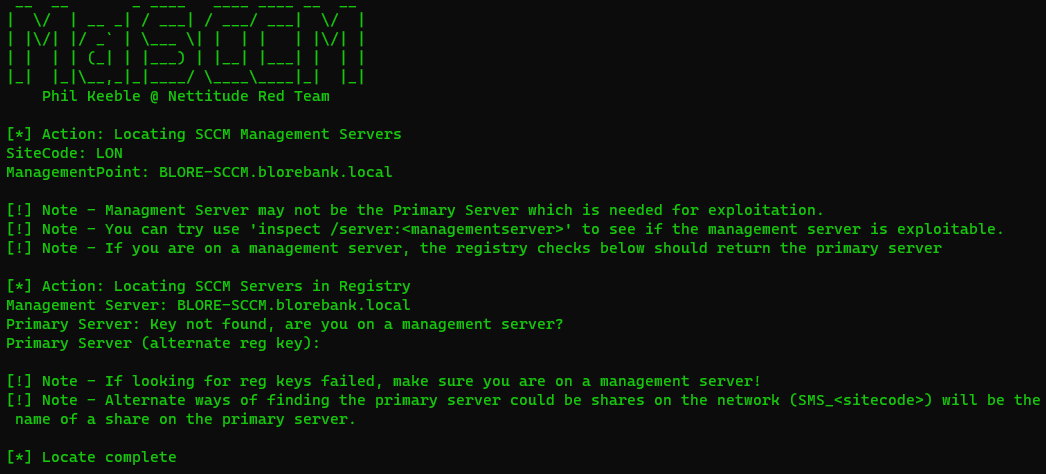
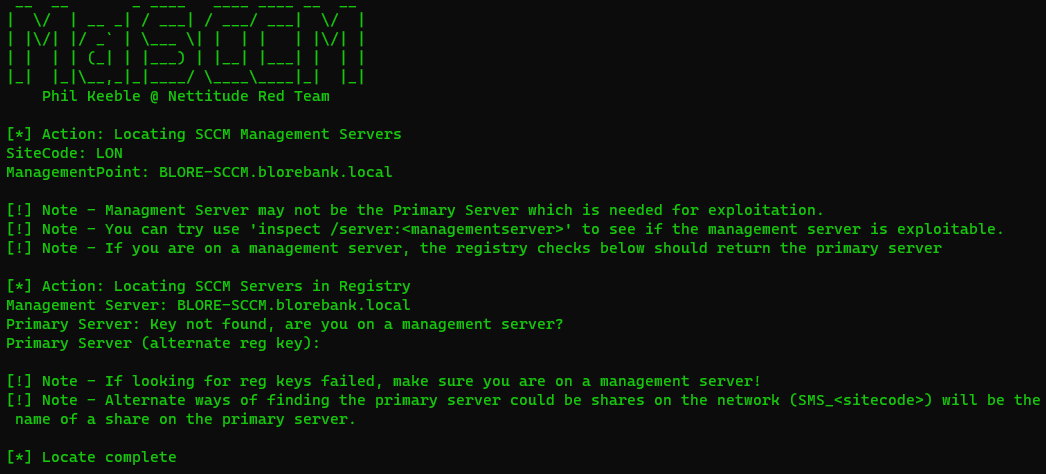
Typically deployments of SCCM will either have the management server and the primary server on the same host, in which case the host returned from the locate command can be used as the primary server.
If that is not the case you will need to compromise the management host returned with locate so that you can then run locate again on that host and get the primary server hostname. Once you have that and admin access you are good to go!
Attack Flow
- Compromise client, use locate to find management server
- Compromise management server, use locate to find primary server
- use Inspect on the primary server to view who you can target
- Create a new device group for the machines you want to laterally move too
- Add your targets into the new group
- Create an application pointing to a malicious EXE on a world-readable share
- Deploy the application to the target group
- Force the target group to checkin for updates
- Profit…
- Cleanup the application and deployment
- Delete the group