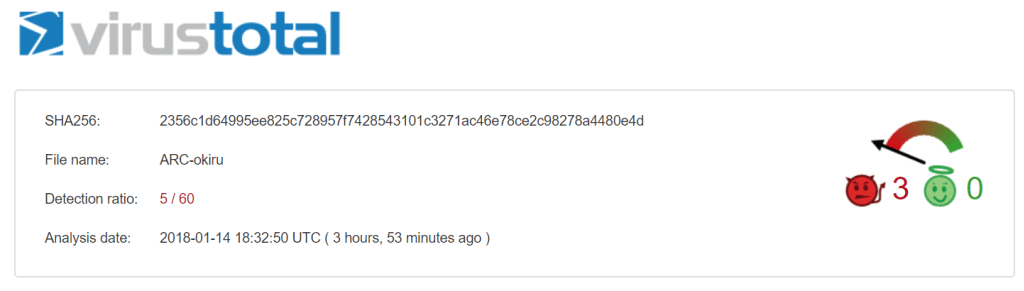
MalwareMustDie team for the first time found a way to infect ARC the CPU Linux ELF malware – Mirai Okiru aims for the system based on the ARC. It is reported that, Mirai Okiru before being found almost no anti-virus engine can be detected, coupled with the current rapidly changing threat landscape Linux things, so the researchers believe that the attacker will use Mirai Okiru targeting based ARC CPU of Things equipment, resulting in devastating effects.
ARC (Argonaut RISC Core) embedded processor is a series of ARC International designed the CPU 32, which is widely used to store, home, mobile, automotive and networking applications SoC devices.
August 2016, a team of researchers MalwareMustDie unixfreaxjp first discovered the botnet Mirai, after less than two years, unixfreaxjp Noting also that the malware community there is a new form of attack –Mirai Okiru, its far-reaching impact, because the ARC embedded processor has been licensed more than 200 organizations, and shipments to reach 1.5 billion a year, which means that the number of devices may be exposed is very large. In addition to attacking ARC, there may be other malicious purposes.
This is the FIRST TIME ever in the history of computer engineering that there is a malware for ARC CPU, & it is #MIRAI OKIRU!!
Pls be noted of this fact, & be ready for the bigger impact on infection Mirai (specially #Okiru) to devices hasn't been infected yet.#MalwareMustDie pic.twitter.com/y8CRwwkenA— Odisseus (@_odisseus) January 14, 2018
For the more in-depth understanding of Mirai Okiru, MalwareDustdie team analyzed the differences between Okiru with Satori variants (another botnet):
- “From what we observe so far. these two types are very different, (among of several common similar characteristics), we think it is good to have different rules to detect Mirai variant Okiru and Satori
- Some simple highlights to differ Okiru to Satori variant:
- The config is different, Okiru variant’s config is encrypted in two parts w/ telnet bombardment password encrypted, Satori does not split it in 2parts and doesn’t encrypt brute default passwords. Also, Okiru’s telnet attack login information is a bit longer (can be up to 114 credentials, max counted), while Satori is having different and shorter database.
- Satori seem to have “TSource Engine Query” common Distributed “Reflective” (DRDoS) attack function via random UDP, while Okiru does not seem to have this function,
- The infection follow up commands written in both Okiru and Satori in their configurations are a bit different, showing possibility that they don’t seem sharing a same “herding environment”,
- (up to) Four types of router attack exploit code has only being spotted hardcoded in Okiru variant, yet Satori does not use these exploits at all,
- Satori (see VT comment part for reversed code) is using small embedded ELF trojan downloaders to download other architecture binaries which were coded differently compared to Okiru ones (see reversed code is in VT comment),
- (there are more minors stuff too that you can notice using the pictures shown in previous points, like differences in usage of watchdog, the usage of command “echo -en \x…” etc)
Researchers from MalwareMustDie published the Yara rules for the threat
https://github.com/unixfreaxjp/rules/blob/master/malware/MALW_Mirai_Okiru_ELF.yar
Source: Security Affairs
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
