PESecurity
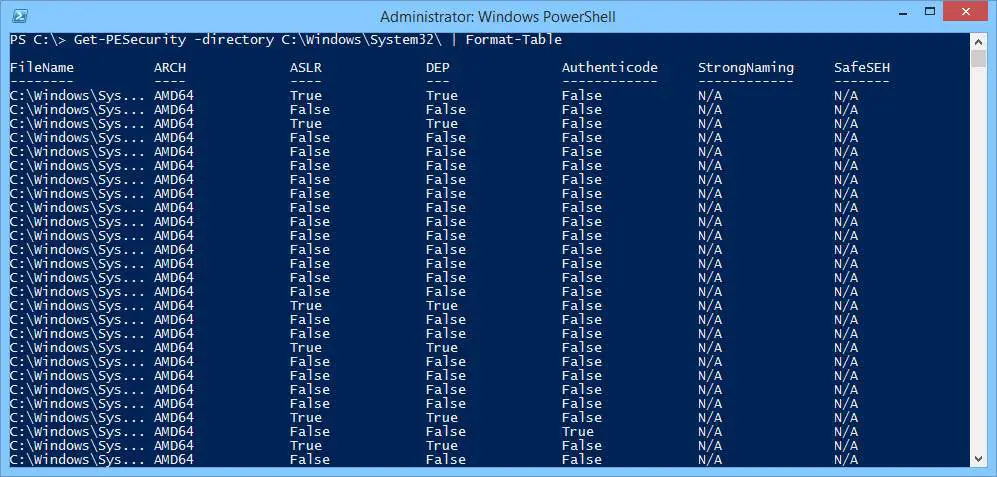
PowerShell script to check if a Windows binary (EXE/DLL) has been compiled with ASLR, DEP, SafeSEH, StrongNaming, Authenticode, Control Flow Guard, and HighEntropyVA.
Download
git clone https://github.com/NetSPI/PESecurity.git
Usage
Import the module
Check a directory for DLLs & EXEs
Check a directory for DLLs & EXEs recrusively
Show results in a table and sort by a column
Copyright (c) 2015 NetSPI
Source: https://github.com/NetSPI/
Continue Reading