Ports scanning using Metasploit
On your penetration testing, finding ports and services is important. In the real world, I exploited some systems by identifying open ports and try to attack this port.
This articles, I am going to guide you how to use some module on Metasploit for finding ports and services on your target system.
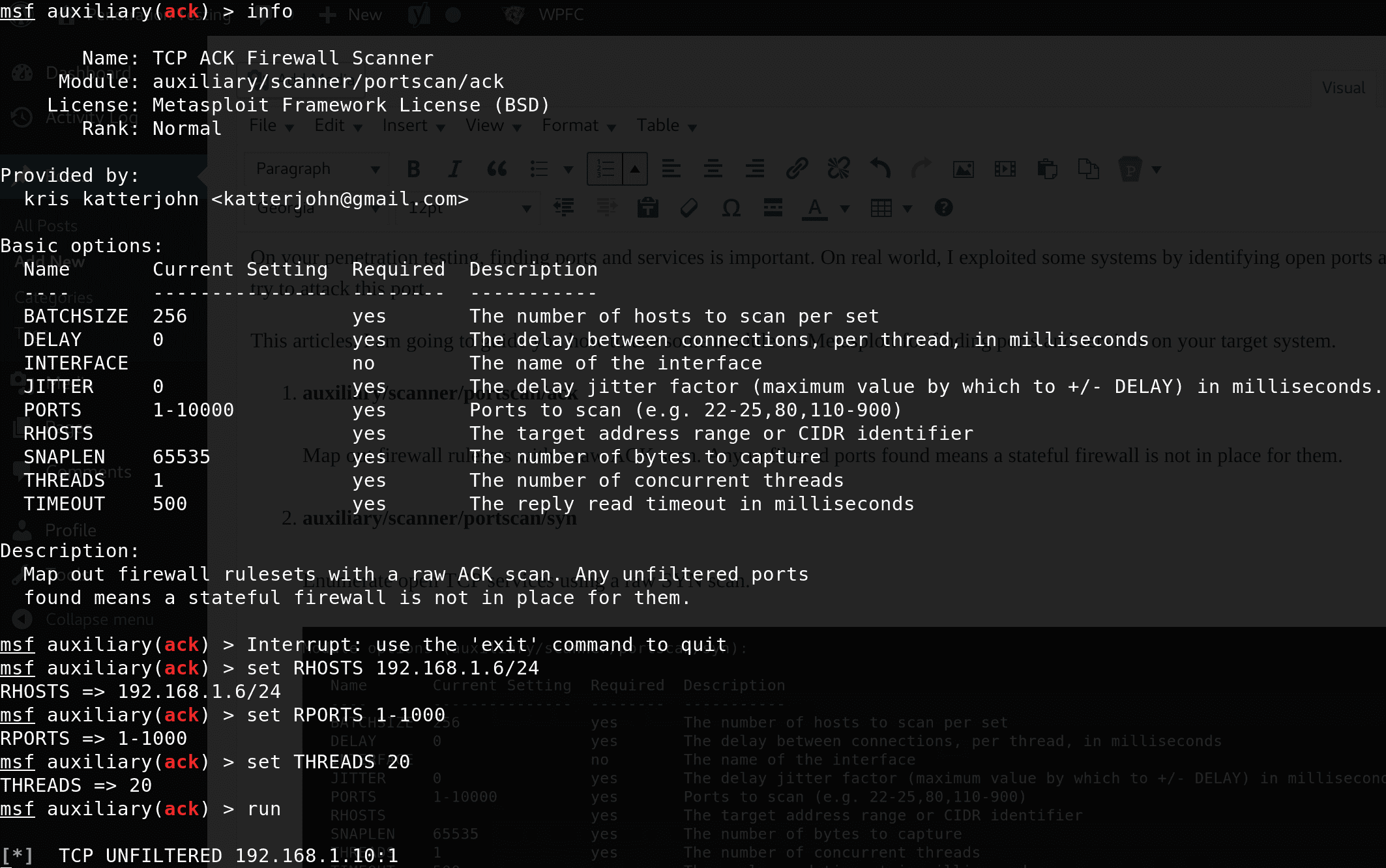
- auxiliary/scanner/portscan/ack Map out firewall rulesets with a raw ACK scan. Any unfiltered ports found means a stateful firewall is not in place for them.
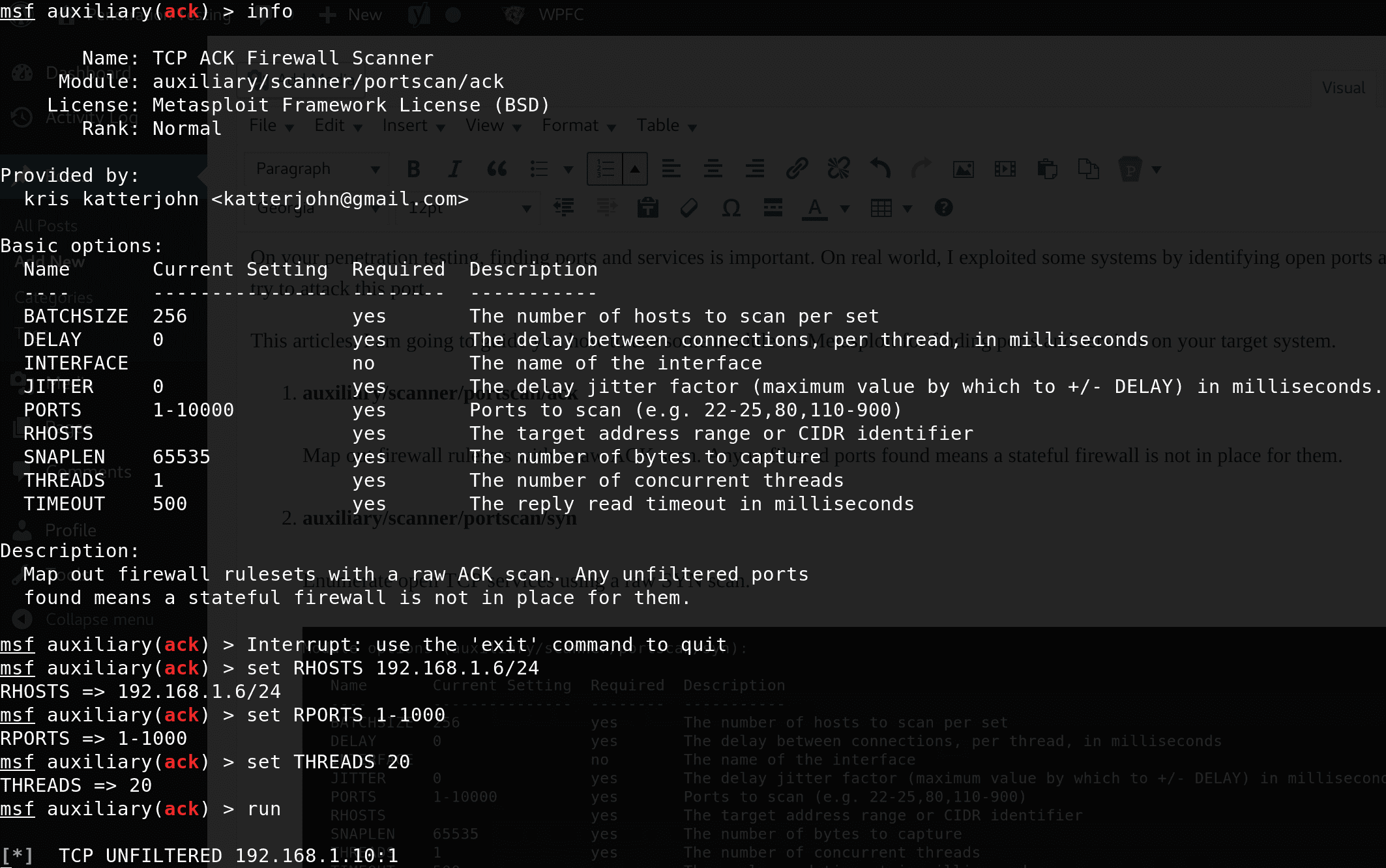
- auxiliary/scanner/portscan/synEnumerate open TCP services using a raw SYN scan.
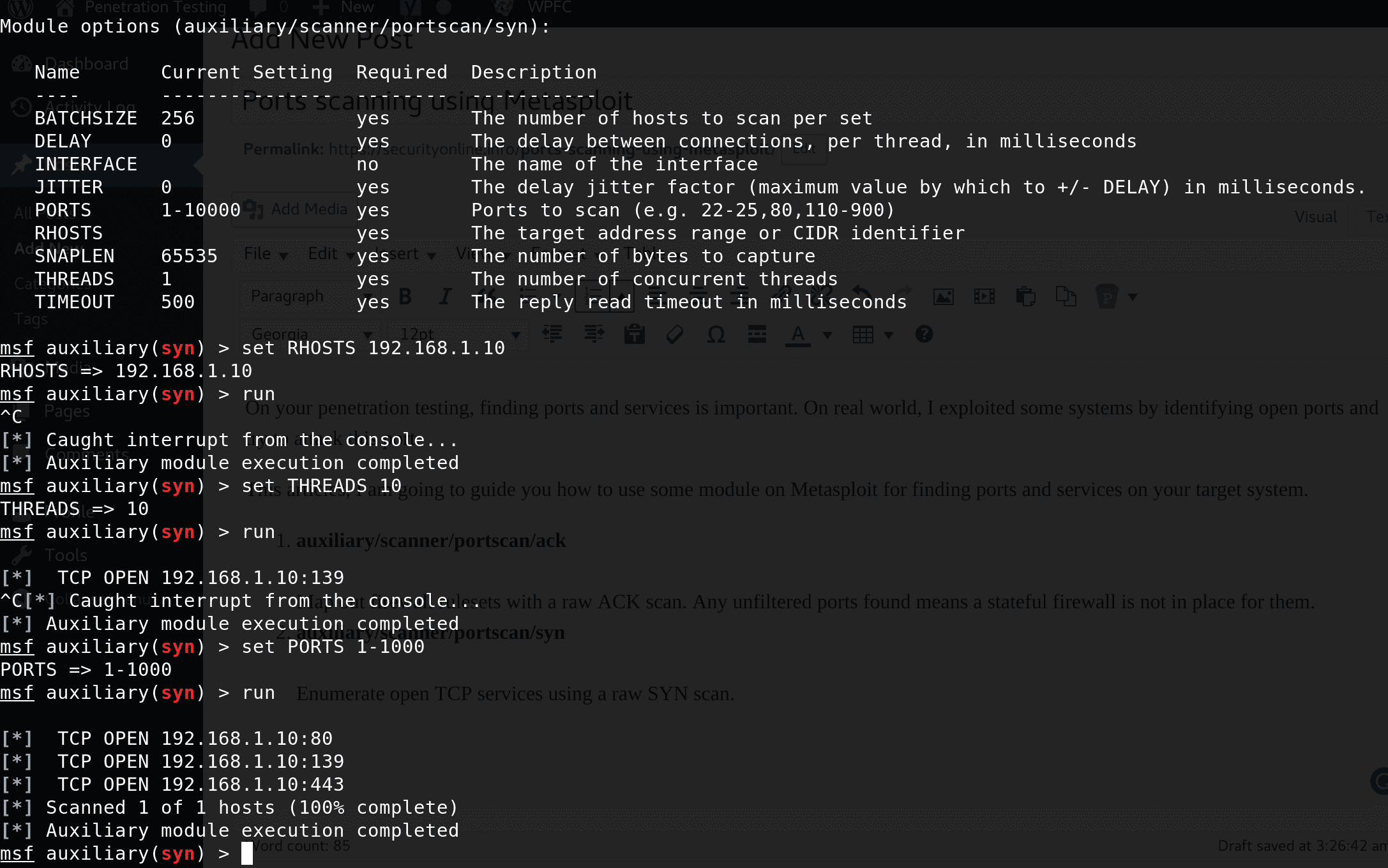
- auxiliary/scanner/portscan/tcpEnumerate open TCP services by performing a full TCP connect on each port. This does not need administrative privileges on the source machine, which may be useful if pivoting.

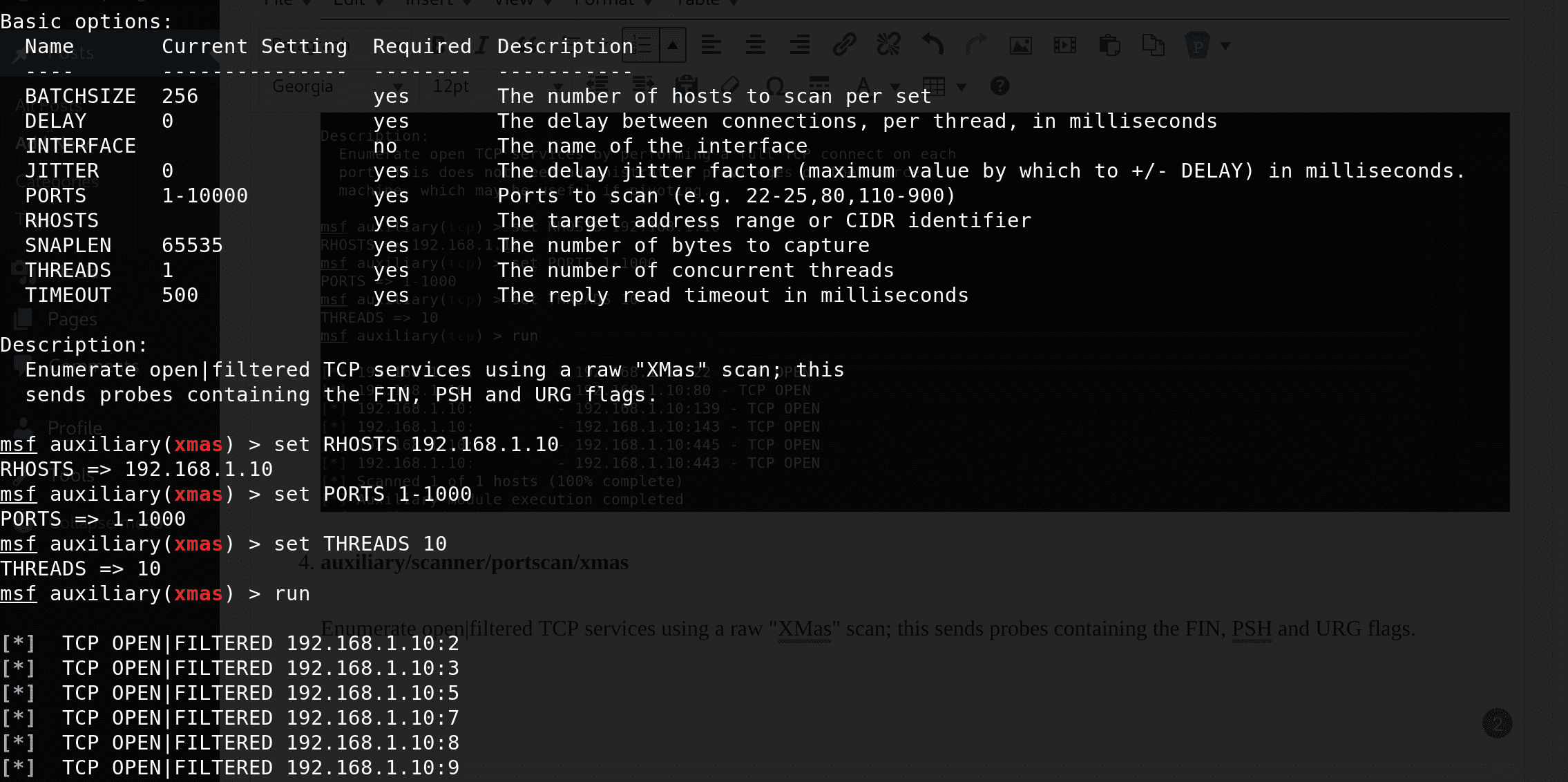
- auxiliary/scanner/portscan/xmasEnumerate open|filtered TCP services using a raw “XMas” scan; this sends probes containing the FIN, PSH and URG flags.
Demo
To use all 4 modules, you can use this script:






