pwndbg 2024.02.14 releases: Exploit Development and Reverse Engineering with GDB
pwndbg (/poʊndbæg/) is a GDB plug-in that makes debugging with GDB suck less, with a focus on features needed by low-level software developers, hardware hackers, reverse-engineers and exploit developers.
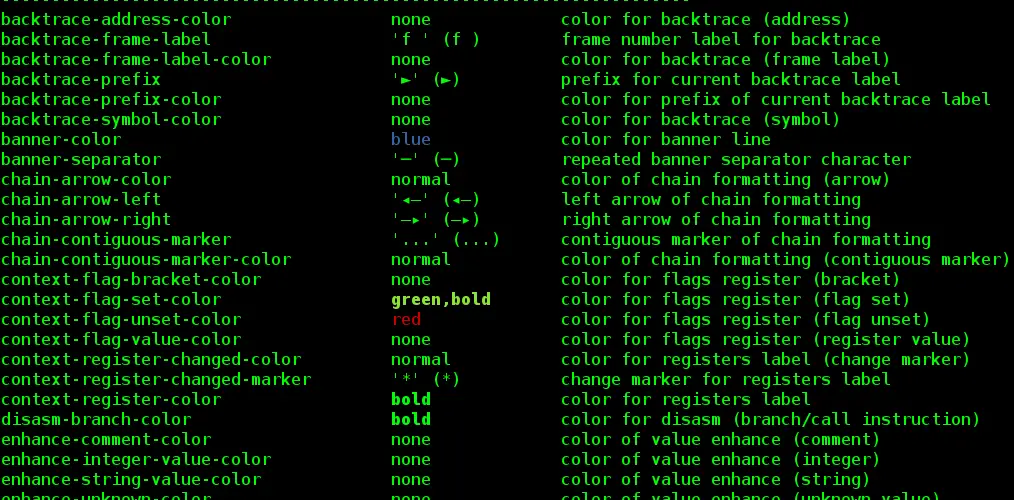
Pwndbg has a lot of useful features. You can a list of all available commands at any time by typing the pwndbgcommand. Here’s a small subset which is easy to capture in screenshots.
Arguments
All function call sites are annotated with the arguments to those functions. This works best with debugging symbols, but also works in the most common case where an imported function (e.g. libc function via GOT or PLT) is used.
Context
A useful summary of the current execution context is printed every time GDB stops (e.g. breakpoint or single-step), displaying all registers, the stack, call frames, disassembly, and additionally recursively dereferencing all pointers. All memory addresses are color-coded to the type of memory they represent.
Disassembly
Pwndbg uses Capstone Engine to display disassembled instructions, but also leverages its introspection into the instruction to extract memory targets and condition codes.
All absolute jumps are folded away, only displaying relevant instructions.
Additionally, if the current instruction is conditional, Pwndbg displays whether or not it is evaluated with a green check or a red X, and folds away instructions as necessary.
Emulation
Pwndbg leverages Unicorn Engine in order to only show instructions which will actually be emulated. At each debugger stop (e.g. breakpoint or single-step) the next few instructions are silently emulated, and only instructions which will actually be executed are displayed.
This is incredibly useful when stepping through jump tables, PLT entries, and even while ROPping!
Heap Inspection
Pwndbg enables introspection of the glibc allocator, ptmalloc2, via a handful of introspection functions.
IDA Pro Integration
Pwndbg flips traditional IDA Pro integration on its head. Rather than sticking code inside of IDA that you need to interact with, by installing a small XMLRPC server inside of IDA, Pwndbg has full access to everything IDA knows.
This allows extraction of comments, decompiled lines of source, breakpoints, and synchronized debugging (single-steps update the cursor in IDA).
More…
Changelog 2024.02.14
General changes:
- Added portable Pwndbg archive to release as well as nix, rpm, deb, arch and alpine packages
- Added
$base(objfile_name)function to compute base address of given memory page, e.g.print $base(libc)+0x123will return base of libc + 0x123 - Context will now display threads information for multi-threaded programs
- this is limited by
context-max-threadsparameter (useset context-max-threads <N>to change)
- this is limited by
- Added glibc heap exploitation support for libc 2.12+ (#1823)
- Added support for FreeBSD (#1832)
- The
gdb-pt-dumpgit submodule was moved to a python dependency (#1929)
New commands:
track-got {enable,disable,info,query} ...can be used to track (#1971)stepuntilasm <asm>will step through program instructions until a matching part of instruction string is found (#1798)break-if-taken <loc>andbreak-if-not-taken <loc>will setup a breakpoint on given location of a branch instruction which will stop the program if the branch was taken or not (#1799)plist ...can be used to print linked lists (#1795, #1817)mmap ...andmprotect ...commands will invoke themmapormprotectsyscalls with given arguments in the debugged program- note: this works by assembling a shellcode for the syscall call, placing the code on current PC/IP address, executing the syscall and reverting back the register and memory changes made
threadcommand to display threads informationhicommand to check if an address belongs to a glibc heap chunk (#1938)tipsto display tips about Pwndbg usagesigreturn <address>to print sigreturn x86-64 frame (#1940)
Changed commands:
- Added
telescope --frameto display stack frame information (requires BP and SP to point to the same memory region) (#1855) - Glibc heap commands now also print real chunk size (#1748)
- Added
spray --only-funcptrs | -xflag to spray only the memory addresses where values point to executable memory pages (#1809) - Added
-A <N>and-B <N>flags tovmmapto display N entries after/before the filtered page (#1810) - The linux kernel memory pages figured out by gdb-pt-dump can now be filtered in
vmmap(they have unique names) (#1837) - Added new arguments/options to the
searchmemory command (#1867) telescopeoutput can now show frame pointer offsets (#1925)distance <single-address>now prints offset from memory page start address (#1926)- Added
stack -i | --inverseto show stack in reverse order (#1978) - Added new positional argument to
cycliccommand to save its output to file (so it can later be used, e.g. asrun < input) (#2009)
- More…
Installation
Copyright (c) 2023 Dominik ‘Disconnect3d’ Czarnota













