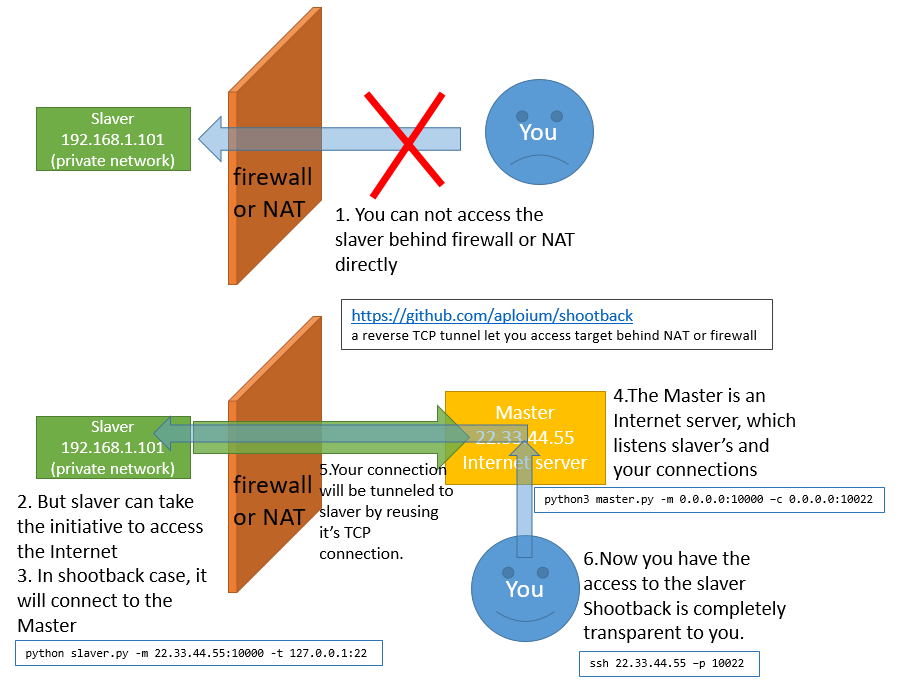
shootback: a reverse TCP tunnel let you access target behind NAT or firewall

shootback
is a reverse TCP tunnel let you access target behind NAT or firewall. Consumes less than 1% CPU and 8MB memory under 800 concurrency. slaver is single file and only depends on python(2.7/3.4+) standard library.
How it works
Typical Scene
- Access company/school computer(no internet IP) from home
- Make a private network/site public.
- Help private network penetration.
- Help CTF offline competitions.
- Connect to a device with dynamic IP, such as ADSL
Getting started
- requirement:
- Master: Python3.4+, OS independent
- Slaver: Python2.7/3.4+, OS independent
- no external dependencies, only python std lib
- download
git clone https://github.com/aploium/shootback
- (optional) if you need a single-file slaver.py, run python3 build_singlefile_slaver.py
- run these command
- a more realistic example:
assume your master is 22.33.44.55 (just like the graph above) - for more help, please see python3 master.py –help and python3 slaver.py –help
Tips
- run in daemon:
nohup python(or python3) slaver.py -m host:port -t host:port -q &
or - ANY service using TCP is shootback-able. HTTP/FTP/Proxy/SSH/VNC/…
- shootback itself just do the transmission job, do not handle encrypt or proxy. However, you can use a 3rd party proxy (eg: shadowsocks) as slaver target.
for example:shadowsocks_server<-->shootback_slaver<-->shootback_master<-->shadowsocks_client(socks5)
Source: https://github.com/aploium/





