shuriken: Cross Site Scripting scanner
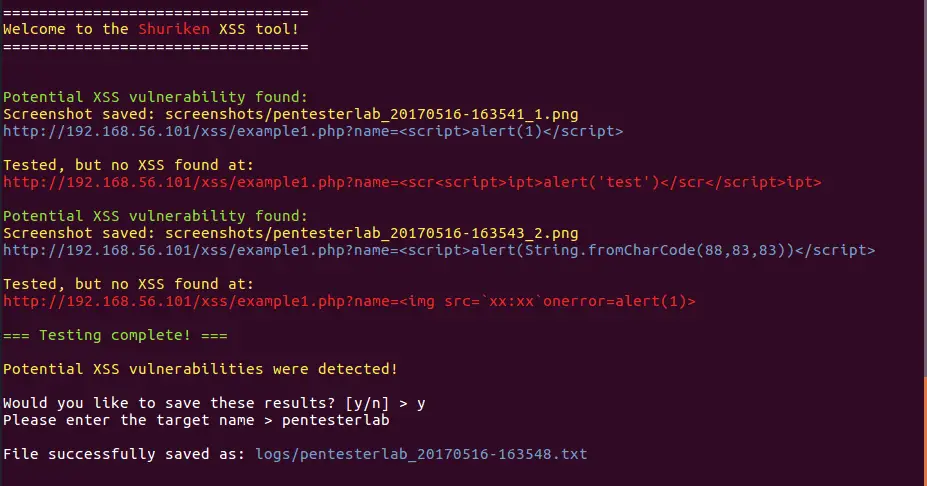
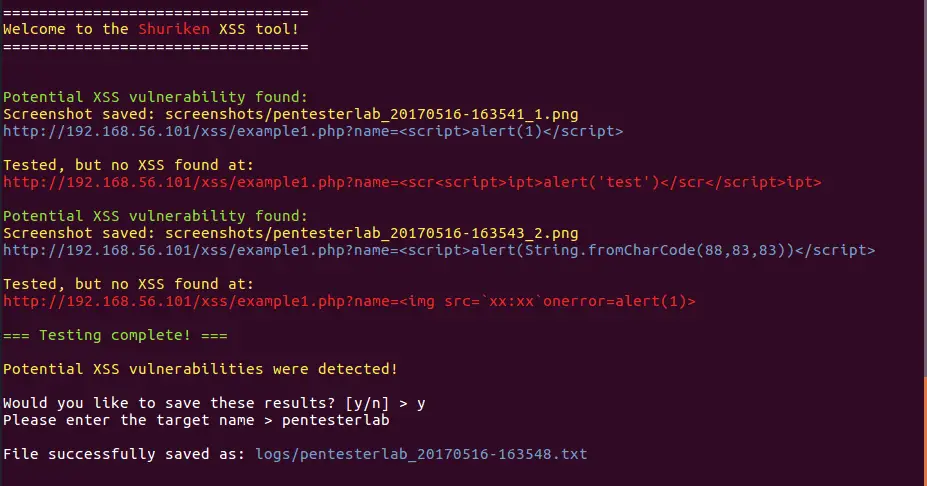
Shuriken was developed by Shogun Lab as an open source Cross-Site Scripting (XSS) command line utility to aid web security researchers who want to test a list of XSS payloads in a web application. It allows a tester to easily change payload lists, log results and take screenshots of successful payloads.
It should only be used on valid targets who have consented to pentesting, please ensure you have permission before using this tool against a web application.
Features
- Easily specify where in a URL the payload should be injected with the “{xss}” string.
- Quickly change payload lists.
- Take screenshots of successful XSS hits.
- Save logs of reflected XSS payloads.
Installation
Usage
To get a list of options and switches, enter:
To test a list of payloads against a target URL, specify where the payloads will go with “{xss}” and enter:
If you would like to screenshot and save all reflected XSS payloads, use the –screen flag with a name for the screenshot images and enter:
You must specify a payload and URL if you don’t then you’ll get an error. For an example payload to test with, check out this list of common XSS payloads.
Copyright (c) 2016 Faizan Ahmad, on original work (XssPy).
Copyright (c) 2017 Steven Patterson [Shogun Lab], on modified work (Shuriken).
Source: https://github.com/shogunlab/






