ADRecon: Active Directory gathering information tool
ADRecon: Active Directory Recon
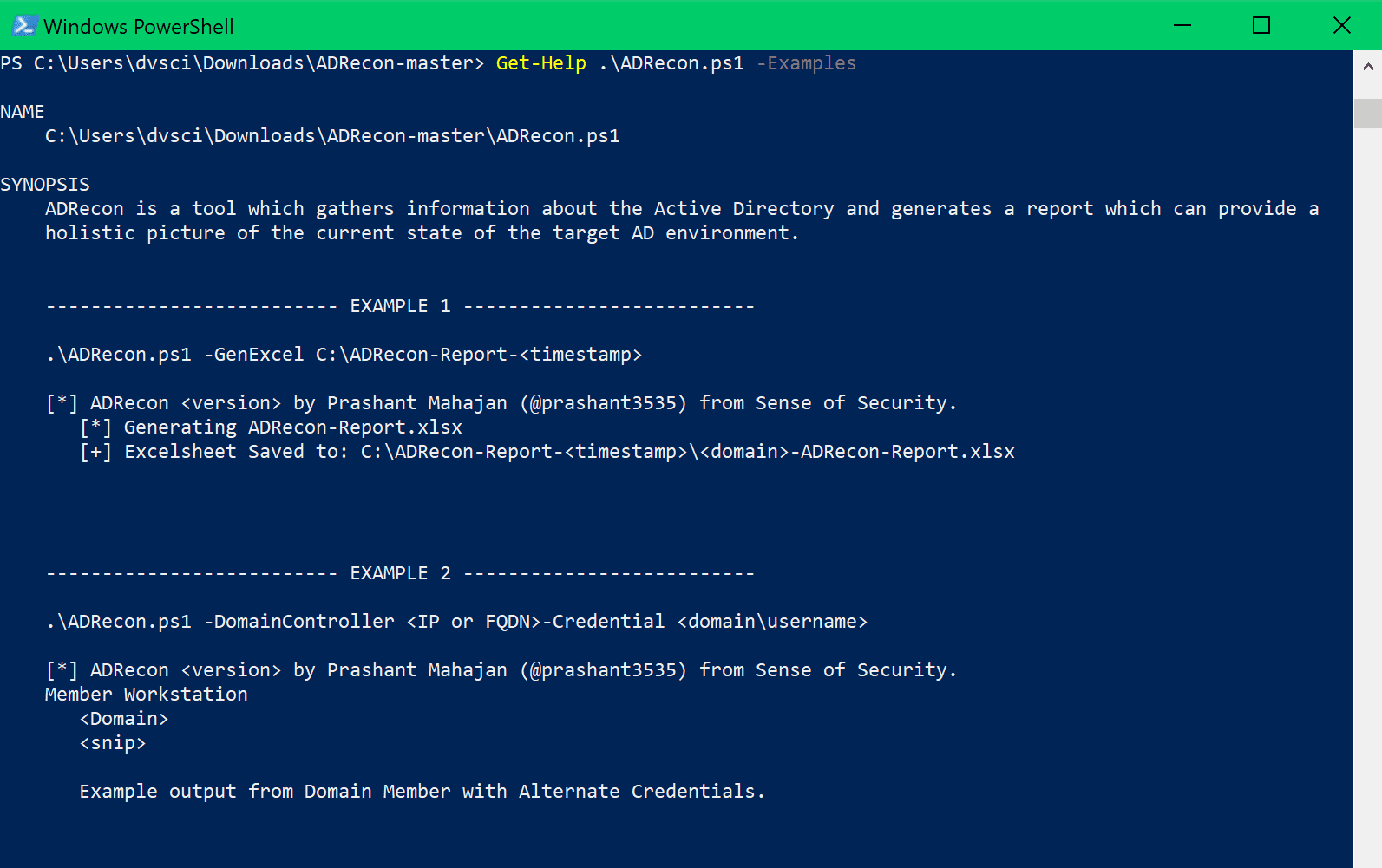
ADRecon is a tool which extracts and combines various artifacts (as highlighted below) out of an AD environment. The information can be presented in a specially formatted Microsoft Excel report that includes summary views with metrics to facilitate analysis and provide a holistic picture of the current state of the target AD environment.
The tool is used by various classes of security professionals like auditors, DFIR, students, administrators, etc. It can also be an invaluable post-exploitation tool for a penetration tester.
It can be run from any workstation that is connected to the environment, even hosts that are not domain members. Furthermore, the tool can be executed in the context of a non-privileged (i.e. standard domain user) account. Fine-Grained Password Policy, LAPS, and BitLocker may require Privileged user accounts. The tool will use Microsoft Remote Server Administration Tools (RSAT) if available, otherwise, it will communicate with the Domain Controller using LDAP.
The following information is gathered by the tool:
- Forest;
- Domain;
- Trusts;
- Sites;
- Subnets;
- Default Password Policy;
- Fine-Grained Password Policy (if implemented);
- Domain Controllers, SMB versions, whether SMB Signing is supported and FSMO roles;
- Users and their attributes;
- Service Principal Names (SPNs);
- Groups and memberships;
- Organizational Units (OUs);
- ACLs for the Domain, OUs, Root Containers and GroupPolicy objects;
- Group Policy Object details;
- DNS Zones and Records;
- Printers;
- Computers and their attributes;
- LAPS passwords (if implemented);
- BitLocker Recovery Keys (if implemented); and
- GPOReport (requires RSAT).
- Kerberoast (not included in the default collection method).
ADRecon was presented at: Black Hat Arsenal Asia 2018 & Black Hat Arsenal USA 2018
Installation
Requirement
Prerequisites
- .NET Framework 3.0 or later (Windows 7 includes 3.0)
- PowerShell 2.0 or later (Windows 7 includes 2.0)
Optional
- Microsoft Excel (to generate the report)
- Remote Server Administration Tools (RSAT):
- Windows 10 (https://www.microsoft.com/en-au/download/details.aspx?id=45520)
- Windows 7 (https://www.microsoft.com/en-au/download/details.aspx?id=7887)
Download
git clone https://github.com/sense-of-security/ADRecon.git
Usage
Examples
- To run ADRecon on a domain member host.PS C:\> .\ADRecon.ps1
- To run ADRecon on a domain member host as a different user.PS C:\>.\ADRecon.ps1 -DomainController <IP or FQDN> -Credential <domain\username>
- To run ADRecon on a non-member host using LDAP.PS C:\>.\ADRecon.ps1 -Protocol LDAP -DomainController <IP or FQDN> -Credential <domain\username>
- To run ADRecon with specific modules on a non-member host with RSAT.PS C:\>.\ADRecon.ps1 -Protocol ADWS -DomainController <IP or FQDN> -Credential <domain\username> -Collect Domian, DCs
- To generate the ADRecon-Report.xlsx based on ADRecon output.PS C:\>.\ADRecon.ps1 -GenExcel C:\ADRecon-Report-<timestamp>
When you run ADRecon, a ADRecon-Report-<timestamp> folder will be created which will contain ADRecon-Report.xlsx and CSV-Folder with the raw files.
Parameters
Copyright (C) Sense of Security






