On January 10, Apache
issued a security notice to fix a remote code execution vulnerability (CVE-2021-43297) in Dubbo. Due to a deserialization vulnerability in Dubbo’s hessian-lite, an unauthenticated attacker could exploit the
vulnerability to remotely execute arbitrary code on the target system. Most Dubbo users use Hessian2 as the serialization/deserialization protocol by default. When Hessian catches an exception, Hessian will log out some user information, which may lead to remote command execution.
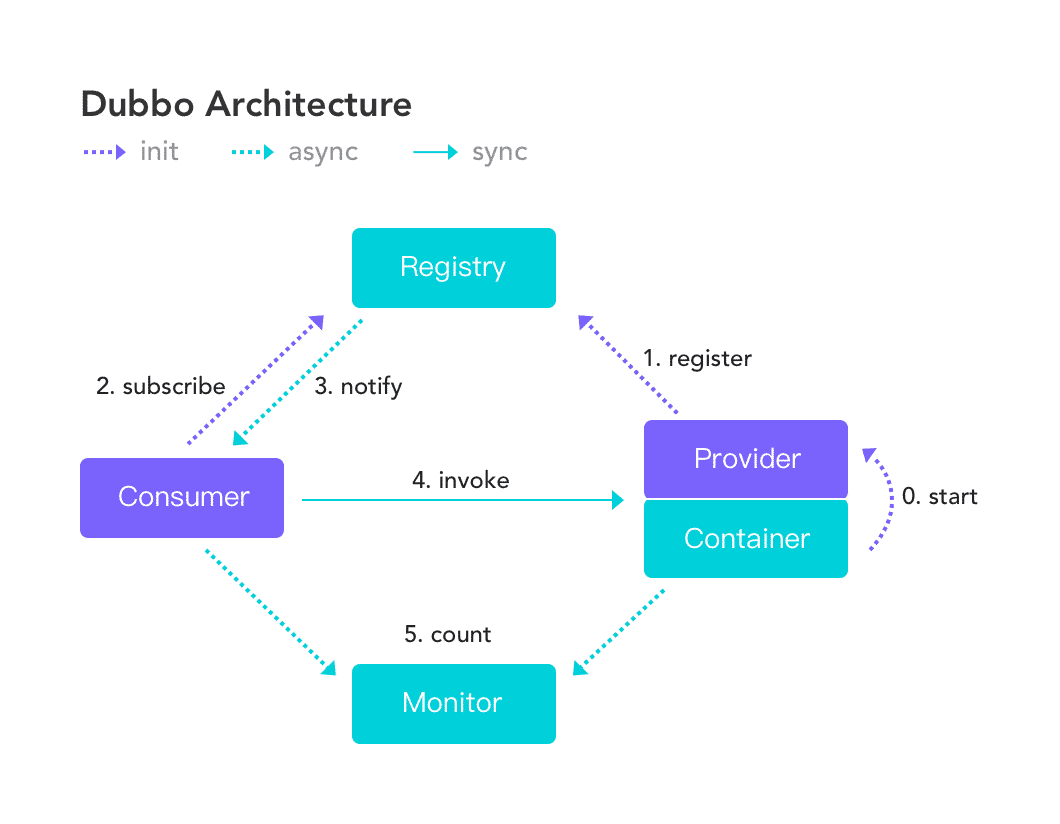
Apache Dubbo is a high-performance, Java-based open-source RPC framework. It offers six key functionalities, which include transparent interface-based RPC, intelligent load balancing, automatic service registration, and discovery, high extensibility, runtime traffic routing, and visualized service governance.
Affected version
- Apache Dubbo 2.6.x < 2.6.12
- Apache Dubbo 2.7.x < 2.7.15
- Apache Dubbo 3.0.x < 3.0.5
Unaffected version
- Apache Dubbo = 2.6.12
- Apache Dubbo = 2.7.15
- Apache Dubbo = 3.0.5
Solution
At present, Apache Dubbo has released a fixed version for the CVE-2021-43297 vulnerability. The user should upgrade Apache Dubbo to the unaffected version.
Mitigating method
-
Close the Dubbo server port open to the public network, and only allow trusted IP access.
-
The Dubbo protocol uses Hessian for serialization and deserialization by default. In the case of not affecting the system, it is recommended to replace the protocol and deserialization method.