Espionage – A Network Traffic Interceptor For Linux
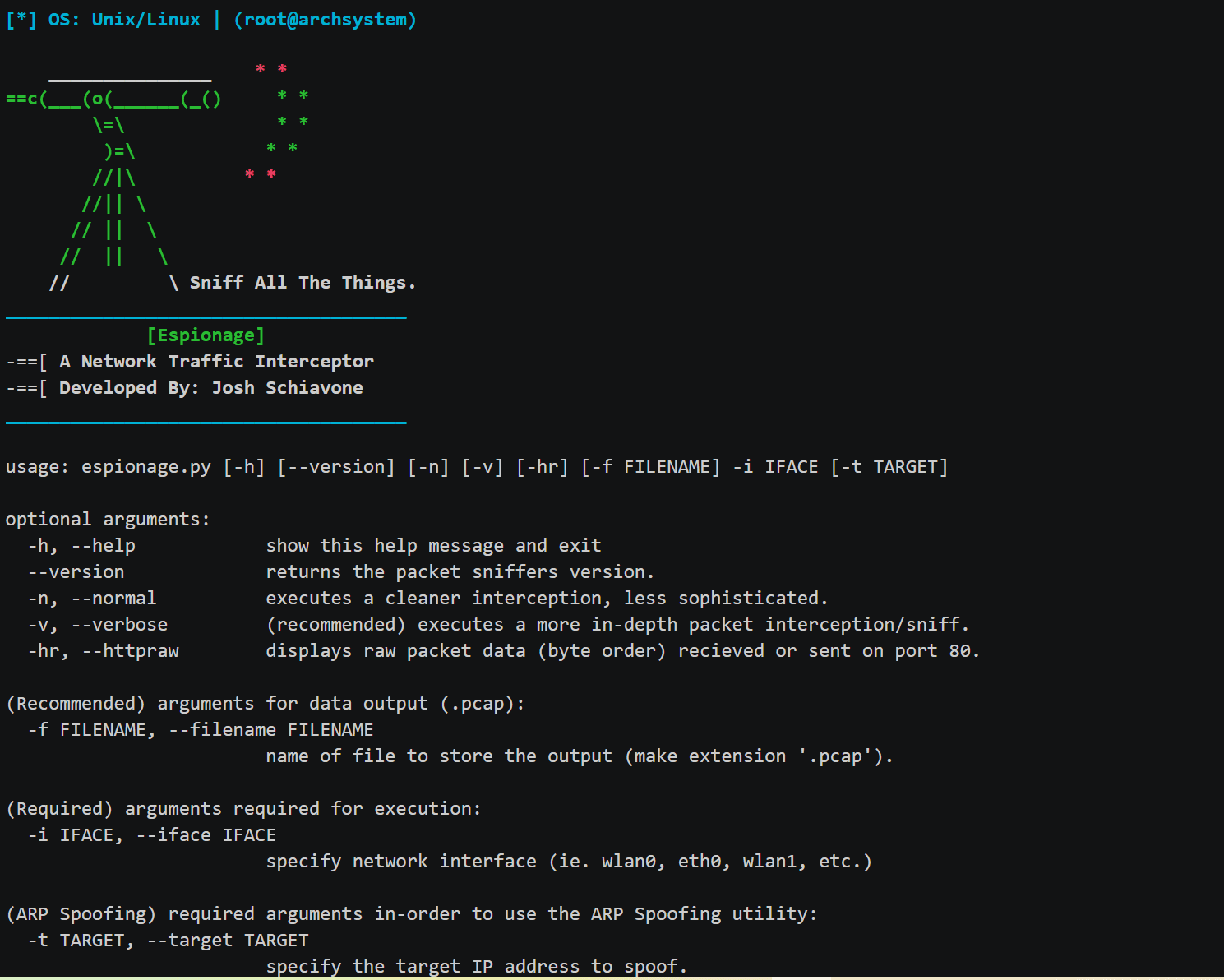
Espionage is a network packet sniffer that intercepts large amounts of data being passed through an interface. The tool allows users to run normal and verbose traffic analysis that shows a live feed of traffic, revealing packet direction, protocols, flags, etc. It can also spoof ARP so, all data sent by the target gets redirected through the attacker (MiTM). Espionage supports IPv4, TCP/UDP, ICMP, and HTTP. Scapy support is also available so users can run in-depth sniffs using the Scapy library. Espionage was written in Python 3.8 but it also supports version 3.6. This is the first version of the tool so please contact the developer if you want to help contribute and add more to Espionage.
Install
git clone https://www.github.com/josh0xA/Espionage.git
cd Espionage
sudo python3 -m pip install -r requirments.txt
Use
sudo python3 espionage.py --normal --iface wlan0 -f capture_output.pcap
Command 1 will execute a clean packet sniff and save the output to the pcap file provided. Replacewlan0with whatever your network interface is.sudo python3 espionage.py --verbose --iface wlan0 -f capture_output.pcap
Command 2 will execute a more detailed (verbose) packet sniff and save the output to the pcap file provided.sudo python3 espionage.py --normal --iface wlan0
Command 3 will still execute a clean packet sniff however, it will not save the data to a pcap file. Saving the sniff is recommended.sudo python3 espionage.py --verbose --httpraw --iface wlan0
Command 4 will execute a verbose packet sniff and will also show raw http/tcp packet data in bytes.sudo python3 espionage.py --target <target-ip-address> --iface wlan0
Command 5 will ARP spoof the target ip address and all data being sent will be routed back to the attackers’ machine (you/localhost).
- Press Ctrl+C in-order to stop the packet interception and write the output to file.
Copyright (c) 2020 Josh Schiavone
Source: https://github.com/josh0xA/