sparta 1.0.4 BETA releases: Network Infrastructure Penetration Testing Tool
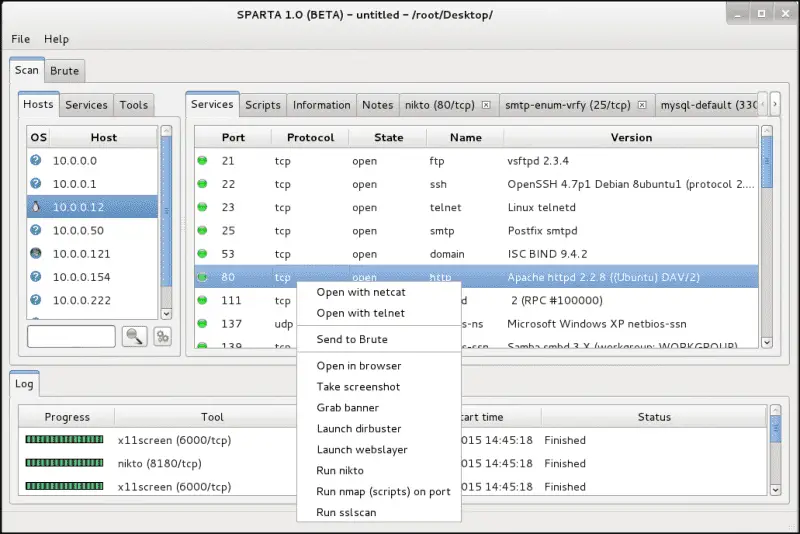
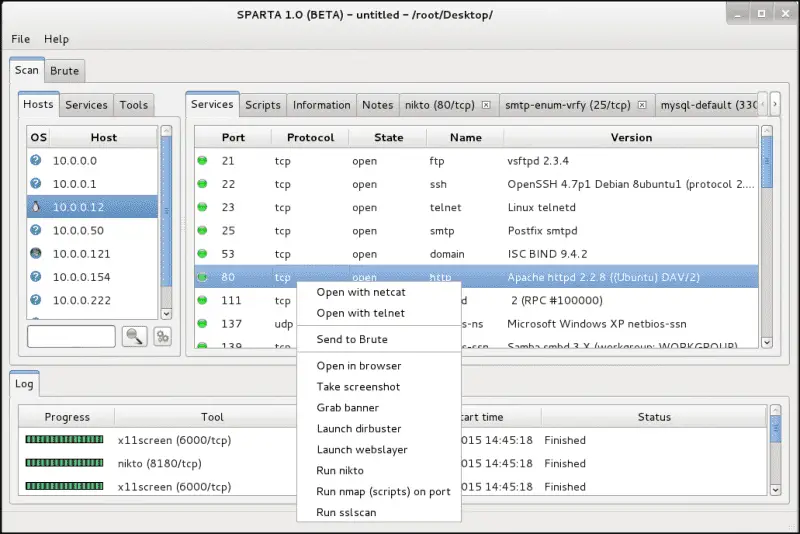
SPARTA is a python GUI application which simplifies network infrastructure penetration testing by aiding the penetration tester in the scanning and enumeration phase. It allows the tester to save time by having point-and-click access to his toolkit and by displaying all tool output in a convenient way. If little time is spent setting up commands and tools, more time can be spent focusing on analyzing results. Despite the automation capabilities, the commands and tools used are fully customizable as each tester has his own methods, habits, and preferences.
Features
– Run nmap from SPARTA or import nmap XML output.
– Transparent staged nmap: get results quickly and achieve thorough coverage.
– Configurable context menu for each service. You can configure what to run on discovered services. Any tool that can be run from a terminal, can be run from SPARTA.
– You can run any script or tool on a service across all the hosts in scope, just with a click of the mouse.
– Define automated tasks for services (ie. Run nikto on every HTTP service, or sslscan on every ssl service).
– Default credentials check for most common services. Of course, this can also be configured to run automatically.
– Identify password reuse on the tested infrastructure. If any usernames/passwords are found by Hydra they are stored in internal wordlists which can then be used on other targets in the same network (breaking news: sysadmins reuse passwords).
– Ability to mark hosts that you have already worked on so that you don’t waste time looking at them again.
– Website screenshot taker so that you don’t waste time on less interesting web servers.
Changelog
SPARTA 1.0.4 (BETA)
* removed QtWebKit dependency for displaying the help menu
* improved HTTPS/HTTP detection (experimental)
* removed MS08-067 check from smbenum.sh
Installation
Usage
Copyright (C) 2014






