Category: Vulnerability Analysis
Callisto An Intelligent Automated Binary Vulnerability Analysis Tool Callisto is an intelligent automated binary vulnerability analysis tool. Its purpose is to autonomously decompile a provided binary and iterate through the pseudo code output looking...
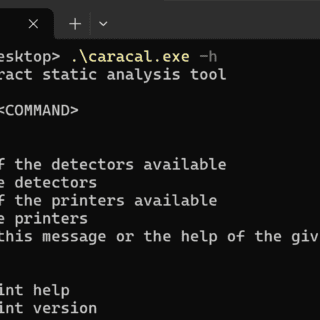
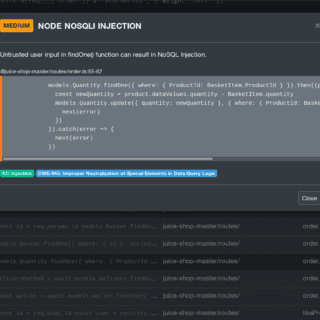
Caracal Caracal is a static analyzer tool over the SIERRA representation for Starknet smart contracts. Features Detectors to detect vulnerable Cairo code Printers to report information Taint analysis Data flow analysis framework Easy to...
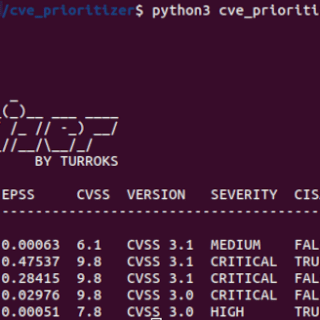
CVE Prioritizer Tool CVE_Prioritizer is a powerful tool that helps you prioritize vulnerability patching by combining CVSS, EPSS, and CISA’s Known Exploited Vulnerabilities. It provides valuable insights into the likelihood of exploitation and the potential impact of...
ADCSKiller – An ADCS Exploitation Automation Tool ADCSKiller is a Python-based tool designed to automate the process of discovering and exploiting Active Directory Certificate Services (ADCS) vulnerabilities. It leverages features of Certipy and Coercer...
Sirius Scan Sirius is the first truly open-source general purpose vulnerability scanner. Today, the information security community remains the best and most expedient source for cybersecurity intelligence. The community itself regularly outperforms commercial vendors....
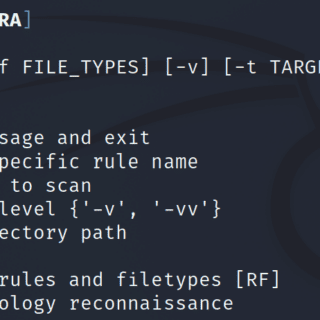
Daksh SCRA (Source Code Review Assist) The tool currently offers the following functionalities: Options to use programming language-specific rules specific for finding areas of interests Option to extend or add new rules for any...
IaC Scan Runner The IaC Scanner is an inspection service that aims to scan IaC (Infrastructure as Code) in order to find the problems and security vulnerabilities so that the users can improve their code....
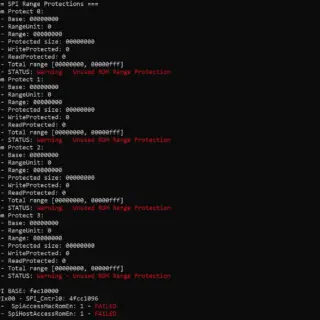
Platbox UEFI and SMM Assessment Tool Features Platbox is a tool that helps assessing the security of the platform: Dumps the platform registers that are interesting security-wise Flash Locks MMIO and Remapping Locks SMM...
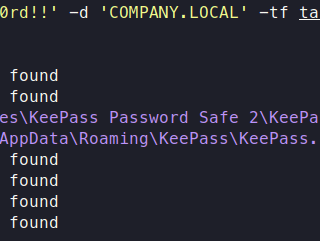
KeePwn A python script to help red teamers discover KeePass instances and extract secrets. Features & Roadmap KeePass Discovery Accept multiple target sources (IP, range, hostname, file) Automatically look for KeePass global installation files...
Kubestroyer Kubestroyer aims to exploit Kubernetes clusters misconfigurations and be the swiss army knife of your Kubernetes pentests. Kubestroyer is a Golang exploitation tool that aims to take advantage of Kubernetes clusters misconfigurations. The tool...
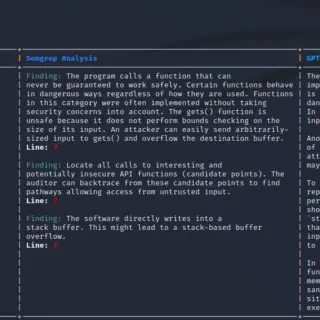
Grepmarx – source code static analysis platform for security auditors Grepmarx is a web application providing a single platform to quickly understand, analyze and identify vulnerabilities in possibly large and unknown code bases. Features...
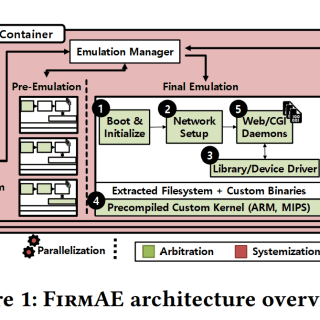
FirmAE FirmAE is a fully-automated framework that performs emulation and vulnerability analysis. FirmAE significantly increases the emulation success rate (From Firmadyne‘s 16.28% to 79.36%) with five arbitration techniques. We tested FirmAE on 1,124 wireless routers...
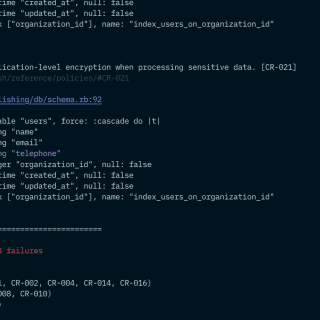
Bearer Bearer is a static application security testing (SAST) tool that scans your source code and analyzes your data flows to discover, filter and prioritize security risks and vulnerabilities leading to sensitive data exposures (PII, PHI, PD). We...
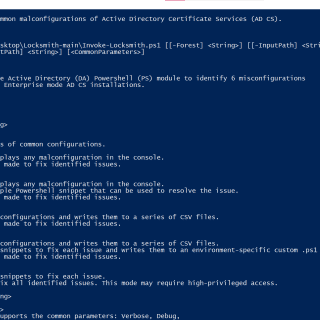
Locksmith A tiny tool to identify and remediate common misconfigurations in Active Directory Certificate Services. Mode 0 (Default) – Identify Issues and Output to Console PS> .\Invoke-Locksmith.ps1 Running Invoke-Locksmith.ps1 with no parameters or -Mode 0 will...
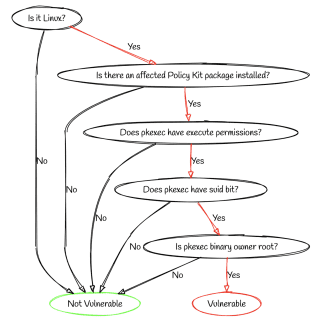
Am I Exploitable? ‘Am I Exploitable?’ is a python open source project that comes to meet the need of validating if your system is exploitable to specific vulnerabilities. The project can help you understand...