Category: Maintaining Access
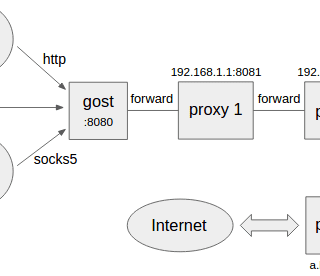
gost – GO Simple Tunnel Features Listening on multiple ports Multi-level forward proxies – proxy chain Standard HTTP/HTTPS/HTTP2/SOCKS4(A)/SOCKS5 proxy protocols support Probing resistance support for web proxy TLS encryption via negotiation support for SOCKS5...
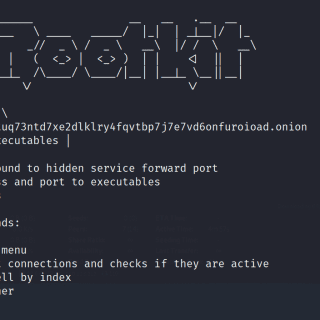
Tor Rootkit A Python 3 standalone Windows 10 / Linux Rootkit. The networking communication get’s established over the tor network. Features Standalone executable, including python interpreter and tor The executable has a size of...
SillyRAT A cross-platform RAT is written in pure Python. The RAT accepts commands alongside arguments to either perform as the server who accepts connections or to perform as the client/target who establishes connections to...
clash A rule-based tunnel in Go. Features Local HTTP/HTTPS/SOCKS server with authentication support VMess, Shadowsocks, Trojan, Snell protocol support for remote connections Built-in DNS server that aims to minimize DNS pollution attack impact, supports...
Azure Outlook C2 Azure Outlook Command & Control that uses Microsoft Graph API for C2 communications & data exfiltration. Remotely Control a compromised Windows Device from your Outlook Mailbox. This project consists of an...
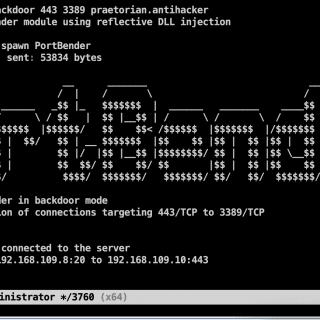
PortBender PortBender is a TCP port redirection utility that allows a red team operator to redirect inbound traffic destined for one TCP port (e.g., 445/TCP) to another TCP port (e.g., 8445/TCP). PortBender includes an...
The PyIris Project The PyIris project is a modular, stealthy and flexible remote-access-toolkit written completely in python. It allows users to dynamically build, generate, and encode/encrypt remote-access-trojan payloads for remote control of other compromised hosts....
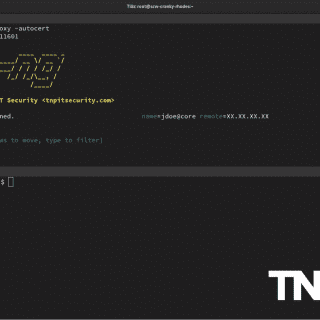
Ligolo-ng : Tunneling like a VPN An advanced, yet simple, tunneling tool that uses a TUN interface. Ligolo-ng is a simple, lightweight, and fast tool that allows pentesters to establish tunnels from a reverse TCP/TLS connection without the need of...
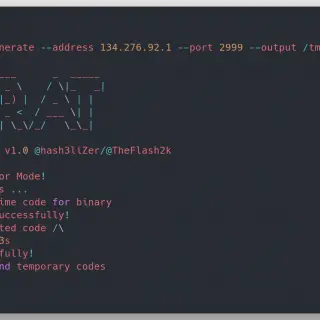
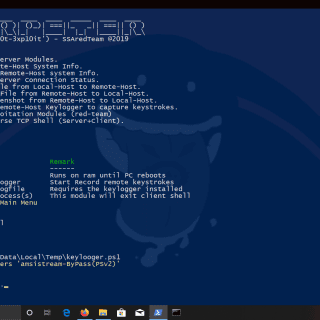
meterpeter meterpeter – This PS1 starts a listener Server on a Windows|Linux attacker machine and generates oneliner PS reverse shell payloads obfuscated in ANCII|BXOR with a random secret key and another layer of Characters/Variables...
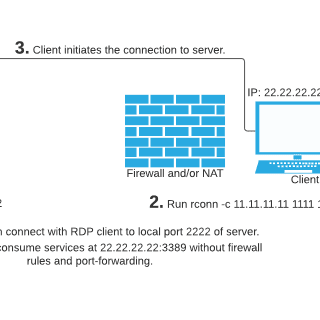
rconn (r[everse] conn[ection]) is a multiplatform program for creating reverse connections. It lets you consume behind NAT and/or firewall services without adding firewall rules or port-forwarding. This is achieved by creating a connection from...
Rustcat Rustcat is a port listener that can be used for different purposes. It is basically like netcat but with fewer options. Why use Rustcat? Serves it purpose of listening to ports It is...
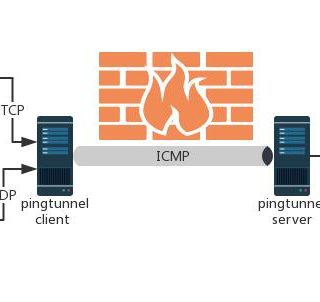
Pingtunnel Pingtunnel is a tool that advertises tcp/udp/sock5 traffic as icmp traffic for forwarding. Usage Install server First prepare a server with a public IP, such as EC2 on AWS, assuming the domain name...
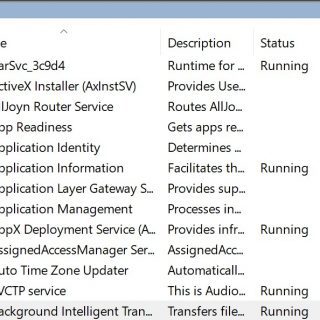
SHEPARD This is an IN PROGRESS persistent tool using Windows Background Intelligent Transfer Service (BITS). Functionality: File Download, File Exfiltration, File Download + Persistent Execution Usage: run shepard.exe as Administrator with the following command-line...
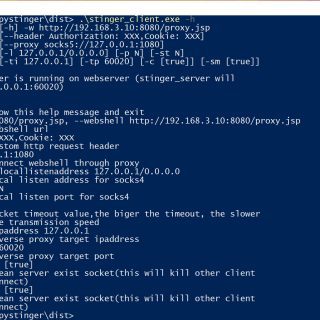
pystinger Pystinger implements SOCK4 proxy and port mapping through webshell. It can be directly used by Metasploit-framework, viper, cobalt strike for sessions online. Pystinger is developed in python, and currently supports three proxy scripts: php, jsp(x), and...
Project-Iroh Offensive Windows security tooling that allows for persistence to the operating system. Iroh provides a variety of different persistences and misconfigurations to the system with a couple of class calls. It also allows...